Abstract
Inaccurate localization of wildfire boundary will adversely affect the efficiency of fire fighting, especially in the case of limited water for aerial dumping. This paper formulates the detection of occluded wildfire boundary as a shape completion problem and introduces a new solution. Different from traditional shape completion algorithms which only consider the contour geometry, the proposed algorithm takes partially visible fire surface geometry into consideration, and generates extrapolated feature points to detect the invisible section. The proposed solution involves two processes: firstly, fire surfaces above the occluded segments are extrapolated to the ground level with a Hurwitz–Radon operator based algorithm to obtain feature points in the invisible segments of the wildfire boundary; secondly, interpolating extra control points with a Bezier curve to reduce uncertainty and improve the accuracy of fire boundary detection. To demonstrate the effectiveness and efficiency of the proposed algorithm, a series of numerical simulations were performed. Simulated results show that the proposed algorithm in this study can detect the occluded wildfire boundary that conforms with the ground truth of the invisible fire boundary.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
Wildfire or forest fire is an uncontrolled fire in an area of combustible vegetation. Wildfires have become one of the most global critical natural hazards in the recent past [1], resulting in enormous damages to ecological environment and serious loss of human life, and destroys economic development [2,3,4]. The usual fire fighting tactic is to isolate the burning combustible substance from the unburned by applying a fire retardant to the forefront of the fire. This process is risky and time sensitive and also involves extensive human resources. In many cases, the lack of information about the current state and the dynamic evolution of fire worsens the efficiency of fire fighting. In addition, the fire which sometimes spreads at ferocious speeds threatens the lives of the firefighters. Given these circumstances, accurate determination of the fire boundary is absolutely essential so that the fire fighting equipment such as helicopters can accurately dump the fire retardants on the actual fire thereby significantly improving the fire fighting efficiency in fire risk management and suppression policy implementations [5].
To better understand wildfires, a large number of researches related to fire models e.g., physical [6] and quasi-physical models [7], empirical [8] and quasi-empirical models [9, 10], and simulation and mathematical analogue models [11] have been ongoing for decades to parameterize wildfire behavior. As the development of technology, the quantification of wildfire geometric characteristics such as rate of spread, inclination, length, width, surface and volume, etc., are available from 3D vision systems [12,13,14,15]. In this context, this paper relies on 3D sensed data to identify position of wildfire boundary. In the operation of gathering vision information, a dominant challenge is the ubiquitous occlusions. Either an interposed object or a surface of the object that happens to project similar colour without sufficient contrast can lead to occlusions. For wildfires, inclination of flame caused by winds will pose occlusions to wildfire perimeters in the process of data collection. In addition, the angle of view constrained by operational requirements, from which the data is collected also can lead to unavailability of predominant features of the wildfire boundary. In other situations thick smoke or plumes may also impair the visibility. If the location of wildfire boundary is not available or inaccurate, the application of retardants is likely to miss some segments of the fire boundary. Occlusions in the image poses a formidable problem to the computation of object boundaries. Many literatures treat the recovery of boundary with occlusions as a shape completion, curve completion or gap completion problem [16]. Studies of shape completion usually assume that the completed shape is induced by the two oriented line segments at the end points of the occluded segment and these studies are widely recognized to be divided into two problems: the first is the grouping problem, and the second is the shape problem [17]. The former problem determines which two candidate inducers can be paired [18] and the latter problem deals with retrieving the shape between two inducers [16]. In this paper, we focus on the shape problem, with the goal of accurate recovery of wildfire boundary subjected to occlusions.
A large number of methods have been suggested for curve reconstruction. Given two oriented inducers, approaches to shape completion includes the classical polynomial interpolation, such as Lagrange, Hermite, etc. Polynomial interpolation has superior features in construction and computation, however, it does not always provide satisfactory results [19]. To produce the desired shape, a new class of optimized geometric Hermite curves in which the magnitudes of the endpoint tangent vectors are optimized to minimize the strain energy of the curve is proposed [20]. Similarly, Lin et al. [21] imposes a shortest-length constraint on admissible curves by finding two unknown control points lying on the tangent lines of two inducers. Afterwards, the admissible curve was generated by the Bezier curve.
