Abstract
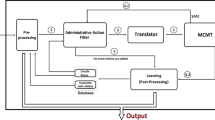
We present a logic for specifying policies where access requests can have effects on the authorization state. The logic is semantically defined by a mapping to Transaction Logic. Using this approach, updates to the state are factored out of the resource guard, thus enhancing maintainability and facilitating more expressive policies that take the history of access requests into account. We also present a sound and complete proof system for reasoning about sequences of access requests. This gives rise to a goal-oriented algorithm for finding minimal sequences that lead to a specified target authorization state.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Blaze, M., Feigenbaum, J., Keromytis, A.D.: The role of trust management in distributed systems security. In: Vitek, J. (ed.) Secure Internet Programming. LNCS, vol. 1603, pp. 185–210. Springer, Heidelberg (1999)
Becker, M.Y., Nanz, S.: A logic for state-modifying authorization policies. Technical Report MSR-TR-2007-32, Microsoft Research (2007)
Bonner, A.J., Kifer, M.: An overview of transaction logic. Theoretical Computer Science 133(2), 205–265 (1994)
Shanahan, M.: Prediction is deduction but explanation is abduction. In: International Joint Conference on Artificial Intelligence, pp. 1055–1060 (1989)
Kakas, A.C., Kowalski, R.A., Toni, F.: Abductive logic programming. Journal of Logic and Computation 2(6), 719–770 (1992)
Tamaki, H., Sato, T.: OLD resolution with tabulation. In: Third international conference on logic programming, pp. 84–98 (1986)
Dietrich, S.W.: Extension tables: Memo relations in logic programming. In: Symposium on Logic Programming, pp. 264–272 (1987)
Chen, W., Warren, D.S.: Tabled evaluation with delaying for general logic programs. Journal of the ACM 43(1), 20–74 (1996)
Toman, D.: Memoing evaluation for constraint extensions of Datalog. Constraints 2(3/4), 337–359 (1997)
Becker, M.Y., Sewell, P.: Cassandra: Flexible trust management, applied to electronic health records. In: 17th IEEE Computer Security Foundations Workshop (CSFW), pp. 139–154. IEEE Computer Society Press, Los Alamitos (2004)
Becker, M.Y., Fournet, C., Gordon, A.D.: Design and semantics of a decentralized authorization language. In: Computer Security Foundations Symposium (2007)
Becker, M.Y.: Information governance in NHS’s NPfIT: A case for policy specification. International Journal of Medical Informatics 76(5-6) (2007)
Chen, S., Wijesekera, D., Jajodia, S.: Incorporating dynamic constraints in the flexible authorization framework. In: Samarati, P., Ryan, P.Y.A., Gollmann, D., Molva, R. (eds.) ESORICS 2004. LNCS, vol. 3193, pp. 1–16. Springer, Heidelberg (2004)
Jagadeesan, R., Marrero, W., Pitcher, C., Saraswat, V.: Timed constraint programming: a declarative approach to usage control. In: International Conference on Principles and Practice of Declarative Programming, pp. 164–175 (2005)
Damianou, N., Dulay, N., Lupu, E., Sloman, M.: The Ponder policy specification language. In: International Workshop on Policies for Distributed Systems and Networks, pp. 18–38 (2001)
OASIS: eXtensible Access Control Markup Language (XACML) Version 2.0 core specification (2005)
Li, N., Tripunitara, M.V.: Security analysis in role-based access control. In: Symposium on Access Control Models and Technologies, pp. 126–135 (2004)
Li, N., Mitchell, J.C., Winsborough, W.H.: Beyond proof-of-compliance: security analysis in trust management. Journal of the ACM 52(3), 474–514 (2005)
Sasturkar, A., Yang, P., Stoller, S.D., Ramakrishnan, C.R.: Policy analysis for administrative role based access control. In: Workshop on Computer Security Foundations, pp. 124–138 (2006)
Sandhu, R., Bhamidipati, V., Coyne, E., Canta, S., Youman, C.: The ARBAC97 model for role-based administration of roles: Preliminary description and outline. In: 2nd ACM Workshop on Role-Based Access Control, pp. 41–54. ACM Press, New York (1997)
Jha, S., Reps, T.: Analysis of SPKI/SDSI certificates using model checking. In: Computer Security Foundations Workshop (2002)
Bertino, E., Catania, B., Ferrari, E., Perlasca, P.: A logical framework for reasoning about access control models. ACM Trans. Inf. Syst. Secur. 6(1), 71–127 (2003)
Fisler, K., Krishnamurthi, S., Meyerovich, L.A., Tschantz, M.C.: Verification and change-impact analysis of access-control policies. In: Inverardi, P., Jazayeri, M. (eds.) ICSE 2005. LNCS, vol. 4309, pp. 196–205. Springer, Heidelberg (2006)
Pucella, R., Weissman, V.: Reasoning about dynamic policies. In: Foundations of Software Science and Computation Structures, pp. 453–467 (2004)
Dougherty, D.J., Fisler, K., Krishnamurthi, S.: Specifying and reasoning about dynamic access-control policies. In: Furbach, U., Shankar, N. (eds.) IJCAR 2006. LNCS (LNAI), vol. 4130, pp. 632–646. Springer, Heidelberg (2006)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Becker, M.Y., Nanz, S. (2007). A Logic for State-Modifying Authorization Policies. In: Biskup, J., López, J. (eds) Computer Security – ESORICS 2007. ESORICS 2007. Lecture Notes in Computer Science, vol 4734. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-74835-9_14
Download citation
DOI: https://doi.org/10.1007/978-3-540-74835-9_14
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-74834-2
Online ISBN: 978-3-540-74835-9
eBook Packages: Computer ScienceComputer Science (R0)