Abstract
The Governance, Risk, and Compliance (GRC) management process for Information Security is a necessity for any software systems where important information is collected, processed, and used. To this extent, many standards for security managements at operational level exists (e.g., ITIL, ISO27K family etc). What is often missing is a process to govern security at organizational level.
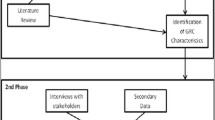
In this tutorial, we present a method to analyze and design security controls that capture the organizational setting of the system and where business goals and processes are the main citizen. The SI*-GRC method is a comprehensive method that is composed of i) a modeling framework based on a requirement engineering framework, with some extensions related to security & GRC concerns, such as: trust, permission, risk, and treatment, 2) a analysis process defining systematical steps in analyzing and design security controls, 3) analytical techniques to verify that certain security properties are satisfied and the risk level is acceptable, and at last 4) a CASE tool, namely the SI* Tool to support analysts in using the method.
To illustrate this method, we use a running example on e-Health adapted from a real-life process in an hospital partner.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Rasmussen, M., Kark, K., Penn, J., McClean, C., Bernhardt, S.: Trends 2007: Governance, risk and compliance: Organizations are motivated to formalize a federated GRC process. Technical report, Forrester Research (April 2007)
McClean, C., Whiteley, R., Kark, K., Dill, A.: The Forrester Wave: Enterprise governance, risk, and compliance platforms, Q3 2009. Technical report, Forrester Research (July 2009)
ACL: Audit command language, http://www.acl.com/ (last check July 15, 2010 (3020))
Pfleeger, C.P., Pfleeger, S.L.: Security in Computing, 4th edn. Prentice-Hall, Englewood Cliffs (2006)
ISACA: The Risk IT Framework. ISACA (November 2009)
Institute, T.I.G.: CoBIT - Framework Control Objectives Management Guidelines Maturity Models. 4.1 edn. ISACA.org (2007)
Trist, E.: The evolution of Socio-Technical systems. Occasional Paper 2 (1981)
Asnar, Y., Lim, H.W., Massacci, F., Worledge, C.: Realizing trustworthy business services through a new GRC approach. ISACA Journal - JOnline 2 (2010)
Deming, W.E.: Out of the Crisis. MIT Press, Cambridge (2000)
Marino, D., Potral, J.J., Hall, M., Rodriguez, C.B., Rodriguez, P.S., Sobota, J., Jiri, M., Asnar, Y.: Master scenarios. Project Deliverable D1.2.1, MASTER Consortium (2009); This case study has been provided by Hospital San Raffaele Foundation, Its complete description is available at http://www.masterfp7.eu/index.php?option=com_docman&task=doc_details&gid=53&Itemid=60
Erl, T.: SOA Principles of Service Design. Prentice-Hall, Englewood Cliffs (2007)
Casteleyn, S., Daniel, F., Dolog, P., Matera, M.: Engineering Web Applications. Springer-Verlag New York Inc., New York (2009)
Yu, E.: Modelling Strategic Relationships for Process Engineering. PhD thesis, University of Toronto, Department of Computer Science (1995)
OMG: Business process modeling notation (January 2009)
Hofstede, A.H.M., Aalst, W.M.P., Adams, M., Russell, N. (eds.): Modern Business Process Automation-YAWL and its Support Environment. Springer, Heidelberg (2010)
Giorgini, P., Massacci, F., Mylopoulos, J., Zannone, N.: Requirements engineering for trust management: model, methodology, and reasoning. International Journal of Information Security 5(4), 257–274 (2006)
Robbins, S.P.: Organizational Behavior, Concepts, Controversies, Applications, 7th edn. Prentice-Hall, Englewood Cliffs (1996)
OCC: Management information systems. the comptroller’s handbook, Office of the Comptroller of the Currency (May 1995)
Zachman, J.A.: A framework for information systems architecture. IBM Systems Journal 26(3), 276–292 (1987)
van der Aalst, W.M.P.: Formalization and verification of event-driven process chains. Information and Software Technology 41(10), 639–650 (1999)
Eriksson, H.E., Penker, M.: Business modeling with UML: Business Patterns at Work. John Wiley & Sons, Chichester (2000)
van der Aalst, W.M.P., Pesic, M., Schonenberg, H.: Declarative workflows: Balancing between flexibility and support. Computer Science - Research and Development (March 2009)
van der Aalst, W.M., Weske, M., Grünbauer, D.: Case handling: a new paradigm for business process support. Data & Knowledge Engineering 53(2), 129–162 (2005)
Bresciani, P., Perini, A., Giorgini, P., Giunchiglia, F., Mylopoulos, J.: Tropos: An Agent-Oriented software development methodology. Autonomous Agents and Multi-Agent Systems 8(3), 203–236 (2004)
Massacci, F., Mylopoulos, J., Zannone, N.: Computer-aided support for secure tropos. Automated Software Engineering 14(3), 341–364 (2007)
Compagna, L., Khoury, P.E., Krausová, A., Massacci, F., Zannone, N.: How to integrate legal requirements into a requirements engineering methodology for the development of security and privacy patterns. Artificial Intelligence and Law 17(1), 1–30 (2008)
Asnar, Y., Giorgini, P., Mylopoulos, J.: Goal-driven risk assessment in requirements engineering. Requirements Engineering 16(2), 101–116 (2011), 10.1007/s00766-010-0112-x
ISO/IEC: Risk Management-Vocabulary-Guidelines for Use in Standards, Published: ISO/IEC Guide 73 (2002)
Vose, D.: Risk Analysis: A Quantitative Guide. Wiley, Chichester (2000)
Mosleh, A., Hilton, E.R., Browne, P.S.: Bayesian probabilistic risk analysis. SIGMETRICS Perform. Eval. Rev. 13(1), 5–12 (1985)
Lund, M.S., Solhaug, B., Stlen, K.: Model-Driven Risk Analysis - The CORAS Approach. Springer, Heidelberg (2011)
Vesely, W., Goldberg, F., Roberts, N., Haasl, D.: Fault Tree Handbook. U.S Nuclear Regulatory Commission (1981)
Delande, O., Felix, E., Massacci, F., Paci, F.: Managing changes with legacy security engineering processes. In: Zeng, D., Yang, C.C., Collberg, C. (eds.) Proc. of IEEE Internat. Conf. on Intelligence and Security Informatics (ISI 2011). IEEE Press, Los Alamitos (2011)
Namiri, K.: Model-Driven Management of Internal Controls for Business Process Compliance. PhD thesis, Universität Fridericiana zu Karlsruhe (2008)
Schumacher, M., Fernandez-Buglioni, E., Hybertson, D., Buschmann, F., Sommerlad, P.: Security Patterns: Integrating Security and Systems Engineering, 1st edn. Wiley, Chichester (2006)
Chappell, D.: Enterprise Service Bus. O’Reilly Media, USA (2004)
Kochar, H.: Business Activity Monitoring and Business Intelligence, (December 2005), http://www.ebizq.net/topics/bam/features/6596.html (last access at July 03, 2010)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this chapter
Cite this chapter
Asnar, Y., Massacci, F. (2011). A Method for Security Governance, Risk, and Compliance (GRC): A Goal-Process Approach. In: Aldini, A., Gorrieri, R. (eds) Foundations of Security Analysis and Design VI. FOSAD 2011. Lecture Notes in Computer Science, vol 6858. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-23082-0_6
Download citation
DOI: https://doi.org/10.1007/978-3-642-23082-0_6
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-23081-3
Online ISBN: 978-3-642-23082-0
eBook Packages: Computer ScienceComputer Science (R0)