Previous researchers have proposed a set of predefined axioms to the completed curve. Among the first is the biarc model presented by Ullman [22] which seeks curves of least curvature meanwhile satisfying the requirements of isotropy, smoothness and extensibility. Nevertheless, later research found that the biarc models cannot meet the presented original axioms in some cases [23]. After Ullman’s work, some other axioms, known as scale invariance, roundedness, total minimum change of curvature [24] are also suggested. Among them, the total curvature or total variation in curvature is usually formulated as an energy functional and the preferred solution for retrieved shape should be with minimal energy function. The least curvature gives rise to the Elastica model [25] which uses the integral of a linear combination of the square curvature and the arc-length. Kimia et al. [16] proposed the criteria of minimizing the change of curvature, resulting in a family of Euler Spirals. This model has been further improved in works [26,27,28]. Except for axiomatic models, a somewhat different non-axiomatic approach, also dubbed as the mechanistic approach has been employed in some published work [24, 29, 30]. It specifies probabilistic models for the generation of maximum probability curves or for the calculation of point-wise probabilities of belonging to a curve [29]. Williams and Jacobs [31] found that the maximum likelihood paths are curves of least energy when following the predefined random walk rules. Singh and Fulvio [32,33,34] also found that the curvature decay in the occluded part is modeled in terms of a Bayesian interaction between probabilistically-expressed constraints to minimize curvature and minimize variation in curvature.
Aforementioned works formulate the problem of shape completion as contour interpolation and do not consider contours with large gaps. More specifically, the interpolation geometry is encoded in the form of the local geometry of inducing-contour pairs while ignoring the role of surface geometry. The reconstructed shape in the gap section is driven by contour-based mechanisms applying 1D constraints along contours. In addition, most of these models require more computation due to the minimization procedure. In practice, the local contour geometry is insufficient to predict the perceived shapes of occlusions, especially in the under-constrained case with large gaps. Figure 1 demonstrates the influence of extra control points on the recovery of an analogous curve with a large gap. As it illustrated in Fig. 1, there are three potential curves for shape completion while the curves 2 and 3 are far away from the ground truth. Actually, if some extra control points were provided, it is likely to estimate the occluded part in a more accurate way, just as the curve 1 which is very close to the original curve. Although the local geometry can predict extra control points, only limited number of points can be generated. For example, each of two end-points in the work [21] only predicts a control point in their tangent directions with a shortest-length constraint. To improve accuracy of shape completion, the surface geometry is preferred to obtain no less than two extra control points, especially in the case of very large gaps that are dynamically changing.
Motivated by the previous discussion, this paper presents an algorithm for accurate detection of wildfire boundary with large missing or invisible segments. The main differences between our proposed shape completion strategy and the existing shape completion approaches can be summarized as follows. First, extra control points in the large gap section will be obtained by considering the fire surface geometry rather than the contour geometry. Second, in contrast to existing interpolation approaches, an extrapolation approach will be employed to generate extra control points on the ground level. Finally, an interpolation algorithm will be adopted to process obtained extra control points and complete the gap. Moreover, no optimization procedures is required in the process of shape completion, hence the fire boundary can be accurately established in real-time. The main contributions of this paper include: (1) formulate the determination of invisible segments of a wildfire boundary as a shape completion problem; (2) exploit the fire surface geometry with a numerical extrapolation approach to anticipate extra control points on the invisible segment of the wildfire boundary; (3) reduce the uncertainty of reconstructed wildfire boundary with a Bezier curve based algorithm to interpolate extra control points; and (4) propose an analytical solution to wildfire boundary detection.
The rest of this paper is organized as follows. In Sect. 2, problem statement and the preliminaries of adopted extrapolation algorithm will be introduced. In Sect. 3, a surface curve extrapolation algorithm and a Bezier curve based algorithm are presented to recover wildfire perimeters with gaps. After presenting and discussing the simulation results of the proposed strategy in Sect. 4, conclusions are given in Sect. 5.
