Abstract
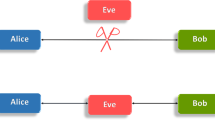
To achieve unconditional security through quantum key distribution (QKD), users involved in key distribution first need to authenticate each other. Classical identity authentication schemes were used in all the early implementations of QKD, but realizing their potential vulnerability, a few protocols for quantum identity authentication (QIA) have been proposed in the recent past. Here, we propose a new protocol for QIA which is constructed by modifying the concept of controlled secure direct quantum communication. The proposed controlled secure direct quantum communication inspired scheme for QIA allows two users Alice and Bob to mutually authenticate each other’s identity with the help of a third-party Charlie using Bell states. The security of the proposed protocol is critically analyzed, and it is shown that the proposed protocol is secure against several known attacks including impersonation attack, intercept and resend attack, and impersonated fraudulent attack. Further, the relevance of the proposed protocol is established by comparing it with a set of existing protocols for QIA with specific attention to the advantages of the present protocol.



Similar content being viewed by others
Data availability
Data sharing is not applicable to this article as no datasets were generated or analyzed during the current study.
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public-key distribution and coin tossing. In: Proceedings of the IEEE International Conference on Computers, Systems, and Signal Processing (Bangalore, India, 1984), pp. 175–179 (1984)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67(6), 661 (1991)
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68(21), 3121 (1992)
Wang, X., Sun, X., Liu, Y., Wang, W., Kan, B., Dong, P., Zhao, L.: Transmission of photonic polarization states from geosynchronous earth orbit satellite to the ground. Quantum Eng. 3(3), e73 (2021)
Tang, G.-Z., Li, C.-Y., Wang, M.: Polarization discriminated time-bin phase-encoding measurement-device-independent quantum key distribution. Quantum Eng. 3(4), e79 (2021)
She, L.-G., Zhang, C.-M.: Reference-frame-independent quantum key distribution with modified coherent states. Quantum Inf. Process. 21(5), 161 (2022)
Kwek, L.-C., Cao, L., Luo, W., Wang, Y., Sun, S., Wang, X., Liu, A.Q.: Chip-based quantum key distribution. AAPPS Bull. 31(1), 15 (2021)
Wegman, M.N., Carter, J.L.: New hash functions and their use in authentication and set equality. J. Comput. Syst. Sci. 22(3), 265–279 (1981)
Crépeau, C., Salvail, L.: Quantum oblivious mutual identification. In: International Conference on the Theory and Applications of Cryptographic Techniques, pp. 133–146. Springer (1995)
Li, X., Barnum, H.: Quantum authentication using entangled states. Int. J. Found. Comput. Sci. 15(04), 609–617 (2004)
Wang, J., Zhang, Q., Tang, C.-J.: Multiparty simultaneous quantum identity authentication based on entanglement swapping. Chin. Phys. Lett. 23(9), 2360–2363 (2006)
Zhang, Y.S., Li, C.F., Guo, G.C.: Quantum authentication using entangled state. arXiv preprint quant-ph/0008044 (2000)
Zhang, Z., Zeng, G., Zhou, N., Xiong, J.: Quantum identity authentication based on ping-pong technique for photons. Phys. Lett. A 356(3), 199–205 (2006)
Zhang, S., Chen, Z.-K., Shi, R.-H., Liang, F.-Y.: A novel quantum identity authentication based on Bell states. Int. J. Theor. Phys. 59(1), 236–249 (2020)
Kang, M.-S., Heo, J., Hong, C.-H., Yang, H.-J., Han, S.-W., Moon, S.: Controlled mutual quantum entity authentication with an untrusted third party. Quantum Inf. Process. 17(7), 159 (2018)
Chang, Y., Chunxiang, X., Zhang, S., Yan, L.: Controlled quantum secure direct communication and authentication protocol based on five-particle cluster state and quantum one-time pad. Chin. Sci. Bull. 59(21), 2541–2546 (2014)
Mihara, T.: Quantum identification schemes with entanglements. Phys. Rev. A 65(5), 052326 (2002)
Lo, H.-K., Chau, H.F.: Is quantum bit commitment really possible? Phys. Rev. Lett. 78(17), 3410 (1997)
Zeng, G., Wang, X.: Quantum key distribution with authentication. arXiv preprint quant-ph/9812022 (1998)
Dušek, M., Haderka, O., Hendrych, M., Myška, R.: Quantum identification system. Phys. Rev. A 60(1), 149 (1999)
Dutta, A., Pathak, A.: A short review on quantum identity authentication protocols: how would bob know that he is talking with alice? Quantum Inf. Process. 21(11), 369 (2022)
Long, G.-L., Liu, X.-S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A 65(3), 032302 (2002)
Lucamarini, M., Mancini, S.: Secure deterministic communication without entanglement. Phys. Rev. Lett. 94(14), 140501 (2005)
Pathak, A.: Elements of Quantum Computation and Quantum Communication. CRC Press, Boca Raton (2013)
Srikara, S., Thapliyal, K., Pathak, A.: Continuous variable direct secure quantum communication using Gaussian states. Quantum Inf. Process. 19(4), 132 (2020)
Shukla, C., Thapliyal, K., Pathak, A.: Semi-quantum communication: protocols for key agreement, controlled secure direct communication and dialogue. Quantum Inf. Process. 16(12), 295 (2017)
