Abstract
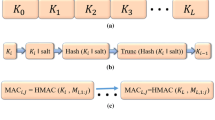
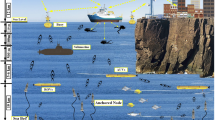
The maritime wideband communication network, which extends the operation of wireless access from land to sea, will significantly contribute to the maritime distress, urgency, safety, and general communications. The Worldwide Interoperability for Microwave Access (WiMAX) technology has been applied to establish a maritime wideband shore-side network infrastructure, to achieve large capacity data backhauls. However, in this scenario, many new security and privacy challenges are arising, e.g., the reduced time overhead for group access authentication due to limited time window vessels passing by infostations along the shore-side. In this paper, a simple and reliable group authentication framework is developed for dealing with security issues in this special maritime wideband communication scenario. Specifically, an efficient authentication protocol for secure group communications (EAPSG) in maritime wideband communication network is proposed based on the Elliptic Curve Diffie-Hellman (ECDH), to overcome the weakness existing in the prevailing protocols on land, i.e., user identity disclosure, the lack of perfect forward secrecy, and man-in-the-middle attacks. Meanwhile, EAPSG can reduce the communication overhead and computational complexity by designing group access authentication procedures. Compared with conventional EAP-AKA protocol used in WiMAX networks on land, our scheme enhances the security and provides better performance. Especially, the security of the proposed protocol was verified by Automated Validation of Internet Security Protocols and Applications (AVISPA), and detailed performance evaluations are also given. The results illustrate that the proposed EAPSG outperforms other existing schemes on land in terms of the delivery cost and the number of signaling messages.







Similar content being viewed by others
Notes
We use the term of vessel and ship interchangeably.
References
Sharda (2011) What is a group of ships called? http://www.marineinsight.com/marine/marine-piracy-marine/10-maritime-piracy-affected-areas-around-the-world/
Yang T, Liang H, Cheng N, Shen X (2013) Towards video packets store-carry-and-forward scheduling in maritime wideband communication. accepted by IEEE GLOBECOM’13
Maglogiannis I, Hadjiefthymiades S, Panagiotarakis N, Hartigan P (2005) Next generation maritime communication systems. Int J Mob Commun 3(3):231–248
Mitropoulos E (2007) E-navigation: a global resource. seaways. In: The international journal of the nautical institute
Zhou M-T, Harada H (2012) Cognitive maritime wireless mesh/ad hoc networks. J Netw Comput Appl 35(2):518–526
Cellular-news (2008) Maritime WiMAX network launched in Singapore. http://www.cellular-news.com/story/29749.php
Hoang VD, Ma M, Miura R, Fujise M (2007) A novel way for handover in maritime WiMAX mesh network. In: Proceedings of IEEE ITST, pp 1–4
Funk P, Blake-Wilson S (2008) Extensible authentication protocol tunneled transport layer security authenticated protocol version 0 (EAP-TTLSv0). In: RFC5281
Palekar A, Simon D, Zorn G, Josefsson S (2004) Protected EAP protocol (PEAP). In: Work in Progress
Yuan G, ZHU K, FANG N-s, WU G-x (2006) Research and application of 802.1 x/EAP-PEAP. Comput Eng Des 10:34
Dantu R, Clothier G, Atri A (2007) EAP methods for wireless networks. Comput Stand Interfaces 29(3):289–301
Pereniguez F, Kambourakis G, Marin-Lopez R, Gritzalis S, Gomez A (2010) Privacy-enhanced fast re-authentication for EAP-based next generation network. Comput Commun 33(14):1682–1694
Marin-Lopez R, Pereniguez F, Bernal F, Gomez A (2010) Secure three-party key distribution protocol for fast network access in EAP-based wireless networks. Comput Netw 54(15):2651–2673
Marin-Lopez R, Ohba Y, Pereniguez F, Gomez AF (2010) Analysis of handover key management schemes under IETF perspective. Comput Stand Interfaces 32(5):266–273
Al Shidhani AA, Leung VC (2011) Fast and secure reauthentications for 3GPP subscribers during WiMAX-WLAN handovers. IEEE Trans Dependable Secure Comput 8(5):699–713
Jiang R, Luo J, Wang X (2013) HRKT: a hierarchical route key tree based group key management for wireless sensor networks. KSII Trans Internet Inf Syst (TIIS) 7(8):2042–2060
Ngo HH, Wu X, Le PD, Srinivasan B (2010) An individual and group authentication model for wireless network services. J Converg Inf Technol 5(1):82–94
Chen Y-W, Wang J-T, Chi K-H, Tseng C-C (2012) Group-based authentication and key agreement. Wirel Pers Commun 62(4):965–979
Aboudagga N, Quisquater J-J, Eltoweissy M (2007) Group authentication protocol for mobile networks. In: Proceeding of IEEE WiMOB, pp 28–28
Lai C, Li H, Li X, Cao J (2013) A novel group access authentication and key agreement protocol for machine-type communication. In: Transactions on emerging telecommunications technologies
Jiang R, Lai C, Luo J, Wang X, Wang H (2013) EAP-based group authentication and key agreement protocol for machine-type communications. Int J Distrib Sensor Net 2013(2013):1–14
Lai C, Li H, Lu R, Shen XS (2013) SE-AKA: a secure and efficient group authentication and key agreement protocol for lte networks. Comput Netw 57(17):3492–3510
Lai C, Li H, Lu R, Jiang R, Shen XS (2013) LGTH: a lightweight group authentication protocol for machine-type communication in LTE networks. In: Proceedings of IEEE Globecom
Lu R, Liang X, Li X, Lin X, Shen X (2012) EPPA: an efficient and privacy-preserving aggregation scheme for secure smart grid communications. IEEE Trans Parallel Distrib Syst 23(9):1621–1631
Avispaautomated validation of internet security protocols. http://www.avispa-project.org
Author information
Authors and Affiliations
Corresponding author
Appendix
Appendix
The formal security verification code is described as follow:

Rights and permissions
About this article
Cite this article
Yang, T., Lai, C., Lu, R. et al. EAPSG: Efficient authentication protocol for secure group communications in maritime wideband communication networks. Peer-to-Peer Netw. Appl. 8, 216–228 (2015). https://doi.org/10.1007/s12083-014-0251-9
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-014-0251-9