2 Preliminary Knowledge
In this paper, terms such as contour, boundary and perimeter carry the same import. In this section, we first formulate the recovery of wildfire boundary as the problem of shape completion. Then we introduce some preliminary knowledge and discuss some related challenges.
2.1 Problem Statement
The identification of wildfire boundary is challenging due to occlusions. Either projection of surface or the angle in which raw data is collected can lead to invisible areas in the actual wildfire boundary. In this paper, a rapid recovery algorithm is proposed to identity wildfire boundary with large gaps. Different from traditional shape completion algorithms which only consider the contour geometry, the fire surface geometry will be taken into consideration to generate extra control points on the ground before curve interpolation. In addition, the work [15] presented a possible solution with a drone carried stereoscopic sensing system for data collection. After image processing with the proposed algorithm in [15], 3D coordinates of visible points on the wildfire are assumed to be available.
The problem studied in this paper can be formulated as follows. As it illustrated in Fig. 2, 3D points cloud P(x, y, z) of a wildfire are collected by a stereoscopic sensing system. However, the sensed wildfire boundary has an occlusion and the end points of the invisible fire front segment are denoted as \(P_0\) and \(P_1\), which are also the end points of the visible fire front. To compute the invisible segment of the wildfire boundary that is not visible, we extrapolate the flame surface in the occluded area to the ground. The extrapolated points are used to calculate additional control points \(P_i^*(x,y,z)\) embodying the salient shape features in the gap segment. After that, two end points and extra control points are interpolated by a robust curve completion algorithm, which should have the feature of reducing uncertainties caused by extra control points.
2.2 Operator of Hurwitz–Radon
Dariusz [35,36,37] proposed a method which is based on local, orthogonal matrix operators for point extrapolation. This algorithm requires that at least four points monotonic in coordinate x or y direction are available. Its principle is to construct skew-symmetric Hurwitz-Radon (HR) matrices [38] build on N dimensional vector space and connect all available points with orthogonal and discrete operators of HR (OHRs) on the basis of HR matrices. Usually the value of N can be an element of the set \(\{2,4,8\}\).
If given points are monotonic in the direction of x, namely \(x_1<x_2<\cdots<x_{2N-1}<x_{2N}\), the coordinates of extrapolated points in x direction are computed by linearly combining the first coordinates of even and odd nodes in the form
where \(\alpha \) is a scale. Define a vector \(X^* = [x_1^*,x_2^*,\ldots ,x_N^*]^T\) comprising of the x coordinates of extrapolated points, then the second coordinates of extrapolated points is predicted by
where \(M_0\) and \(M_1\) are the OHR operators for odd nodes \((x_1,y_1),\ldots ,(x_{2N-1},y_{2N-1})\) and even nodes \((x_2,y_2),\ldots ,(x_{2N},y_{2N})\) respectively, and they are computed by substituting corresponding coordinates into the general form of OHR operator (3)
where \(u_0 = \sum \nolimits _{i=1}^{N}x_iy_i\), \(I_N\) is N dimensional identity matrix, matrix W consisted of the off-diagonal elements of M multiplying \(\sum \nolimits _{i=1}^Nx_i^2\). More Details of different dimensional OHR operators are provided in “Appendix”.
If the given nodes are monotonic in the coordinates \(y_i\), then the elements in the vector \(Y^* = [y_1^*,y_2^*,\ldots ,y_N^*]^T\) and the first coordinates of extrapolated points are estimated by
Similarly, the reverse OHR operator \(M^{-1}\) is given by
2.3 Bezier Curve
A Bezier curve is a fundamental tool in geometric design. It is generated by blending a set of Bernstein basis functions and a series of control points which make up a control polygon. The formula of Bezier curve is given by (7).
where the polynomials \(B_i(t) = \big ({\begin{matrix} n \\ i\\ \end{matrix}}\big ) t^i(1-t)^{n-i},\ i=0,1,\ldots ,n\) are Bernstein basis functions of degree n.
