Abstract
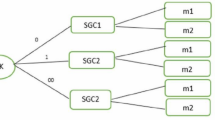
In many of the sensor network applications like natural habitat monitoring and international border monitoring, sensor networks are deployed in areas, where there is a high possibility of node capture and network level attacks. Specifically in such applications, the sensor nodes are severely limited in resources. We propose MUQAMI, a locally distributed key management scheme for resilience against the node capture in wireless sensor networks. Our scheme is efficient both in case of keying, re-keying and node compromise. Beauty of our scheme is that it requires minimal message transmission outside the cluster. We base our Scheme on Exclusion Basis System (EBS).
Please use the following formal when citing this chapter: Raazi, S. M. K., Khan, A. M, Khan, F. I., Lee, S. Y., Song, Y. J. and Lee, Y. K., 2007, in IFIP International Federation for Information Processing, Voiume 238, Trust Management, eds. Etalle, S., Marsh, S., (Boston: Springer), pp. 333–348.
Chapter PDF
Similar content being viewed by others
References
I.F. Akyildiz, W. Su, Y. Sankarasubramaniam, and E. Cayirci, Wireless Sensor Networks: A Survey, Computer Networks 38(4), 393–422 (2002).
S. Tilak, N.B. Abu-Ghazaleh, and W. Heinzelman, A Taxonomy of Wireless Microsensor Network Models, ACM Mobile Computing and Comm. Rev. 6(2), 1–8 (2002).
M. Eltoweissy, H. Heydari, L. Morales, and H. Sadborough, Combinatorial Optimization of Group Key Management, J. Network and Systems Management 12(1), 33–50 (2004).
G. Dini and I.M. Savino, An Efficient Key Revocation Protocol for Wireless Sensor Networks, International Workshop on Wireless Mobile Multimedia, Proceedings of the 2006 International Symposium on World of Wireless, Mobile and Multimedia Networks, 450–452 (2006).
L. Lamport, Password authentication with insecure communication, Communications of the ACM 24(11), 770–772 (1981).
M. Younis, K. Ghumman, and M. Eltoweissy, Location aware Combinatorial Key Management Scheme for Clustered Sensor Networks, IEEE Trans. Parallel and Distrib. Sys. 17(8), 865–882 (2006).
G. Gupta and M. Younis, Load-Balanced Clustering of Wireless Sensor Networks, Proc. Int’l Conf. Comm. (ICC’ 03), 1848–1852 (2003).
O. Younis and S. Fahmy, HEED: A Hybrid, Energy-Efficient, Distributed lustering Approach for Ad Hoc Sensor Networks, IEEE Trans. Mobile Computing 3(4), 366–379 (2004).
K. Langendoen and N. Reijers, Distributed Localization in Wireless Sensor Networks: A Quantitative Comparison, Computer Networks 43(4), 499–518 (2003).
A. Youssef, A. Agrawala, and M. Younis, Accurate Anchor-Free Localization in Wireless Sensor Networks, Proc. First IEEE Workshop Information Assurance in Wireless Sensor Networks (WSNIA’ 05), (2005).
R.L. Rivest, A. Shamir, and L. Adleman, A method for obtaining digital signatures and public-key cryptosystems, Comm. of the ACM 21(2), 120–126 (1978).
A.J. Menezes, P.C.V. Oorschot, and S.A. Vanstone, Handbook of Applied Cryptography, CRC Press, (1996).
D. Eastlake and P. Jones, US Secure Hash Algorithm 1 (SHA-1), RFC 3174, IETF, (2001).
R. Rivest, The MD5 Message-Digest Algorithm, RFC 1320, MIT and RSA Data Security Inc., (1992).
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2007 International Federation for Information Processing
About this paper
Cite this paper
Raazi, S.M.KuR., Khan, A.M., Khan, F.I., Lee, S.Y., Song, Y.J., Lee, Y.K. (2007). MUQAMI: A Locally Distributed Key Management Scheme for Clustered Sensor Networks. In: Etalle, S., Marsh, S. (eds) Trust Management. IFIPTM 2007. IFIP International Federation for Information Processing, vol 238. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-73655-6_22
Download citation
DOI: https://doi.org/10.1007/978-0-387-73655-6_22
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-387-73654-9
Online ISBN: 978-0-387-73655-6
eBook Packages: Computer ScienceComputer Science (R0)