Yadav, P., Srikanth, R., Pathak, A.: Two-step orthogonal-state-based protocol of quantum secure direct communication with the help of order-rearrangement technique. Quantum Inf. Process. 13(12), 2731–2743 (2014)
Banerjee, A., Pathak, A.: Maximally efficient protocols for direct secure quantum communication. Phys. Lett. A 376(45), 2944–2950 (2012)
Shukla, C., Pathak, A.: Orthogonal-state-based deterministic secure quantum communication without actual transmission of the message qubits. Quantum Inf. Process. 13(9), 2099–2113 (2014)
Sheng, Y.-B., Zhou, L., Long, G.-L.: One-step quantum secure direct communication. Sci. Bull. 67(4), 367–374 (2022)
Deng, F.-G., Long, G.L., Liu, X.-S.: Two-step quantum direct communication protocol using the Einstein–Podolsky–Rosen pair block. Phys. Rev. A 68(4), 042317 (2003)
Deng, F.-G., Long, G.L.: Secure direct communication with a quantum one-time pad. Phys. Rev. A 69(5), 052319 (2004)
Chandra, D., Cacciapuoti, A.S., Caleffi, M., Hanzo, L.: Direct quantum communications in the presence of realistic noisy entanglement. IEEE Trans. Commun. 70(1), 469–484 (2021)
Long, G.-L., Pan, D., Sheng, Y.-B., Xue, Q., Jianhua, L., Hanzo, L.: An evolutionary pathway for the quantum internet relying on secure classical repeaters. IEEE Netw. 36(3), 82–88 (2022)
Boström, K., Felbinger, T.: Deterministic secure direct communication using entanglement. Phys. Rev. Lett. 89(18), 187902 (2002)
Yuan, H., Liu, Y., Pan, G., Zhang, G., Zhou, J., Zhang, Z.: Quantum identity authentication based on ping-pong technique without entanglements. Quantum Inf. Process. 13(11), 2535–2549 (2014)
Li, X., Chen, L.: Quantum authentication protocol using Bell state. In: The First International Symposium on Data, Privacy, and E-Commerce (ISDPE 2007), pp. 128–132. IEEE (2007)
Pathak, A.: Efficient protocols for unidirectional and bidirectional controlled deterministic secure quantum communication: different alternative approaches. Quantum Inf. Process. 14(6), 2195–2210 (2015)
Lo, H.-K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94(23), 230504 (2005)
Sharma, R.D., Thapliyal, K., Pathak, A., Pan, A.K., De, A.: Which verification qubits perform best for secure communication in noisy channel? Quantum Inf. Process. 15(4), 1703–1718 (2016)
Holevo, A.S.: Bounds for the quantity of information transmitted by a quantum communication channel. Probl. Peredachi Informatsii 9(3), 3–11 (1973)
ho Hong, C., Heo, J., Jang, J.G., Kwon, D.: Quantum identity authentication with single photon. Quantum Inf. Process. 16(10), 236 (2017)
Kang, M.-S., Heo, J., Hong, C.-H., Yang, H.-J., Moon, S., Han, S.-W.: Response to “comment on ‘controlled mutual quantum entity authentication with an untrusted third party’’’. Quantum Inf. Process. 19(4), 1–15 (2020)
Zhou, Z.R., Sheng, Y.B., Niu, P.H., Yin, L.G., Long, G.L., Hanzo, L.: Measurement-device-independent quantum secure direct communication. Sci. China Phys. Mech. Astron. 63(3), 230362 (2020)
Pan, D., Li, K., Ruan, D., Ng, S.X., Hanzo, L.: Single-photon-memory two-step quantum secure direct communication relying on Einstein–Podolsky–Rosen pairs. IEEE Access 8, 121146–121161 (2020)
Zhou, L., Sheng, Y.-B.: One-step device-independent quantum secure direct communication. Sci. China Phys. Mech. Astron. 65(5), 1–12 (2022)
Zhou, L., Sheng, Y.-B., Long, G.-L.: Device-independent quantum secure direct communication against collective attacks. Sci. Bull. 65(1), 12–20 (2020)
Yi-Nuo, W., Zhao-Yang, S., Yu-Lin, M., Nan, H., Hong-Yang, M.: Color image encryption algorithm based on DNA code and alternating quantum random walk. Acta Phys. Sin. 70(23) (2021). https://doi.org/10.7498/aps.70.20211255
Shukla, C., Kothari, V., Banerjee, A., Pathak, A.: On the group-theoretic structure of a class of quantum dialogue protocols. Phys. Lett. A 377(7), 518–527 (2013)
Banerjee, A., Shukla, C., Thapliyal, K., Pathak, A., Panigrahi, P.K.: Asymmetric quantum dialogue in noisy environment. Quantum Inf. Process. 16(2), 49 (2017)
Xu, T.J., Chen, Y., Geng, M.J., Ye, T.Y.: Single-state multi-party semiquantum key agreement protocol based on multi-particle GHZ entangled states. arXiv preprint arXiv:2112.05874 (2021)
Thapliyal, K., Sharma, R.D., Pathak, A.: Orthogonal-state-based and semi-quantum protocols for quantum private comparison in noisy environment. Int. J. Quantum Inf. 16(05), 1850047 (2018)
Asagodu, P., Thapliyal, K., Pathak, A.: Quantum and semi-quantum sealed-bid auction: vulnerabilities and advantages. arXiv preprint arXiv:2108.06388 (2021)
Acknowledgements
The authors thank DRDO India for the support provided through the Project Number ANURAG/MMG/CARS/2018-19/071. The authors also thank Kishore Thapliyal and Sandeep Mishra for their interest and technical feedback on this work.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Dutta, A., Pathak, A. Controlled secure direct quantum communication inspired scheme for quantum identity authentication. Quantum Inf Process 22, 13 (2023). https://doi.org/10.1007/s11128-022-03767-4
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-022-03767-4