3 Methodology
3.1 Surface Curve Extrapolation
Because of the existence of occlusions, it is insufficient to predict extra control points in the large gap area by only depending on the contour geometry of wildfire boundary. By contrast, more cues for the estimation of feature points in the occluded parts can be provided by the surface geometry of wildfire. Nevertheless, certain surfaces above the gap of wildfire boundary may be invisible, therefore there is no direct intersection between the missing part of surface and the ground boundary. To obtain control points on the ground, the visible surface above the gap should be extended meanwhile keeping the characteristics of surface geometry.
In this paper, the principle of surface curve extrapolation is that converting the extension of three-dimensional surface to the ground to the problem of extrapolating a set of two-dimensional curves to the ground. The details of curve extrapolation are described as follows. Depending on which direction the length of the gap is large, a defined coordinate x or y is determined. Along the defined coordinate, above surface in the gap area will be divided into pieces with the step defined by the users. The points on each slice can be regarded as a set of three-dimensional points on the curve with a fixed value of first or second coordinates. After slicing, we have to selecting a certain number of nodes monotonic in x or y direction from the target curve determined by the visible points on the slice. Then the HR operator is issued to predict salient feature points on the invisible part by following Eqs. (1)–(3) or Eqs. (4)–(6).
In the process of curve extrapolation, the sign of scale \(\alpha \) influences the position of predicted points, as it illustrated in Fig. 3. There is a segment of two-dimensional line, ending at two nodes \(P_0(x_0,y_0)\) and \(P_1(x_1,y_1)\) and a third node P(x, y) settled between or beyond the two nodes in Fig. 3. The relationship among three points \(P_0(x_0,y_0)\) , \(P_1(x_1,y_1)\) and P(x, y) can be formulated by a convex (linear) combination:
where \(\alpha = \frac{\overrightarrow{PP_1}}{\overrightarrow{P_0P_1}}\). If \(0\le \alpha \le 1\), the third point P is interpolated between point \(P_0\) and point \(P_1\); if \(\alpha <0\) or \(\alpha >1\), the third point P is extrapolated on the left or right side of the two given points \(P_0\) and point \(P_1\). Hence, \(\alpha \) used to compute coordinates of points beyond the sampled visible curve on the sampled slice should satisfy \(\alpha <0 \) or \(\alpha >1\), depending on the order of sampled points.
3.2 Contour Curve Interpolation
After getting extra control points in the gap area, an interpolation algorithm will be developed to recover the occluded wildfire boundary. Since the anticipation of extra control points is unreliable and uncertain, to reduce the uncertainty of recovered wildfire boundary, a robust interpolation algorithm is preferred. The control polygon determines the shape of Bezier curve with defined order, as shown in Fig. 4. If all control points are co-linear, the generated curve is a straight line, like case (a) in Fig. 4. The start and end segments of the Bezier curve are both tangent to the first and last sections of the Bezier polygon. Bezier curves have the variation diminishing property, meaning that in intuitive terms a Bezier curves does not “undulate” more than the polygon of its control points, and may actually “undulate” less than that [39], as it shown in Fig. 4b–d.
Data extrapolation is an unstable process, hence the estimated control points extrapolated from fire boundary surface to the ground will deviate from the true missing points to some extent. The generated Bezier curve is likely to compensate the deviation and keep the recovered shape sufficiently close to the ground truth in the missing part if we select appropriate control points. Figure 5 illustrates the robustness of Bezier curve, from which the retrieved curve is close to the invisible one.
3.3 Recovery Algorithm
In Algorithm 1, the procedure of recovering wildfire boundary is demonstrated in algorithmic form, utilizing at each step the appropriate equations as formulated in Sects. 2 and 3.

In addition, we also evaluate the accuracy of retrieved curve quantitatively. First of all, we introduce the notion of Fréchet distance \(\delta _F\) [40] as the measure of resemblance between curves, taking into account the location and ordering of the points along the curves. After that, we define the relative reconstruction error (RRE) as the metric for accuracy evaluation.
where \(\delta _F(C_r, C^*)\) is the Fréchet distance between retrieved curve \(C_r\) and ground truth \(C^*\), points \(P_0\) and \(P_1\) are in pair inducers in the occluded segment of wildfire boundary.
