Abstract.
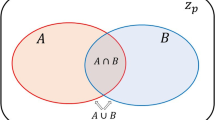
Traditional secret sharing schemes involve the use of a mutually trusted authority to assist in the generation and distribution of shares that will allow a secret to be protected among a set of participants. In contrast, this paper addresses the problem of establishing secret sharing schemes for a given access structure without the use of a mutually trusted authority. A general protocol is discussed and several implementations of this protocol are presented. Several efficiency measures are proposed and we consider how to refine the general protocol in order to improve the efficiency with respect to each of the proposed measures. Special attention is given to mutually trusted authority-free threshold schemes. Constructions are presented for such threshold schemes that are shown to be optimal with respect to each of the proposed efficiency measures.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
Author information
Authors and Affiliations
Additional information
Received 13 September 1995 and revised 10 April 1996
Rights and permissions
About this article
Cite this article
Jackson, WA., M. Martin, K. & M. O'Keefe, C. Mutually Trusted Authority-Free Secret Sharing Schemes . J. Cryptology 10, 261–289 (1997). https://doi.org/10.1007/s001459900031
Published:
Issue Date:
DOI: https://doi.org/10.1007/s001459900031