Abstract
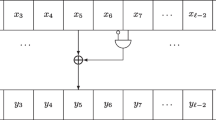
Differential Power Analysis (DPA) has turned out to be an efficient method to attack the implementations of cryptographic algorithms and has been well studied for ciphers that incorporate a nonlinear substitution box as e.g. in DES. Other product ciphers and message authentication codes are based on the mixing of different algebraic groups and do not use look-up tables. Among these are IDEA, the AES finalist RC6 and HMAC-constructions such as HMAC-SHA-1 and HMAC-RIPEMD-160. These algorithms restrict the use of the selection function to the Hamming weight and Hamming distance of intermediate data as the addresses used do not depend on cryptographic keys. Because of the linearity of the primitive operations secondary DPA signals arise. This article gives a deeper analysis of the characteristics of DPA results obtained on the basic group operations XOR, addition modulo 2n and modular multiplication using multi-bit selection functions. The results shown are based both on simulation and experimental data. Experimental results are included for an AVR ATM163 microcontroller which demonstrate the application of DPA to an IDEA implementation.
Chapter PDF
Similar content being viewed by others
References
Chari, S., Jutla, C., Rao, J.R., Rohatgi, P.: A Cautionary Note Regarding Evaluation of AES Candidates on Smart-Cards. In: Proceedings of the second AES conference, pp. 135–150 (1999)
Kocher, P., Jaffe, J., Jun, B.: Differential Power Analysis. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 388–397. Springer, Heidelberg (1999)
Messerges, T., Dabbish, E., Sloan, R.: Investigation of Power Analysis Attacks on Smartcards. In: USENIX Workshop on Smartcard Techonolgy, USENIX Association, pp. 151–161 (1999)
Mayer-Sommer, R.: Smartly Analyzing the Simplicity and the Power of Simple Power Analysis on Smartcards. In: Paar, C., Koç, Ç.K. (eds.) CHES 2000. LNCS, vol. 1965, pp. 78–92. Springer, Heidelberg (2000)
Aigner, M., Oswald, E.: Power Analysis Tutorial, available at http://www.iaik.tugraz.ac.at/aboutus/people/oswald/papers/dpa_tutorial.pdf
Oswald, E., Preneel, B.: A Theoretical Evaluation of some NESSIE Candidates regarding their Susceptibility towards Power Analysis Attacks, October 4 (2002), available at http://www.cosic.esat.kuleuven.ac.be/nessie/reports/phase2/kulwp5-022-1.pdf
Kelsey, J., Schneier, B., Wagner, D., Hall, C.: Side Channel Cryptanalysis of Product Ciphers. Journal of Computer Security 8(2-3), 141–158 (2000)
Brier, E., Clavier, C., Olivier, F.: Optimal Statistical Power Analysis, IACR Cryptology ePrint Archive, Report 2003/152, available at: http://eprint.iacr.org/2003/152.pdf
Goubin, L.: A sound method for switching between boolean and arithmetic masking. In: Koç, Ç.K., Naccache, D., Paar, C. (eds.) CHES 2001. LNCS, vol. 2162, pp. 3–15. Springer, Heidelberg (2001)
Coron, J.-S., Tchulkine, A.: A New Algorithm for Switching from Arithmetic to Boolean Masking. In: Walter, C.D., Koç, Ç.K., Paar, C. (eds.) CHES 2003. LNCS, vol. 2779, pp. 89–97. Springer, Heidelberg (2003)
Lai, X., Massey, J.L.: Markov ciphers and differential cryptanalysis. In: Davies, D.W. (ed.) EUROCRYPT 1991. LNCS, vol. 547, pp. 17–38. Springer, Heidelberg (1991)
Rivest, R.L., Robshaw, M.J.B., Sidney, R., Yin, X.L.: The RC6TM Block Cipher, Version 1.1, August 20 (1998)
Bellare, M., Canetti, R., Krawczyk, H.: Message Authentication using Hash Functions — The HMAC Construction. RSA Laboratories’ CryptoBytes 2(1) (1996)
Bellare, M., Canetti, R., Krawczyk, H.: Keying hash functions for message authentication. In: Koblitz, N. (ed.) CRYPTO 1996. LNCS, vol. 1109, pp. 1–15. Springer, Heidelberg (1996)
Dobbertin, H., Bosselaers, A., Preneel, B.: RIPEMD-160: A Strengthened Version of RIPEMD. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, pp. 71–82. Springer, Heidelberg (1996), http://www.esat.kuleuven.ac.be/~cosicart/pdf/AB-9601/AB-9601.pdf
Menezes, A., van Oorschot, P., Vanstone, S.: Handbook of Applied Cryptography. CRC Press, Boca Raton (1996)
ATmega163 ATmega163L, 8-bit AVR Microcontroller with 16K Bytes In-System Programmable Flash, Rev. 1142E-AVR-02/03, Atmel, available at www.atmel.com
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Lemke, K., Schramm, K., Paar, C. (2004). DPA on n-Bit Sized Boolean and Arithmetic Operations and Its Application to IDEA, RC6, and the HMAC-Construction. In: Joye, M., Quisquater, JJ. (eds) Cryptographic Hardware and Embedded Systems - CHES 2004. CHES 2004. Lecture Notes in Computer Science, vol 3156. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-28632-5_15
Download citation
DOI: https://doi.org/10.1007/978-3-540-28632-5_15
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-22666-6
Online ISBN: 978-3-540-28632-5
eBook Packages: Springer Book Archive