Abstract
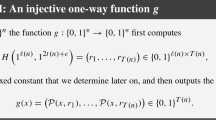
For many cryptographic primitives, e.g., hashing and pseudorandom functions & generators, doubling the output length is useful even if the doubling transformation is not reversible. For these cases, we present a non-reversible construction based on a Benes network, as an alternative to the traditional Feistel construction (which is the basis of DES).
Assuming that a given primitive behaves like an n-bit to n-bit random function, we present a length-doubling scheme that yields a 2n-bit to 2n-bit function that provably requires Ω(2n) queries to distinguish with Θ(1) probability from a truly random function of that length. This is true even if the adversary is of unlimited computing power and is allowed to query the function adaptively. Our construction is minimal in the sense that omitting any operation makes the resulting network susceptible to birthday attacks using O(2n/2) queries.
Feistel networks also use truly random n-bit functions to achieve 2n-bit functions. Luby and Rackoff [16] showed that 3 and 4 round Feistel networks require Ω(2n/2) queries to distinguish with Θ(1) probability from truly random. We show that these bounds are tight by showing that these networks are susceptible various types of birthday attacks using O(2n/2) queries.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
M. Bellare, R. Canetti, and H. Krawcyk, “Keying MD5 — Message Authentication via Iterated Pseudorandomness,” manuscript.
M. Bellare, J. Kilian, and P. Rogaway, “The Security of Cipher Block Chaining,” Advances in Cryptology-Crypto’ 94, Springer Verlag (1994).
E. Biham and A. Shamir, Differential Cryptanalysis of the Data Encryption Standard, Springer Verlag (1993).
E. Biham and A. Shamir, “Differential Cryptanalysis of Snefru, Khafre, REDOC II, LOKI, Lucifer,” Advances in Cryptology Crypto’ 91, Springer Verlag (1992).
E. Biham and A. Shamir, “Differential Cryptanalysis of Feal and N-hash”, Advances in Cryptology Eurocrypt’ 91, Springer Verlag (1991).
M. Blum and S. Micali, “How to Generate Cryptographically Strong Sequences of Pseudorandom Bits,” SIAM Journal on Computing, 13 pp. 850–864 (1984).
D. Coppersmith, “Another Birthday Attack,” Advances in Cryptology-Crypto’ 85, Springer Verlag (1986).
I. Damgard, “A Design Principle for Hash Functions,” Advances in Cryptology-Crypto’ 89, Springer Verlag (1989).
D. Davies and W. Price, Security for Computer Networks (2e), John Wiley (1989).
H. Dobbertin, “Cryptanalysis of MD4,” To appear at the Fast Software Encryption Workshop, February, 1996.
O. Goldreich, S. Goldwasser, and S. Micali, “How To Construct Random Functions,” JACM, 33,4, pp. 792–807 (1986).
J. Hastad, R. Impagliazzo, L. Levin, and M. Luby, “Pseudorandom Generation From One-Way Functions,” Proc. ACM Symp. on Theory of Computing, (1989); “Pseudorandom Generators Under Uniform Assumptions,” Proc. of the ACM Symp. on Theory of Computing (1990)
S. Langford and M. Hellman, “Differential-Linear Cryptanalysis,” Advances in Cryptology-Crypto’ 94, Springer Verlag (1994).
L. Levin, “One-Way Functions and Pseudo-Random Generators,” Proc. of the ACM Symp. on Theory of Computing (1985).
M. Luby, Pseudorandomness And Its Cryptographic Applications, Princeton Univ. Press, to appear.
M. Luby and C. Rackoff, “How to Construct Pseudorandom Permutations from Pseudorandom Functions,” SIAM Journal on Computing, 17, 373–386 (1988).
U. Maurer, “A Simplified and Generalized Treatment of Luby-Rackoff Pseudo-Random Permutation Generators,” Advances in Cryptology-Eurocrypt’ 92, Springer Verlag (1992).
M. Matsui, “The First Experimental Cryptanalysis of the Data Encryption Standard,” Advances in Cryptology-Crypto’ 94, Springer Verlag (1994).
R. Merkle, “A Fast in Software One-Way Hash Function,” Journal of Cryptology, 3,1, pp. 43–58 (1990).
R. Merkle, “One-Way Hash Functions and DES,” Advances in Cryptology-Crypto’ 89, Springer Verlag (1989).
P. van Oorschot and M. Wiener, “Parallel Collision Search with Application to Hash Functions and Discrete Logarithms,” Proc. of the 2nd ACM Conf. on Computer and Communications Security, (1994).
B. Prencel, Analysis and Design of Cryptographic Hash Functions, Ph.D Thesis, Katholieke Universiteit Leuven (1993).
B. Preneel, and P. van Oorschot, “MDx-MAC and Building Fast MACs from Hash Functions,” Advances in Cryptology-Crypto’ 95, Springer Verlag (1995).
V. Shoup, personal communication (1995).
A. Wyner, “The Wire-Tap Channel,” Bell System Technical Journal, 54 (1975).
A. Yao, “Theory and Applications of Trapdoor Functions,” Proc. of the IEEE Symp. on Foundations of Computer Science, (1982).
Y. Zheng, T. Matsumoto, and H. Imai, “On the Construction of Block Ciphers Provably Secure and Not Relying on Any Unproved Hypotheses,” Advances in Cryptology-Crypto’ 89 (1989).
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1996 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Aiello, W., Venkatesan, R. (1996). Foiling Birthday Attacks in Length-Doubling Transformations. In: Maurer, U. (eds) Advances in Cryptology — EUROCRYPT ’96. EUROCRYPT 1996. Lecture Notes in Computer Science, vol 1070. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-68339-9_27
Download citation
DOI: https://doi.org/10.1007/3-540-68339-9_27
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-61186-8
Online ISBN: 978-3-540-68339-1
eBook Packages: Springer Book Archive