Abstract
Suppose we are given a perfect n + c-to-n bit compression function f and we want to construct a larger m + s-to-s bit compression function H instead. What level of security, in particular collision resistance, can we expect from H if it makes r calls to f? We conjecture that typically collisions can be found in 2(nr + cr − m)/(r + 1) queries. This bound is also relevant for building a m + s-to-s bit compression function based on a blockcipher with k-bit keys and n-bit blocks: simply set c = k, or c = 0 in case of fixed keys.
We also exhibit a number of (conceptual) compression functions whose collision resistance is close to this bound. In particular, we consider the following four scenarios:
-
1
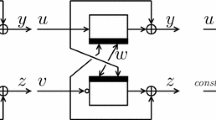
A 2n-to-n bit compression function making two calls to an n-to-n bit primitive, providing collision resistance up to 2n/3/n queries. This beats a recent bound by Rogaway and Steinberger that 2n/4 queries to the underlying random n-to-n bit function suffice to find collisions in any rate-1/2 compression function. In particular, this shows that Rogaway and Steinberger’s recent bound of 2(nr − m − s/2)/r) queries (for c = 0) crucially relies upon a uniformity assumption; a blanket generalization to arbitrary compression functions would be incorrect.
-
1
A 3n-to-2n bit compression function making a single call to a 3n-to-n bit primitive, providing collision resistance up to 2n queries.
-
1
A 3n-to-2n bit compression function making two calls to a 2n-to-n bit primitive, providing collision resistance up to 2n queries.
-
1
A single call compression function with parameters satisfying m ≤ n + c, n ≤ s, c ≤ m. This result provides a tradeoff between how many bits you can compress for what level of security given a single call to an n + c-to-n bit random function.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Bellare, M., Kohno, T.: Hash function balance and its impact on birthday attacks. In: Cachin, C., Camenisch, J.L. (eds.) EUROCRYPT 2004. LNCS, vol. 3027, pp. 401–418. Springer, Heidelberg (2004)
Black, J., Cochran, M., Shrimpton, T.: On the impossibility of highly efficient blockcipher-based hash functions. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 526–541. Springer, Heidelberg (2005)
Black, J., Rogaway, P., Shrimpton, T.: Black-box analysis of the block-cipher-based hash-function constructions from PGV. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442. Springer, Heidelberg (2002)
Damgård, I.: A design principle for hash functions. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435. Springer, Heidelberg (1990)
Hirose, S.: Some plausible constructions of double-length hash functions. In: Robshaw, M. (ed.) FSE 2006. LNCS, vol. 4047, pp. 210–225. Springer, Heidelberg (2006)
Johnson, N.L., Kotz, S.: Urn Models and Their Applications. John Wiley and Sons, Inc., Chichester (1977)
Knudsen, L., Muller, F.: Some attacks against a double length hash proposal. In: Lai, X., Chen, K. (eds.) ASIACRYPT 2006. LNCS, vol. 4284, pp. 462–473. Springer, Heidelberg (2006)
Lucks, S.: A collision-resistant rate-1 double-block-length hash function. In: Biham, E., Handschuh, H., Lucks, S., Rijmen, V. (eds.) Symmetric Cryptography, number 07021 in Dagstuhl Seminar Proceedings, Dagstuhl, Germany, 2007, Schloss Dagstuhl, Germany. Internationales Begegnungs- und Forschungszentrum für Informatik (IBFI) (2007)
Maurer, U., Tessaro, S.: Domain extension of public random functions: Beyond the birthday barrier. In: Menezes, A. (ed.) CRYPTO 2007. LNCS, vol. 4622, pp. 187–204. Springer, Heidelberg (2007)
Merkle, R.: One way hash functions and DES. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 428–466. Springer, Heidelberg (1990)
Mironov, I., Narayanan, A.: Domain extension for random oracles: Beyond the birthday-paradox bound. In: ECRYPT Hash Workshop 2007, Barcelona, May 24–25 (2007)
Nandi, M., Lee, W., Sakurai, K., Lee, S.: Security analysis of a 2/3-rate double length compression function in black-box model. In: Gilbert, H., Handschuh, H. (eds.) FSE 2005. LNCS, vol. 3557, pp. 243–254. Springer, Heidelberg (2005)
Peyrin, T., Gilbert, H., Muller, F., Robshaw, M.: Combining compression functions and block cipher-based hash functions. In: Lai, X., Chen, K. (eds.) ASIACRYPT 2006. LNCS, vol. 4284, pp. 315–331. Springer, Heidelberg (2006)
Rogaway, P., Steinberger, J.: Security/efficiency tradeoffs for permutation-based hashing. Full version of [16] available through authors’ website
Rogaway, P., Steinberger, J.: Constructing cryptographic hash functions from fixed-key blockciphers. In: Wagner, D. (ed.) CRYPTO 2008. LNCS, vol. 5157, pp. 433–450. Springer, Heidelberg (2008)
Rogaway, P., Steinberger, J.: Security/efficiency tradeoffs for permutation-based hashing. In: Smart, N. (ed.) EUROCRYPT 2008. LNCS, vol. 4965, pp. 220–236. Springer, Heidelberg (2008)
Seurin, Y., Peyrin, T.: Security analysis of constructions combining FIL random oracles. In: Biryukov, A. (ed.) FSE 2007. LNCS, vol. 4593, pp. 119–136. Springer, Heidelberg (2007)
Shrimpton, T., Stam, M.: Efficient collision-resistant hashing from fixed-length random oracles. In: ECRYPT Hash Workshop 2007, Barcelona, May 24–25 (2007)
Shrimpton, T., Stam, M.: Building a collision-resistant compression function from non-compressing primitives. In: ICALP 2008, Part II, vol. 5126, pp. 643–654. Springer, Heidelberg (2008); Supersedes [18]
Steinberger, J.: The collision intractability of MDC-2 in the ideal-cipher model. In: Naor, M. (ed.) EUROCRYPT 2007. LNCS, vol. 4515, pp. 34–51. Springer, Heidelberg (2007)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Stam, M. (2008). Beyond Uniformity: Better Security/Efficiency Tradeoffs for Compression Functions. In: Wagner, D. (eds) Advances in Cryptology – CRYPTO 2008. CRYPTO 2008. Lecture Notes in Computer Science, vol 5157. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-85174-5_22
Download citation
DOI: https://doi.org/10.1007/978-3-540-85174-5_22
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-85173-8
Online ISBN: 978-3-540-85174-5
eBook Packages: Computer ScienceComputer Science (R0)