Abstract
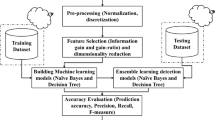
Cloud computing is a preferred option for organizations around the globe, it offers scalable and internet-based computing resources as a flexible service. Security is a key concern factor in any cloud solution due to its distributed nature. Security and privacy are huge obstacles faced in its success of the on-demand service as it is easily vulnerable to intruders for any kind of attack. A huge upsurge in network traffic has paved the way to security breaches which are more complicated and widespread. Tackling these attacks has become an inefficient application of traditional intrusion detection systems (IDS) environment. In this research, we developed an efficient Intrusion Detection System (IDS) for the cloud environment using ensemble feature selection and classification techniques. This proposed method was relying on the univariate ensemble feature selection technique, which is used for the selection of valuable reduced feature sets from the given intrusion datasets. While the ensemble classifiers that can competently fuse the single classifiers to produce a robust classifier using the voting technique. An ensemble based proposed method effectively classifies whether the network traffic behavior is normal or attack. The implementation of the proposed method was measured by applying various performance evaluation metrics and ROC-AUC (“area under the receiver operating characteristic curves”) across various classifiers. The results of the proposed methodology achieved a strong considerable amount of performance enhancement compared with other existing methods. Moreover, we performed a pairwise t test and proved that the performance of the proposed method was statistically significantly different from other existing approaches. Finally, the outcome of this investigation was obtained with the best accuracy and lowest false alarm rate (FAR).









Similar content being viewed by others
References
Thidar, M., Win, M., Khaing, K. T.: Detection and Classification of Attacks in Unauthorized Accesses. pp. 345–349 (2014) https://doi.org/10.15242/iie.e0314155
Pham, N. T., Foo, E., Suriadi, S., Jeffrey, H., Lahza, H. F. M.: Improving performance of intrusion detection system using ensemble methods and feature selection. In ACM International Conference Proceeding Series 1–6 (Association for Computing Machinery, 2018). https://doi.org/10.1145/3167918.3167951
Webb, G.I., Zheng, Z.: Multistrategy ensemble learning: reducing error by combining ensemble learning techniques. IEEE Trans. Knowl. Data Eng. 16, 980–991 (2004)
Mukkamala, S., Sung, A.H., Abraham, A.: Intrusion detection using an ensemble of intelligent paradigms. J. Netw. Comput. Appl. 1, 11 (2004). https://doi.org/10.1016/j.jnca.2004.01.003
Kumar Shrivas, A., Kumar Dewangan, A.: An ensemble model for classification of attacks with feature selection based on KDD99 and NSL-KDD data set. Int. J. Comput. Appl. 99, 8–13 (2014)
Kim, G., Lee, S., Kim, S.: A novel hybrid intrusion detection method integrating anomaly detection with misuse detection. Expert Syst. Appl. 41, 1690–1700 (2014)
Gogoi, P., Bhattacharyya, D.K., Borah, B., Kalita, J.K.: MLH-IDS: A multi-level hybrid intrusion detection method. Comput. J. 57, 602–623 (2014)
Sarkar, C., Cooley, S., Srivastava, J.: Robust feature selection technique using rank aggregation. Appl. Artif. Intell. 28, 243–257 (2014)
Mirza, A.H.: Computer network intrusion detection using various classifiers and ensemble learning. 26th IEEE Signal Process. Commun. Appl. Conf. SIU 2018 1, 11 (2018). https://doi.org/10.1109/siu.2018.8404704
Buczak, A.L., Guven, E.: A survey of data mining and machine learning methods for cyber security intrusion detection. IEEE Commun. Surv. Tutor. 18, 1153–1176 (2016)
Zhou, Y., Cheng, G., Jiang, S., Dai, M.: Building an efficient intrusion detection system based on feature selection and ensemble classifier. Comput. Networks 174, 10–247 (2019)
Gaikwad, D., Thool, R.: DAREnsemble: Decision tree and rule learner based ensemble for network intrusion detection system. In: Gaikwad, D., Thool, R. (eds.) Smart Innovation, Systems and Technologies. Springer, New York (2016)
Rajagopal, S., Kundapur, P.P., Hareesha, K.S.: A stacking ensemble for network intrusion detection using heterogeneous datasets. Secur. Commun. Netw. (2020). https://doi.org/10.1155/2020/4586875
Wankhade, A., Chandrasekaran, K.: Distributed-Intrusion Detection System using combination of Ant Colony Optimization (ACO) and support vector machine (SVM). in Proceedings - 2016 International Conference on Micro-Electronics and Telecommunication Engineering, ICMETE 2016 pp. 646–651 (Institute of Electrical and Electronics Engineers Inc., 2016). https://doi.org/10.1109/icmete.2016.94
Tama, B.A., Rhee, K.H.: An in-depth experimental study of anomaly detection using gradient boosted machine. Neural Comput. Appl. 31, 955–965 (2019)
