Abstract
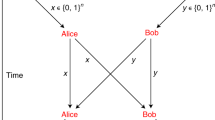
We present a quantum position verification scheme in the random oracle model. In contrast to prior work, our scheme does not require bounded storage/retrieval/entanglement assumptions. We also give an efficient position-based authentication protocol. This enables secret and authenticated communication with an entity that is only identified by its position in space.
We’re sorry, something doesn't seem to be working properly.
Please try refreshing the page. If that doesn't work, please contact support so we can address the problem.
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Ashby, N.: General relativity in the global positioning system. Matters of Gravity (newsletter of the Topical Group in Gravitation of the APS), 9 (1997), http://www.phys.lsu.edu/mog/mog9/node9.html (accessed: February 07, 2014) (Archived by WebCite at http://www.webcitation.org/6ND19QXJ3 )
Bagnara, R., Hill, P.M., Zaffanella, E.: The Parma Polyhedra Library: Toward a complete set of numerical abstractions for the analysis and verification of hardware and software systems. Science of Computer Programming 72(1-2), 3–21 (2008), http://bugseng.com/products/ppl/
Boneh, D., Dagdelen, Ö., Fischlin, M., Lehmann, A., Schaffner, C., Zhandry, M.: Random oracles in a quantum world. In: Lee, D.H., Wang, X. (eds.) ASIACRYPT 2011. LNCS, vol. 7073, pp. 41–69. Springer, Heidelberg (2011)
Buhrman, H., Chandran, N., Fehr, S., Gelles, R., Goyal, V., Ostrovsky, R., Schaffner, C.: Position-based quantum cryptography: Impossibility and constructions. In: Rogaway, P. (ed.) CRYPTO 2011. LNCS, vol. 6841, pp. 429–446. Springer, Heidelberg (2011)
Chandran, N., Goyal, V., Moriarty, R., Ostrovsky, R.: Position based cryptography. In: Halevi, S. (ed.) CRYPTO 2009. LNCS, vol. 5677, pp. 391–407. Springer, Heidelberg (2009)
Kaniewski, J., Tomamichel, M., Hänggi, E., Wehner, S.: Secure bit commitment from relativistic constraints. IEEE Trans. on Inf. Theory 59(7), 4687–4699 (2013)
Kent, A.: Unconditionally secure bit commitment by transmitting measurement outcomes. Phys. Rev. Lett. 109(13), 130501 (2012)
Kent, A., Munro, W.J., Spiller, T.P.: Quantum tagging: Authenticating location via quantum information and relativistic signaling constraints. Phys. Rev. A 84, 012326 (2011)
Nielsen, M., Chuang, I.: Quantum Computation and Quantum Information, 10th anniversary edn. Cambridge University Press, Cambridge (2010)
Stein, W., et al.: Sage Mathematics Software (Version 5.12). The Sage Development Team (2014), http://www.sagemath.org
Tomamichel, M., Fehr, S., Kaniewski, J., Wehner, S.: One-sided device-independent QKD and position-based cryptography from monogamy games. In: Johansson, T., Nguyen, P.Q. (eds.) EUROCRYPT 2013. LNCS, vol. 7881, pp. 609–625. Springer, Heidelberg (2013)
Unruh, D.: Quantum position verification in the random oracle model. IACR ePrint 2014/118, Full version of this paper (February 2014), http://eprint.iacr.org/2014/118
Zhandry, M.: Secure identity-based encryption in the quantum random oracle model. In: Safavi-Naini, R., Canetti, R. (eds.) CRYPTO 2012. LNCS, vol. 7417, pp. 758–775. Springer, Heidelberg (2012)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 International Association for Cryptologic Research
About this paper
Cite this paper
Unruh, D. (2014). Quantum Position Verification in the Random Oracle Model. In: Garay, J.A., Gennaro, R. (eds) Advances in Cryptology – CRYPTO 2014. CRYPTO 2014. Lecture Notes in Computer Science, vol 8617. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-662-44381-1_1
Download citation
DOI: https://doi.org/10.1007/978-3-662-44381-1_1
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-662-44380-4
Online ISBN: 978-3-662-44381-1
eBook Packages: Computer ScienceComputer Science (R0)