Abstract
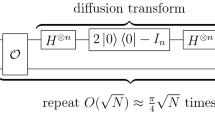
Simon’s algorithm is a well-known quantum algorithm which can achieve an exponential acceleration over classical algorithm. It has been widely used in quantum cryptanalysis of many cryptographic primitives. This paper concentrates on studying the applications of Simon’s algorithm in analyzing the security of Feistel variants, several well-known cryptographic structures derived from the Feistel structure. First, we propose a definition of weakly periodic function to relax the original strong Simon’s promise. Based on this definition, we define and analyze several extensions of Simon’s problem which expand the application of Simon’s algorithm. Furthermore, based on one extended Simon’s problem, we show new polynomial-time quantum distinguishing attacks on several Feistel variants: MISTY L/R, CAST256-like, CLEFIA-like, MARS-like, SMS4-like and Skipjack-A/B-like schemes. These new results show that classically secure schemes may be no longer secure in the Q2 model. Finally, based on the quantum distinguishers introduced above, we extend several rounds forward or backward to propose corresponding quantum all subkeys recovery attacks that can recover all subkeys in the Q2 model with lower query complexities than those in the Q1 model by using Grover’s algorithm.



















Similar content being viewed by others
References
Broadbent, A., Schaffner, C.: Quantum cryptography beyond quantum key distribution. Des. Codes Crypt. 78(1), 351–382 (2016)
Hosoyamada, A., Sasaki, Y.: Quantum Demiric-Selçuk meet-in-the-middle attacks: applications to 6-round generic Feistel constructions. In: International Conference on Security and Cryptography for Networks, pp. 386–403 (2018)
Canteaut, A., Duval, S., Leurent, G., Naya-Plasencia, M., Perrin, L., Pornin, T., Schrottenloher, A.: Saturnin: a suite of lightweight symmetric algorithms for post-quantum security. https://csrc.nist.gov/CSRC/media/Projects/Lightweight-Cryptography/documents/round-1/spec-doc/SATURNIN-spec.pdf (2019). Accessed 19 May 2019
Bonnetain, X.: Quantum key-recovery on full AEZ. In: SAC 2017, pp. 394–406 (2017)
Hosoyamada, A., Sasaki, Y.: Cryptanalysis against symmetric-key schemes with online classical queries and offline quantum computations. In: RSA 2018, pp. 198–218 (2018)
Mossayebi, S.: A concrete security treatment of symmetric encryption in a quantum computing world. Ph.D. Thesis, The University of London (2015)
Boneh, D., Dagdelen, Ö., Fischlin, M., Lehmann, A., Schaffner, C., Zhandry, M.: Random oracles in a quantum world. In: International Conference on the Theory and Application of Cryptology and Information Security, pp. 41–69 (2011)
Kaplan, M., Leurent, G., Leverrier, A., Naya-Plasencia, M.: Breaking symmetric cryptosystems using quantum period finding. In: CRYPTO 2016, pp. 207–237 (2016)
Zhandry, M.: How to construct quantum random functions. In: 53rd Annual IEEE Symposium on Foundations of Computer Science, pp. 679–687 (2012)
Damgård, I., Funder, J., Nielsen, J. B., Salvail, L.: Superposition attacks on cryptographic protocols. In: ICITS 2013, pp. 142–161 (2013)
Boneh, D., Zhandry, M.: Secure signatures and chosen ciphertext security in a quantum computing world. In: CRYPTO 2013, pp. 361–379 (2013)
Boneh, D., Zhandry, M.: Quantum-secure message authentication codes. In: EUROCRYPT 2013, pp. 592–608 (2013)
Simon, D.R.: On the power of quantum computation. SIAM J. Comput. 26(5), 1474–1483 (1997)
Kuwakado, H., Morii, M.: Quantum distinguisher between the 3-round Feistel cipher and the random permutation. In: IEEE International Symposium on Information Theory, pp. 2682–2685 (2010)
Kuwakado, H., Morii, M.: Security on the quantum-type Even-Mansour cipher. In: International Symposium on Information Theory and its Applications, pp. 312–316 (2012)
Dong, X., Dong, B., Wang, X.: Quantum attacks on some Feistel block ciphers. https://eprint.iacr.org/2018/504.pdf (2018). Accessed 19 May 2019
Bonnetain, X., Naya-Plasencia, M., Schrottenloher, A.: On quantum slide attacks. In: SAC 2019, pp. 492–519 (2019)
Ito, G., Hosoyamada, A., Matsumoto, R., Sasaki, Y., Iwata, T.: Quantum chosen-ciphertext attacks against Feistel ciphers. In: RSA 2019, pp. 391–411 (2019)
Santoli, T., Schaffner, C.: Using Simon’s algorithm to attack symmetric-key cryptographic primitives. Quantum Inf. Comput. 17(1 & 2), 65–78 (2017)
Shi, T., Jin, C., Guan, J.: Collision attacks against AEZ-PRF for authenticated encryption AEZ. China Commun. 15(2), 46–53 (2018)
Liu F., Liu F.: Universal forgery and key recovery attacks: application to FKS, FKD and Keyak. https://eprint.iacr.org/2017/691.pdf (2017) Accessed 19 May 2019