4 Results
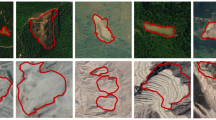
Generally it is very difficult to obtain 3D outdoor wildfire data, therefore the synthesized wildfire models with irregular shapes are generated by CAD and then they are discretized into cloud points. A series of numerical simulations were conducted with MATLAB to validate the effectiveness and efficiency of the proposed fire boundary recovery algorithm. This section presents the numerical results to prove the robustness of the proposed fire boundary extraction method.
In Scenario 1, it assumes that the wildfire boundary on the flat ground is a regular ellipse and the flame above the ground is formulated as part of an inclined ellipsoid, as shown in Fig. 6. In Fig. 6, visible and invisible points are represented in dot and stars respectively. The visible and occlusion segments of wildfire boundary are also displayed. Figure 7 is the visible boundary demonstrated by blue dash line in Fig. 6a, and the gap between two end-points \(P_0(x_0,y_0,z_0)\) and \(P_1(x_1,y_1,z_0)\) is the missing part represented by pink dash-diamond line in Fig. 6b. From the visible boundary illustrated in Fig. 7, the large gap between the two end-points \(P_0(x_0,y_0,z_0)\) and \(P_1(x_1,y_1,z_0)\) is around 90 m in length in the x direction. In order to apply the proposed algorithm, above surface satisfying \(x\in [x_0,x_1]\) was divided into slices perpendicular to the x-axis. Applying the OHR-based surface extrapolation algorithm to visible points on each slice, a set of projected points on the ground was obtained. In this scenario, points on each slice were treated as two-dimensional points, only considering coordinates in y and z directions. Figure 8 exemplifies the results of extrapolated points from available points on a randomly selected slice. The anticipated points on the ground were regarded as the extra control points on the ground. The final result of regular wildfire boundary completion is shown in Fig. 9, by interpolating all control points and the two inducer points with the Bezier curve based algorithm. It can be seen that the recovered wildfire boundary is close to the ground truth, indicating the capability of the proposed algorithm. For the regular wildfire boundary, its Fréchet distance \(\delta _F\) is \(2.7503\ \text{ m }\) and the value of RRE is 0.03, as it shown in Fig. 10.
To further validate the performance of this algorithm, testing on wildfires with irregular shapes were performed in Scenarios 2 and 3. Comparison between this algorithm and other interpolating algorithms were also made.
In Scenario 2, both the wildfire boundary and the fire surface were irregular shapes and the terrain is not flat, as it shown in Fig. 11. We assume that the altitude of the underlying surface is available by sensors. Figure 11b demonstrates the missing wildfire part on xy plane and indicates that the wildfire boundary has a large gap of about 18 m in x direction. Specifically, there is an acutely irregular portion in the missing segment. Similar to Scenario 1, two end-points \(P_0(x_0,y_0,z_0)\) and \(P_1(x_1,y_1,z_0)\) of the gapped fire boundary are identified firstly and above surface satisfying \(x\in [x_0,x_1]\) was divided into slices perpendicular to the x-axis. After slicing, all obtained slices are extrapolated to compute extra control points in the gap part. An example of how the sliced surface geometry is extrapolated is demonstrated in Fig. 12. The strategy of slicing follows the strategy of fixing a position in one direction. All visible surface points on this slice shown in Fig. 12 are represented by blue star and connected with dash line. They are sampled from the gap part in Fig. 11 and have a fixed value in x direction. After applying the proposed algorithm to deal with visible points, green filled squares indicating the extrapolated points from the surface geometry are predicted.
The final result obtained by the proposed boundary recovery algorithm is shown in Fig. 13. Compared with direct interpolation algorithms like Spline and a Bezier curve-based model [21] which only considers two tangent control points obtained from the contour geometry, the proposed algorithm in this article produces a better completed contour, especially when the segments are irregular and uneven. In contrast, other algorithms fail to reconstruct such irregular shapes. In addition, although there is a great uncertainty associated with the projected extra control points in the gap area, Bezier curve reduces this uncertainty and ensures the robustness of wildfire boundary extraction. The quantitative evaluation of three algorithms’ performance is illustrated in Fig. 14 and Table 1. In Scenario 2 with an irregular shape of wildfire boundary, the wildfire boundary retrieved using the proposed algorithm has a smaller Fréchet distance \(\delta _F\) in comparison to the other two algorithms. In terms of RRE, the proposed algorithm also outperforms the other two approaches.
