Abstract
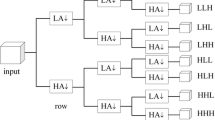
The recent advent in the multimedia tools and their wide availability lead to a critical issue of protecting the privacy of multimedia content in cyber-physical security of industrial set-ups predominantly in surveillance. This paper emphasizes on preserving the authenticity of multimedia content in industrial surveillance by presenting an efficient hashing technique based on normalization, log-polar mapping and singular value decomposition. The core idea is to produce a hash sequence from the key-frames extracted from industrial surveillance video providing better robustness and security. For this purpose, the input key-frame is first normalized to make it resilient against the affine distortions. Log-polar mapping is then applied on the normalized key-frame, and an initial hash sequence is generated using the properties of singular value decomposition. At last, a randomization process is applied to construct the final hash sequence. Extensive experiments on various key-frames are conducted to demonstrate the robustness of the proposed framework against various intentional/unintentional distortions.








Similar content being viewed by others
References
Andrews H, Patterson C (1976) Singular value decompositions and digital image processing. IEEE Trans Acoust Speech Signal Process 24:26–53
Basanta-Val P (2018) An efficient industrial big-data engine. IEEE Trans Ind Inf 14(4):1361–1369
Dong P, Brankov JG, Galatsanos NP, Yang Y, Davoine F (2005) Digital watermarking robust to geometric distortions. IEEE Trans Image Process 14:2140–2150
Du L, Ho ATS, Cong R (2020) Perceptual hashing for image authentication: a survey. Signal Process Image Commun 81:115713
Hernandez RAP, Miyatake MN, Kurkoski BM (2004) Robust image hashing using image normalization and svd decomposition. In: IEEE international midwest symposium on circuits and systems, pp 1–4
Kozat SS, Venkatesan R, Mihcak MK (2004) Robust perceptual image hashing via matrix invariants. Int Conf Image Process 5:3443–3446
Menezes AJ, Oorschot PCV, Vanstone SA (1996) Handbook of applied cryptography. CRC, Oxford
Monga V, Evans BL (2006) Perceptual image hashing via feature points: performance evaluation and tradeoffs. IEEE Trans Image Process 15(11):3452–3465
Monga V, Mihcak MK (2006) Robust image hashing via non-negative matrix factorizations. IEEE Int Conf Acoust Speech Signal Process 2:225–228
Neelima A, Singh M (2016) Perceptual hash function based on scale-invariant feature transform and singular value decomposition. Comput J 59:1275–1281
Ouyang J, Wen X, Liu J, Chen J (2016) Robust hashing based on quaternion zernike moments for image authentication. ACM Trans Multimedia Comput Commun Appl 12(4s):63:1-63:13
Ouyang J, Zhang X, Wen X (2020) Robust hashing based on quaternion gyrator transform for image authentication. IEEE Access 8:220585–220594
Qin C, Chang CC, Tsou PL (2013) Robust image hashing using non-uniform sampling in discrete Fourier domain. Digit Signal Process 23:578–585
Sajjad M, Haq IU, Lloret J, Ding W, Muhammad K (2019) Robust image hashing based efficient authentication for smart industrial environment. IEEE Trans Ind Inf 15(12):6541–6550
Singh SP, Bhatnagar G (2017) A robust image hashing based on discrete wavelet transform. In: IEEE international conference on signal and image processing applications (ICSIPA), pp 440–444
Singh SP, Bhatnagar G, Singh AK (2021) A new robust reference image hashing system. IEEE Trans Depend Secure Comput
Tang ZJ, Zhang XQ, Dai YM, Lan WW (2013) Perceptual image hashing using local entropies and DWT. Imaging Sci J 61:241–251
Tang Z, Yu Y, Zhang H, Yu M, Yu C, Zhang X (2019) Robust image hashing via visual attention model and ring partition. Math Biosci Eng 16(5):6103–6120
Tang Z, Zhang H, Pun C-M, Yu M, Yu C, Zhang X (2020) Robust image hashing with visual attention model and invariant moments. IET Image Proc 14:901–908
VIRAT video dataset, https://viratdata.org/
Wang D, Song G, Tan X (2019) Bayesian denoising hashing for robust image retrieval. Pattern Recogn 86:134–142
Wu L, Zhang J, Deng W, He D (2009) Arnold transformation algorithm and anti-arnold transformation algorithm. In: Proceedings IEEE international conference on information science and engineering, Nanjing, China, pp 1164–1167
Xiang S, Kim H, Huang J (2007) Histogram-based image hashing scheme robust against geometric deformations. In: ACM workshop on multimedia and security, pp 121–128
Yan C-P, Pun C-M, Yuan X-C (2016) Multi-scale image hashing using adaptive local feature extraction for robust tampering detection. Signal Process 121:1–16
Young D (2000) Straight lines and circles in the log-polar image. In: Proceedings of British machine vision conference, pp 426–435
Zhao Y, Liu S (2021) Image hashing algorithm based on mirror flipping and a three-dimensional space angle. Wirel Commun Mob Comput 2021:5349672-1–5349672-16
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Singh, S.P., Bhatnagar, G. Robust and efficient hashing framework for industrial surveillance. J Ambient Intell Human Comput 14, 4757–4769 (2023). https://doi.org/10.1007/s12652-022-04408-5
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12652-022-04408-5