Abstract
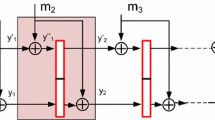
This paper reconsiders the established Merkle-Damgård design principle for iterated hash functions. The internal state size w of an iterated n-bit hash function is treated as a security parameter of its own right. In a formal model, we show that increasing w quantifiably improves security against certain attacks, even if the compression function fails to be collision resistant. We propose the wide-pipe hash, internally using a w-bit compression function, and the double-pipe hash, with w=2n and an n-bit compression function used twice in parallel.
Chapter PDF
Similar content being viewed by others
References
Biham, E., Chen, R., Joux, A., Carribault, P., Lemuet, C., Jalby, W.: Collisions of SHA-0 and reduced SHA-1. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 36–57. Springer, Heidelberg (2005)
Black, J., Rogaway, P., Shrimpton, T.: Black-box analysis of the block-cipher based hash-function construction from PGV. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, pp. 320–335. Springer, Heidelberg (2002)
Brickell, E., Pointcheval, D., Vaudenay, S., Yung, M.: Design validation for discrete logarithm based signature schemes. In: Imai, H., Zheng, Y. (eds.) PKC 2000. LNCS, vol. 1751, pp. 276–292. Springer, Heidelberg (2000)
Canetti, R., Goldreich, O., Halevi, S.: The random oracle methodology. In: 30th STOC, pp. 209–218 (1998) (revisited)
Coron, J., Dodis, Y., Malinaud, C., Punyia, P.: Merkle-Damgård revisited: how to construct a hash function. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 430–448. Springer, Heidelberg (2005)
Damgård, I.: A design principle for hash functions. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 416–427. Springer, Heidelberg (1990)
Daum, M., Lucks, S.: The story of Alice and her boss. Eurocrypt 05 rump session, http://th.informatik.uni-mannheim.de/people/lucks/HashCollisions/
Dobbertin, H., Bosselaers, A., Preneel, B.: RIPEMD-160, a strengthened version of RIPEMD. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, pp. 71–82. Springer, Heidelberg (1996), See also http://www.esat.kuleuven.ac.be/~bosselae/ripemd160.html
Finney, H.: More problems with hash functions. The cryptography mailing list (August 24, 2004), http://lists.virus.org/cryptography-0408/msg00124.html
Girault, M., Stern, J.: On the length of cryptographic hash-values used in identification schemes. In: Desmedt, Y.G. (ed.) CRYPTO 1994. LNCS, vol. 839, pp. 202–215. Springer, Heidelberg (1994)
Joux, A.: Multicollisions in iterated hash functions, application to cascaded constructions. In: Franklin, M. (ed.) CRYPTO 2004. LNCS, vol. 3152, pp. 306–316. Springer, Heidelberg (2004)
Kaminski, D.: MD5 to be considered harmful someday (December 2004), http://www.doxpara.com/md5_someday.pdf
Kelsey, J., Schneier, B.: Second preimages on n-bit hash functions in much less than 2n work. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 474–490. Springer, Heidelberg (2005)
Lenstra, A., de Weger, B.: On the possibility of constructing meaningful hash collisions for public keys. In: Boyd, C., González Nieto, J.M. (eds.) ACISP 2005. LNCS, vol. 3574, pp. 267–279. Springer, Heidelberg (2005) (to appear)
Lenstra, A., de Weger, B., Wang, X.: Colliding X.509 certificates. Cryptology eprint archive report (2005), /067., http://eprint.iacr.org/2005/067/
Merkle, R.: One-way hash functions and DES. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 428–446. Springer, Heidelberg (1990)
Mikle, O.: Practical attacks on digital signatures using MD5 message digest. Cryptology eprint archive report 2004/356, http://eprint.iacr.org/2004/356/
Nandi, M., Lee, W., Sakurai, K., Lee, S.: Security analysis of a 2/3-rate double length compression function in the black box model. In: Gilbert, H., Handschuh, H. (eds.) FSE 2005. LNCS, vol. 3557, pp. 243–254. Springer, Heidelberg (2005)
National Institute of Standards and Technology (NIST). Secure hash standard. FIPS 180-2 (August 2002)
Preneel, B.: Analysis and design of cryptographic hash functions. PhD thesis, Katholieke Universiteit Leuven (1993)
Preneel, B.: Private communication. In: Hash Function Workshop, Krakow (2005)
Bosselaers, A., Preneel, B. (eds.): RIPE 1992. LNCS, vol. 1007. Springer, Heidelberg (1995)
Rivest, R., Shamir, A.: PayWord and MicroMint – two simple micropayment schemes. CryptoBytes 2(1), 7–11 (1996)
Rogaway, P., Shrimpton, T.: Cryptographic Hash-Function Basics: Definitions, Implications, and Separations for Preimage Resistance, Second-Preimage Resistance, and Collision-Resistance. In: Roy, B., Meier, W. (eds.) FSE 2004. LNCS, vol. 3017, pp. 371–388. Springer, Heidelberg (2004)
Wang, X., Lai, X., Feng, D., Cheng, H., Yu, X.: Cryptoanalyisis of the hash functions MD4 and RIPEMD. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 1–18. Springer, Heidelberg (2005)
Wang, X., Yu, H.: How to break MD5 and other hash functions. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 19–35. Springer, Heidelberg (2005)
Wang, X., Yu, H., Yin, Y.L.: Efficient collision search attacks on SHA0. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 1–16. Springer, Heidelberg (2005)
Wang, X., Yin, Y.L., Yu, H.: Finding collisions in the full SHA1. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 17–36. Springer, Heidelberg (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Lucks, S. (2005). A Failure-Friendly Design Principle for Hash Functions. In: Roy, B. (eds) Advances in Cryptology - ASIACRYPT 2005. ASIACRYPT 2005. Lecture Notes in Computer Science, vol 3788. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11593447_26
Download citation
DOI: https://doi.org/10.1007/11593447_26
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-30684-9
Online ISBN: 978-3-540-32267-2
eBook Packages: Computer ScienceComputer Science (R0)