Abstract
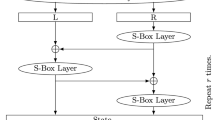
In this paper we cryptanalyze the CBCM mode of operation, which was almost included in the ANSI X9.52 Triple-DES Modes of Operation standard. The CBCM mode is a Triple-DES CBC variant which was designed against powerful attacks which control intermediate feedback for the benefit of the attacker. For this purpose, it uses intermediate feedbacks that the attacker cannot control, choosing them as a keyed OFB stream, independent of the plaintexts and the ciphertexts. In this paper we find a way to use even this kind of feedback for the benefit of the attacker, and we present an attack which requires a single chosen ciphertext of 265 blocks which needs to be stored and 259 complexity of analysis (CBCM encryptions) to find the key with a high probability. As a consequence of our attack, ANSI decided to remove the CBCM mode from the proposed standard.
Article PDF
Similar content being viewed by others
References
ANSI X9.52-1998. Triple Data Encryption Algorithm Modes of Operation.
ANSI draft X9.52. Triple Data Encryption Algorithm Modes of Operation, Revision 6.0, May 1996.
E. Biham. On modes of operation (Abstract). In R. Anderson, editor, Fast Software Encryption — Proc. Cambridge Security Workshop, Cambridge, U.K., LNCS 809, pages 116–120. Springer-Verlag, Berlin, 1994.
E. Biham. How to Forge DES-Encrypted Messages in 228 Steps. Technical Report CS884, Technion, August 1996.
E. Biham. Cryptanalysis of Triple Modes of Operation. Technical Report CS885, Technion, August 1996. A preliminary version of [7].
E. Biham. Cryptanalysis of multiple modes of operation. Journal of Cryptology, 11(1):45–58, 1998.
E. Biham. Cryptanalysis of triple modes of operation. Journal of Cryptology, 12(3): 161–184, 1999.
E. Biham and L. R. Knudsen. Cryptanalysis of the ANSI X9.52 CBCM mode. In K. Nyberg, editor, Advances in Cryptology — EUROCRYPT ’98, LNCS 1403, pages 100–111. Springer-Verlag, Berlin, 1998.
D. Coppersmith, D. B. Johnson, and S. M. Matyas. A proposed mode for Triple-DES encryption. IBM Journal of Research and Development, 40(2):253–261, March 1996.
D. Coppersmith, D. B. Johnson, and S. M. Matyas. Triple DES Cipher Block Chaining with Output Feedback Masking. Technical Report RC 20591, IBM, October 1996. Presented at the rump session of CRYPTO ’96.
D. W. Davies and G. I. P. Parkin. The average cycle size of the key stream in output feedback encipherment (Abstract). In D. Chaum, R. L. Rivest, and A. T. Sherman, editors, Advances in Cryptology: Proceedings of Crypto ’82, pages 97–98. Plenum, New York, 1982.
The DESCHALL home page, http://www.frii.com/~rcv/deschall.htm.
The distributed.net home page, http://www.distributed.net/.
Electronic Frontier Foundation. Cracking DES—Secrets of Encryption Research, Wiretap Politics & Chip Design. O’Reilly, Cambridge, MA, 1998. ISBN 1-56592-520-3.
B. S. Kaliski and M. J. B. Robshaw. Multiple encryption: weighing security and performance. Dr. Dobb’s Journal, pages 123–127, January 1996.
L. R. Knudsen. Block Ciphers — Analysis, Design and Applications. Ph.D. thesis, Aarhus University, 1994.
S. Lucks. Attacking triple encryption. In S. Vaudenay, editor, Fast Software Encryption, Fifth International Workshop, FSE ’98, Paris, France, March 1998, LNCS 1372, pages 239–253. Springer-Verlag, Berlin, 1998.
J. Markoff. U.S. group delays encryption standard. New York Times, March 31, 1998.
U. M. Maurer. New approaches to the design of self-synchronizing stream ciphers. In D. W. Davies, editor, Advances in Cryptology — EUROCRYPT ’91, LNCS 547, pages 458–471. Springer-Verlag, Berlin, 1991.
R. Merkle and M. Hellman. On the security of multiple encryption. Communications of the ACM, 24(7):465–467, 1981.
National Bureau of Standards. Data Encryption Standard. Federal Information Processing Standard (FIPS), Publication 46, National Bureau of Standards, U.S. Department of Commerce, Washington DC, January 1977.
P. C. van Oorschot and M. J. Wiener. A known-plaintext attack on two-key triple encryption. In Ivan B. Damgård, editor, Advances in Cryptology — EUROCRYPT ’90, LNCS 473, pages 318–325. Springer-Verlag, Berlin 1990.
D. Wagner. Cryptanalysis of some multiple modes of operation. In S. Vaudenay, editor, Fast Software Encryption, Fifth International Workshop, FSE ’98, Paris, France, March 1998, LNCS 1372, pages 254–269. Springer-Verlag, Berlin, 1998.
M. J. Wiener. Efficient DES Key Search. Technical Report TR-244, School of Computer Science, Carleton University, Ottawa, May 1994. Presented at the Rump Session of CRYPTO ’93.
M. J. Wiener. Efficient DES key search — an update. CryptoBytes, 3(2):6–8, 1998.
Author information
Authors and Affiliations
Additional information
Communicated by Ivan Damgård
Online publication 28 November 2001
A preliminary version of this paper was presented at EUROCRYPT ’98 in Finland, June 1998 [8]. The first author was supported by the fund for the promotion of research at the Technion.
Rights and permissions
About this article
Cite this article
Biham, E., Knudsen, L.R. Cryptanalysis of the ANSI X9.52 CBCM mode. J. Cryptology 15, 47–59 (2002). https://doi.org/10.1007/s00145-001-0016-5
Received:
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00145-001-0016-5