We also evaluate the influence of the number of extra control points \(N_c\) on the performance accuracy of the proposed algorithm. In Scenario 2, the surface geometry above the gap part is sliced with different numbers and we apply the proposed algorithm to obtain corresponding number of extra control points for curve recovery. Comparison results among them are shown in Table 2. According to the simulation results, the change of accuracy evaluated by Fréchet distance \(\delta _F\) and RRE is opposed to that of the number of extra control points. We also find that the differences among the three numbers of control points \(N_c = 26\), 21 and 14 are very small. With the number of control points \(N_c = 10\), the proposed algorithm performs with the highest accuracy when compared with the performance with remaining number of control points, nevertheless this difference is not too prominent. Control points are needed to ensure the accuracy of the fire boundary. This accuracy needs to be sufficiently high to enable the dumping of fire retardant such as water accurately on to the fire boundary. Therefore, the users can determine the needed number of extra control points according to their requirements on accuracy.
In Scenario 3 (Fig. 15), the wildfire surface and the fire boundary also have irregular random shapes but the underlying surface is a flat plane. Besides, the wildfire surface has an inclination and its projection on xy plane occludes the wildfire boundary. As can be seen in Fig. 15b, there is a large invisible gap around \(30\ \text{ m }\) in the y direction. Two end points on the visible boundary are detected and surface above the gap is sliced with a series of \(y_i\in [y_0,y_1]\). Visible points on each slice with fixed values of y were treated as two-dimensional points \((x_i,z_i)\) and extrapolated to obtain extra control points on the ground. The distribution of predicted feature points is illustrated in Fig. 16. It can be seen that some extrapolated control points are far from the ground truth (invisible boundary) while some are very close to the ground truth. By comparison, the proposed algorithm has a better performance in estimating the change trend of invisible boundary, which is supported by Fig. 17. The evaluation of three algorithms’ performance is displayed in Table 3, where the proposed algorithm outperforms another two algorithms in terms of Fréchet distance \(\delta _F\) and RRE.
The authors acknowledge that the real flame sensing data is not yet available. In the absence of such data, we have developed the above two cases resembling real-life situations where fire has an irregular shape indicating that, by leveraging surface geometry to generate extra control points in the occluded segment, the proposed algorithm has a better performance than another two baseline algorithms in extracting the invisible parts of the fire boundary, regardless of the complexity of the wildfire boundary.
5 Conclusion
This paper proposed a new method to recover the invisible segments of a fire boundary. Different from traditional shape completion algorithms, the flame surface geometry was used to generate extra control points in the unknown area, which were later used by Bezier curve generation. To generate extra control points, a method based on HR operator was used to extend the flame surface curve to the ground level. While flame surface curve extrapolation is inaccurate, a Bezier curve based algorithm which has the variation diminishing property is applied, reducing the uncertainty caused by the control points generated through flame surface extrapolation. Three scenarios in which wildfires have regular or irregular shapes were created to validate the effectiveness and efficiency of the proposed fire boundary recovery algorithm. Simulation results show that the proposed algorithm can ensure the recovery of wildfire boundary with gaps, regardless of the flat or uneven terrain. In addition, it outperforms other shape completion algorithms. The fire boundary extracted this way may be used by fire fighting aircraft to direct fire retardants such as water very accurately to the actual fire boundary, thereby improving effectiveness of extinguishing wild fires. In the future we look forward to use the real flame data with our algorithm to further validate the proper functioning of the proposed methodology.
