Abstract
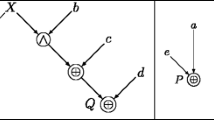
Linear cryptanalysis and linear approximation methods in general are among the most important cryptanalysis methods of symmetric ciphers and their components. Recently, these methods have been extended to efficiently exploit multiple linear approximations simultaneously. It is known that high nonlinearity of Boolean functions and S-boxes is a desirable property and that the bent functions offer the strongest resistance against cryptanalysis using single linear approximations. The goal of this paper is to investigate to which extent resistance against the multidimensional extension of the linear cryptanalysis method can be achieved. For this purpose some common highly nonlinear Boolean functions as well as a basic LFSR based key stream generator using a nonlinear filter function are investigated.
Similar content being viewed by others
References
Matsui, M.: Linear cryptanalysis method for des cipher. In: Helleseth, T. (ed.) Advances in Cryptology – EUROCRYPT’93. Workshop on the Theory and Application of Cryptographic Techniques Lofthus, Norway, 23–27 May 1993. Proceedings, vol. 765 of Lecture Notes in Computer Science, pp. 386–397. Springer, Berlin (1994)
Burton S., Kaliski, J., Robshaw, M.J.B.: Linear cryptanalysis using multiple approximations. In: Desmedt, Y.G. (ed.) Advances in Cryptology – CRYPTO ’94. 14th Annual International Cryptology Conference Santa Barbara, California, USA 21–25 August 1994. Proceedings, vol. 839 of Lecture Notes in Computer Science, pp. 26–39. Springer, Berlin (1994)
Biryukov, A., Cannière, C.D., Quisquater, M.: On multiple linear approximations. In: Franklin, M. (ed.) Advances in Cryptology – CRYPTO ’04. 24th Annual International Cryptology Conference, Santa Barbara, California, USA, 15–19 August 2004. Proceedings, vol. 3152 of Lecture Notes in Computer Science, pp. 1–22. Springer, Berlin (2004)
Englund, H., Maximov, A.: Attack the dragon. In: Maitra, S., Madhavan, C.V. (eds.) Progress in Cryptology – INDOCRYPT ’05. 6th International Conference on Cryptology in India, Bangalore, India, 10–12 December 2005. Proceedings, vol. 3797 of Lecture Notes in Computer Science, pp. 130–142. Springer, Berlin (2005)
Baignères, T., Junod, P., Vaudenay, S.: How far can we go beyond linear cryptanalysis? In: Lee, P.J. (ed.) Advances in Cryptology – ASIACRYPT ’04. 10th International Conference on the Theory and Application of Cryptology and Information Security, Jeju Island, Korea, 5–9 December 2004. Proceedings, vol. 3329 of Lecture Notes in Computer Science, pp. 432–450. Springer, Berlin (2004)
Hermelin, M., Nyberg, K., Cho, J.Y.: Multidimensional linear cryptanalysis of reduced round serpent. In: Mu, Y., Willy Susilo, J.S. (ed.) Information Security and Privacy, 13th Australasian Conference, ACISP 2008, Wollongong, Australia, 7–9 July 2008. Proceedings, vol. 5107 of Lecture Notes in Computer Science, pp. 203–215. Springer, Berlin (2008)
Hermelin, M., Cho, J.Y., Nyberg, K.: Multidimensional extension of Matsui’s Algorithm 2. In: Dunkelman, O. (ed.) Fast Software Encryption, 16th International Workshop, FSE 2009 Leuven, Belgium, 22–25 February 2009 Revised Selected Papers, vol. 5665 of Lecture Notes in Computer Science, pp. 209–227. Springer, Berlin (2009)
Molland, H., Helleseth, T.: An improved correlation attack against irregular clocked and filtered keystream generators. In: Franklin, M. (ed.) Advances in Cryptology-CRYPTO 2004, vol. 3152 of Lecture Notes in Computer Science, pp. 373–389. Springer, Berlin (2004)
Cramér, H., Wold, H.: Some theorems on distribution functions. J. London Math. Soc. s1-11(4), 290–295 (1936)
Murphy, S.: The independence of linear approximations in symmetric cryptology. IEEE Trans. Inf. Theory 52(12), 5510–5518 (2006)
Ekdahl, P., Johansson, T.: A new version of the stream cipher snow. In: Nyberg, K., Heys, H. (eds.) 9th Annual International Workshop, SAC 2002 St. John’s, Newfoundland, Canada, 15–16 August 2002, vol. 2595 of Lecture Notes in Computer Science, pp. 47–61. Springer, Berlin (2003)
Nyberg, K., Wallén, J.: Improved linear distinguishers for SNOW 2.0. In: Robshaw, M. (ed.) Fast Software Encryption, 13th International Workshop, FSE 2006, Graz, Austria, 15–17 March 2006, Revised Selected Papers, vol. 4047 of Lecture Notes in Computer Science, pp. 144–162. Springer, Berlin (2006)
Nyberg, K.: Correlation theorems in cryptanalysis. Discrete Appl. Math. 111(1–2), 177–188 (2001)
Zheng, Y., Zhang, X.M.: Plateaued functions. In: Varadharajan, V., Mu, Y. (eds.) Information and Communication Security Second International Conference, ICICS’99, Sydney, Australia, 9–11 November 1999. Proceedings, vol. 1726 of Lecture Notes in Computer Science, pp. 284–300. Springer, Berlin (2004)
Acknowledgements
We thank Gregor Leander for noticing a problem in the original version of Theorem 4.3 and for proposing a new elegant solution. We also thank Anne Canteaut for her comments and suggestion to investigate plateaued filter functions. Last but least we thank the anonymous referees for their insightful comments and help in improving the presentation of the paper. Financial support from Matine project number 776 is gratefully acknowledged.
Author information
Authors and Affiliations
Corresponding author
Additional information
Preliminary version appeared in the proceedings of BFCA’08 International Workshop on Boolean Functions: Cryptography and Applications.
Rights and permissions
About this article
Cite this article
Hermelin, M., Nyberg, K. Multidimensional linear distinguishing attacks and Boolean functions. Cryptogr. Commun. 4, 47–64 (2012). https://doi.org/10.1007/s12095-011-0053-3
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12095-011-0053-3
Keywords
- Linear approximation
- Multidimensional linear approximation
- Distinguishing attack
- Boolean function
- Filter generator