Ahmad, I.: Feature selection using particle swarm optimization in intrusion detection. Int. J. Distrib. Sens. Networks 11, 806 (2015)
Prusti, D. An efficient intrusion detection model using ensemble methods. www.nitrkl.ac.in
Osanaiye, O., et al.: Ensemble-based multi-filter feature selection method for DDoS detection in cloud computing. Eurasip J. Wirel. Commun. Netw. 2016, 130 (2016)
Zhao, F., Zhao, J., Niu, X., Luo, S., Xin, Y.: A filter feature selection algorithm based on mutual information for intrusion detection. Appl. Sci. 8, 1535 (2018)
Yang, C.: Anomaly network traffic detection algorithm based on information entropy measurement under the cloud computing environment. Clust. Comput. 22, 8309–8317 (2019)
Binbusayyis, A., Vaiyapuri, T.: Identifying and benchmarking key features for cyber intrusion detection: an ensemble approach. IEEE Access 7, 106495–106513 (2019)
Saeys, Y., Abeel, T., Van De Peer, Y.: Robust feature selection using ensemble feature selection techniques. In Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) vol. 5212 LNAI pp. 313–325 (Springer, Berlin, 2008)
Kotsiantis, S.B.: Supervised machine learning: a review of classification techniques. Informatica 31, 208 (2007)
Ali, M., et al.: a data-driven knowledge acquisition system: an end-to-end knowledge engineering process for generating production rules. IEEE Access 6, 15587–15607 (2018)
Muallem, A., Shetty, S., Hong, L., Pan, J. W.: TDDEHT: threat detection using distributed ensembles of Hoeffding trees on streaming cyber datasets. Proc. - IEEE Mil. Commun. Conf. MILCOM 2019, pp. 219–224 (2019)
Lin, Y.-D., Lai, Y.-C., Ho, C.-Y., Tai, W.-H., Tai, W.-H.: Creditability-based weighted voting for reducing false positives and negatives in intrusion detection. Comput. Secur. 39, 460–474 (2013)
Krishnaveni, S., Prabakaran, S., Sivamohan, S.: A survey on honeypot and honeynet systems for intrusion detection in cloud environment. J. Comput. Theor. Nanosci. 15, 2956–2960 (2018)
Pervez, M. S., Farid, D. M.: Feature selection and intrusion classification in NSL-KDD cup 99 dataset employing SVMs. In SKIMA 2014 - 8th International Conference on Software, Knowledge, Information Management and Applications (Institute of Electrical and Electronics Engineers Inc., 2014). https://doi.org/10.1109/skima.2014.7083539
Song, J. et al.: Statistical analysis of honeypot data and building of Kyoto 2006 + dataset for NIDS evaluation. In: Proc. 1st Work. Build. Anal. Datasets Gather. Exp. Returns Secur. BADGERS 2011 29–36 (2011) https://doi.org/10.1145/1978672.1978676
Iwendi, C., et al.: The use of ensemble models for multiple class and binary class classification for improving intrusion detection systems. Sensors 20, 1–37 (2020)
Kim, H., Kim, J., Kim, Y., Kim, I., Kim, K.J.: Design of network threat detection and classification based on machine learning on cloud computing. Clust. Comput. 22, 2341–2350 (2019)
Gottwalt, F., Chang, E., Dillon, T.: CorrCorr: a feature selection method for multivariate correlation network anomaly detection techniques. Comput. Secur. 83, 234–245 (2019)
Wang, W., Du, X., Wang, N.: Building a cloud IDS using an efficient feature selection method and SVM. IEEE Access 7, 1345–1354 (2019)
Manickam, M., Rajagopalan, S.P.: A hybrid multi-layer intrusion detection system in cloud. Clust. Comput. 22, 3961–3969 (2019)
Ambusaidi, M.A., He, X., Nanda, P., Tan, Z.: Building an intrusion detection system using a filter-based feature selection algorithm. IEEE Trans. Comput. 65, 2986–2998 (2016)
Krishnaveni, S., Prabakaran, S.: Ensemble approach for network threat detection and classification on cloud computing. In Concurrency Computation (Wiley, Hoboken, 2019). https://doi.org/10.1002/cpe.5272
Acknowledgements
This paper and research work behind it would not have been possible without the support of our institution. We thankful to our esteemed institution SRM IST. Many thanks to the editor and reviewers for their concern and valuable comments for improving our manuscript. We also thank the referees for their useful suggestions. The author KS designed and developed the model for feature selection, classification, and developed a real-time environment for data collection using honeypot in the AWS, and also wrote the manuscript. The co-authors SM analysed and interpreted the experiments. S.S modified the final manuscript and answered most queries raised by reviewers. P.S edited the original version of the manuscript.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Krishnaveni, S., Sivamohan, S., Sridhar, S.S. et al. Efficient feature selection and classification through ensemble method for network intrusion detection on cloud computing. Cluster Comput 24, 1761–1779 (2021). https://doi.org/10.1007/s10586-020-03222-y
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10586-020-03222-y