References
Quintano C, Fernández-Manso A, Roberts DA (2013) Multiple endmember spectral mixture analysis (MESMA) to map burn severity levels from Landsat images in Mediterranean countries. Remote Sens Environ 136:76–88
Baker G, Webb A, Whiting P (2020) Regulatory controls for buildings in wildfire-prone areas of Australia. Fire Technol 56:1903–1935
Sun T, Zhang L, Chen W, Tang X (2013) Mountains forest fire spread simulator based on geo-cellular automaton combined with Wang Zhengfei velocity model. IEEE J Sel Top Appl Earth Obs Remote Sens 6(4):1971–1987
Zheng Z, Huang W, Li S, Zeng Y (2017) Forest fire spread simulating model using cellular automaton with extreme learning machine. Ecol Model 348:33–43
Alexandridis A, Russo L, Vakalis D, Bafas G, Siettos CI (2011) Wildland fire spread modelling using cellular automata: evolution in large-scale spatially heterogeneous environments under fire suppression tactics. Int J Wildland Fire 20(5):633–647
Grasso P, Innocente M (2020) Physics-based model of wildfire propagation towards faster-than-real-time simulations. Comput Math Appl 80(5):790–808
Sullivan AL (2009) Wildland surface fire spread modelling, 1990–2007. 1: Physical and quasi-physical models. Int J Wildland Fire 18(4):349–368
Ambroz M, Balaovjech M, Medl’a M, Mikula K (2019) Numerical modeling of wildland surface fire propagation by evolving surface curves. Adv Comput Math 45:1067–1103
Sullivan AL (2009) Wildland surface fire spread modelling, 1990–2007. 2: Empirical and quasi-empirical models. Int J Wildland Fire 18(4):369–386
Mallet V, Keyes DE, Fendell FE (2009) Modeling wildland fire propagation with level set methods. Comput Math Appl 57(7):1089–1101
Sullivan LA (2009) Wildland surface fire spread modelling, 1990–2007. 3: Simulation and mathematical analogue models. Int J Wildland Fire 18(4):387–403
Akhloufi M, Ur Rahman Z, Reichenbach SE, Rossi L, Neifeld MA (2009) Three-dimensional tracking for efficient fire fighting in complex situations. In: Visual information processing XVIII, 14 April 2009, Orlando, Florida, USA, p 734109
Rossi L, Thierry M, Pieri A, Akhloufi M, Bosseur F (2011) Measurement of the geometric characteristics of a fire front by stereovision techniques on field experiments. Meas Sci Technol 22(12):125504
Rossi L, Molinier T, Akhloufi M, Pieri A, Tison Y (2013) Advanced stereovision system for fire spreading study. Fire Saf J 60(Aug):64–72
Toulouse T, Rossi L, Akhloufi MA, Pieri A, Maldague X (2018) A multimodal 3D framework for fire characteristics estimation. Meas Sci Technol. https://doi.org/10.1088/1361-6501/aa9cf3
Kimia BB, Frankel I, Popescu A-M (2003) Euler spiral for shape completion. Int J Comput Vis 54(1–3):159–182
Wagemans J, Elder J, Kubovy M, Palmer S, Singh M (1985) A century of Gestalt psychology in visual perception: I. Perceptual grouping and figure-ground organisation. Comput Vis Graph Image Process 31:156–177
Kellman PJ, Garrigan P, Shipley TF, Keane BP (2007) Interpolation processes in object perception: reply to Anderson (2007). Psychol Rev 114(2):488
Harary G, Tal A (2010) 3D Euler spirals for 3D curve completion. In: Proceedings of the twenty-sixth annual symposium on computational geometry, 2010. ACM, pp 393–402
Yong J-H, Cheng FF (2004) Geometric Hermite curves with minimum strain energy. Comput Aided Geom Des 21(3):281–301
Lin H, Wang Z, Feng P, Lu X, Yu J (2016) A computational model of topological and geometric recovery for visual curve completion. Comput Vis Media 2(4):329–342
Ullman S (1976) Filling-in the gaps: the shape of subjective contours and a model for their generation. Biol Cybern 25(1):1–6
Brady M, Grimson WEL, Langridge DJ (1980) Shape encoding and subjective contours. In: AAAI, 1980, pp 15–17