Liu F., Liu F.: Universal forgery with birthday paradox: application to blockcipher-based message authentication codes and authenticated encryptions. https://eprint.iacr.org/2017/653.pdf (2017) Accessed 19 May 2019
Xie, H., Yang, L.: Quantum miss-in-the-middle attack. https://arxiv.org/pdf/1812.08499.pdf (2018) Accessed 20 May 2019
Hosoyamada, A., Aoki, K.: On quantum related-key attacks on iterated Even–Mansour ciphers. In: 12th International Workshop on Security, pp. 3–18 (2017)
Leander, G., May, A.: Grover meets Simon-quantumly attacking the FX-construction. In: ASIACRYPT 2017, pp. 161–178 (2017)
Dong, X., Wang, X.: Quantum key-recovery attack on Feistel structures. Sci. China Inf. Sci. 61, 102501 (2018)
Dong, X., Li, Z., Wang, X.: Quantum cryptanalysis on some generalized Feistel schemes. Sci. China Inf. Sci. 62, 22501 (2019)
Ni, B., Dong, X.: Improved quantum attack on type-1 generalized Feistel schemes and its application to CAST-256. https://eprint.iacr.org/2019/318.pdf (2019). Accessed 19 May 2019
Ito, G., Iwata, T.: Quantum distinguishing attacks against type-1 generalized Feistel ciphers.https://eprint.iacr.org/2019/327.pdf (2019). Accessed 19 May 2019
Bonnetain, X., Naya-Plasencia, M., Schrottenloher, A.: Quantum security analysis of AES. https://eprint.iacr.org/2019/272.pdf (2019). Accessed 19 May 2019
Matsui, M.: New block encryption algorithm MISTY. In: FSE 1997, pp. 54–68 (1997)
Zheng, Y., Matsumoto, T., Imai, H.: On the construction of block ciphers provably secure and not relying on any unproved hypotheses. In: CRYPTO 1989, pp. 461–480 (1989)
Adams, C., Gilchrist, J.: The CAST-256 encryption algorithm. https://www.rfc-editor.org/info/rfc2612 (1999). Accessed 20 May 2019
Shirai, T., Shibutani, K., Akishita, T., Moriai, S., Iwata, T.: The 128-bit blockcipher CLEFIA (Extended abstract). In: FSE 2007, pp. 181–195 (2007)
Burwick, C., Coppersmith, D., D’Avignon, E., et al.: MARS—a candidate cipher for AES. http://cryptosoft.de/docs/Mars.pdf (1999) Accessed 20 May 2019
Diffie, W., Ledin, G.: SMS4 encryption algorithm for wireless networks. https://eprint.iacr.org/2008/329.pdf (2008). Accessed 20 May 2019
National Security Agency: SKIPJACK and KEA algorithm specifications. https://csrc.nist.gov/CSRC/media/Projects/Cryptographic-Algorithm-Validation-Program/documents/skipjack/skipjack.pdf (1998). Accessed 20 May 2019
Menezes, A.J., Van Oorschot, P.C., Vanstone, S.A.: Handbook of Applied Cryptography. CRC Press, Boca Raton (1997)
Alagic, G., Majenz, C., Russell, A., Song, F.: Quantum-secure message authentication via blind-unforgeability. https://eprint.iacr.org/2018/1150.pdf (2018). Accessed 21 May 2019
Loceff, M.: A course in quantum computing. http://lapastillaroja.net/wp-content/uploads/2016/09/Intro_to_QC_Vol_1_Loceff.pdf (2016). Accessed 5 Jan 2019
Brassard, G., Høyer, P., Mosca, M.: Quantum amplitude amplification and estimation. Quantum computation and information: a millennium volume. Contemp. Math. 305, 53–74 (2002)
Fuller, L.E.: Basic Matrix Theory. Courier Dover Publications, Mineola (2017)
Murphy, S., Robshaw, M.J.B.: Key-dependent S-boxes and differential cryptanalysis. Des. Codes Crypt. 27(3), 229–255 (2002)
Daemen, J., Rijmen, V.: Probability distributions of correlation and differentials in block ciphers. J. Math. Crypt. 1(3), 221–242 (2007)
Shi, T.R., Jin, C.H., Hu, B., et al.: Complete analysis of Simon’s quantum algorithm with additional collisions. Quantum Inf. Process. 18(11), 334 (2019)
Luby, M., Rackoff, C.: How to construct pseudorandom permutations from pseudorandom functions. SIAM J. Comput. 17(2), 373–386 (1988)
Treger, J., Patarin, J.: Generic attacks on Feistel networks with internal permutations. In: AFRICACRYPT 2009, pp. 41–59 (2009)
Gilbert, H., Minier, M.: New results on the pseudorandomness of some blockcipher constructions. In; FSE 2001, pp. 248–266 (2001)
Moriai, S., Vaudenay, S.: On the pseudorandomness of top-level schemes of block ciphers. In: ASIACRYPT 2000, pp. 289–302 (2000)
Zhang, L.T., Wu, W.L.: Pseudorandomness and super pseudorandomness on the unbalanced feistel networks with contracting functions. Chin. J. Comput. 32(7), 1320–1330 (2009)
Wu, W.L., Wei, H.R.: Pseudorandomness on the round-structure of Skipjack. Chin. Inst. Electron. 15(3), 378–383 (2006)
Samajder, S., Sarkar, P.: Another look at success probability in linear cryptanalysis. https://eprint.iacr.org/2017/391.pdf (2017). Accessed 19 May 2019
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Cui, J., Guo, J. & Ding, S. Applications of Simon’s algorithm in quantum attacks on Feistel variants. Quantum Inf Process 20, 117 (2021). https://doi.org/10.1007/s11128-021-03027-x
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-021-03027-x