Ben-Yosef G, Ben-Shahar O (2011) A tangent bundle theory for visual curve completion. IEEE Trans Pattern Anal Mach Intell 34(7):1263–1280
Shen J, Kang SH, Chan TF (2003) Euler’s elastica and curvature-based inpainting. SIAM J Appl Math 63(2):564–592
Walton DJ, Meek DS (2008) An improved Euler spiral algorithm for shape completion. In: 2008 Canadian conference on computer and robot vision, 2008. IEEE, pp 237–244
Xu J, Collins MD, Singh V (2013) Incorporating topological constraints within interactive segmentation and contour completion via discrete calculus. In: CVPR, 2013, vol 2, p 6
Zhou H, Zheng J, Yang X (2012) Euler arc splines for curve completion. Comput Graph 36(6):642–650
Barnea E, Ben-Shahar O (2018) Curve reconstruction via the global statistics of natural curves. In: Proceedings of the IEEE conference on computer vision and pattern recognition, 2018, pp 3099–3107
Ben-Shahar O, Ben-Yosef G (2014) Tangent bundle elastica and computer vision. IEEE Trans Pattern Anal Mach Intell 37(1):161–174
Williams LR, Jacobs DW (1997) Stochastic completion fields: a neural model of illusory contour shape and salience. Neural Comput 9(4):837–858
Singh M, Fulvio JM (2005) Visual extrapolation of contour geometry. Proc Natl Acad Sci USA 102(3):939–944
Singh M, Fulvio JM (2006) Contour extrapolation using probabilistic cue combination. In: 2006 Conference on computer vision and pattern recognition workshop (CVPRW’06), 2006. IEEE, pp 188–188
Singh M, Fulvio JM (2007) Bayesian contour extrapolation: geometric determinants of good continuation. Vis Res 47(6):783–798
Jakóbczak D (2007) 2D and 3D image modeling using Hurwitz–Radon matrices. Pol J Environ Stud A 4:104–107
Jakóbczak D (2010) Curve extrapolation and data analysis using the method of Hurwitz–Radon matrices. Folia Oecon Stetin 9(1):121–138
Jakóbczak D (2019) Information analysis and 2D point extrapolation using method of Hurwitz–Radon matrices. Int Arab J Inf Technol 16(2):236–241
Eckmann B (2006) Topology, algebra, analysis—relations and missing links: Notices AMS 46 (1999), 520–527. Math Surv Lect 1943–2004:189–196
Gonzalez T, Diaz-Herrera J, Tucker A (2014) Computing handbook: computer science and software engineering, vol 1. CRC Press, Boca Raton
Eiter T, Mannila H (1994) Computing discrete Fréchet distance. Technical report. Citeseer
Acknowledgements
This research did not receive any specific funding.
Funding
Open Access funding enabled and organized by CAUL and its Member Institutions.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix
Appendix
HR matrices are skew-symmetric and satisfy
For dimension \(N = 2,4,8\), columns and rows of HR matrices are orthogonal only, the family of HR matrices consists of \(N-1\) matrices. If the coordinates of all available nodes are monotonic in a direction, we can build an orthogonal and discrete OHR on the basis of HR matrices.
For the case of \(N = 2\), given two nodes \((x_1,y_1)\) and \((x_2,y_2)\) satisfy \(x_1<x_2\), then the OHR of dimension \(N = 2\) is constructed as:
For the case of \(N = 4\), given four nodes \((x_1,y_1),(x_2,y_2),(x_3,y_3)\) and \((x_4,y_4)\) are monotonic in \(x_i\), then the construction of OHR of dimension \(N = 4\) is:
For the case of \(N = 8\), given eight nodes \((x_1,y_1),(x_2,y_2),\ldots ,(x_8,y_8)\) are monotonic in \(x_i\). Similar to (A.2) and (A.3), the OHR of dimension \(N = 8\) is built as:
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Feng, L., Katupitiya, J. Accurate Detection of Occluded Wildfire Boundary. Fire Technol 58, 1789–1813 (2022). https://doi.org/10.1007/s10694-022-01227-0
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10694-022-01227-0