Abstract
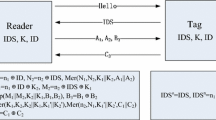
In this paper, we analyze the security vulnerabilities of two ultra-lightweight RFID mutual authentication protocols: LMAP and M2 AP, which are recently proposed by Peris-Lopez et al. We identify two effective attacks, namely Desynchronization attack and Fulldisclosure attack, against their protocols. The former attack can break the synchronization between the RFID reader and the tag in a single protocol run so that they can not authenticate each other in any following protocol runs. The latter attack can disclose all the secret information stored on a tag by interrogating the tag multiple times. Thus it compromises the tag completely. Moreover, we point out the potential countermeasures to improve the security of above protocols.
Please use the following format when citing this chapter: Li, T. and Wang, G., 2007, in 1F1P international Federation for Information Processing, Volume 232, New Approaches for Security, Privacy and Trust in Complex Environments, eds. Venter, H., Etoff, M., Labuschagne, L., Eloff, J., von Solms. R., (Boston: Springer), pp. 109–120.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
M. Aigner and M. Feldhofer. Secure Symmetric Authentication for RFID Tags. Telecommunication and Mobile Computing, March 2005.
G. Avoine. Security and Privacy in RFID Systems, http://lasecwww.epfl.ch/gavoine/rfid
B. Defend, K. Fu and A. Juels. Cryptanalysis of Two Lightweight RFID Authentication Schemes. In: Proc. of PERSEC’07, March 2007.
A. Juels and R. Pappu. Squealing euros: Privacy protection in RFID-enabled banknotes. In: Proc. of FC’03, LNCS 2742, pp. 103–121. Springer-Verlag, 2003.
A. Juels. Minimalist Cryptography for Low-Cost RFID Tags. In: Proc. of SCN’04, LNCS 3352, pp. 149–164. Springer-Verlag, 2004.
A. Juels and S. Weis. Authenticating pervasive devices with human protocols. In: Proc. of CRYPTO’05, LNCS 3126, pp. 293–308. Springer-Verlag, 2005.
A. Juels. RFID Security and Privacy: A Research Survey. IEEE Journal on Selected Areas in Communications, 24(2): 381–394, Feb. 2006.
H. Lipmaa and S. Moriai. Efficient Algorithms for Computing Differential Properties of Addition. In: Proc. of FSE’ 01, LNCS 2355, pp. 336–350. Springer-Verlag, 2001.
D. Molnar and D. Wagner. Privacy and Security in Library RFID: Issues, Practices, and Architectures. In: Proc. of CCS’04, pp. 210–219. ACM Press, 2004.
D. Molnar, A. Soppera, and D. Wagner. A Scalable, Delegatable Pseudonym Protocol Enabling Ownership Transfer of RFID Tags. In: Proc. of SAC’05, LNCS 3897, pp. 276–290. Springer-Verlag, 2005.
M. Ohkubo, K. Suzuki, and S. Kinoshita. Cryptographic approach to privacyfriendly tags. In: Proc. of RFID Privacy Workshop, 2003.
P. Peris-Lopez, J. C. Hernandez-Castro, J. M. Estevez-Tapiador, and A. Ribagorda. LMAP: A Real Lightweight Mutual Authentication Protocol for Low-cost RFID tags. In: Proc. of 2nd Workshop on RFID Security, July 2006. http://events.iaik.tugraz.at/RFIDSecO6.
P. Peris-Lopez, J. C. Hernandez-Castro, J. M. Estevez-Tapiador, and A. Ribagorda. M2AP: A Minimalist Mutual-Authentication Protocol for Low-cost RFID Tags. In: Proc. of International Conference on Ubiquitous Intelligence and Computing UIC’06, LNCS 4159, pp. 912–923. Springer-Verlag, 2006.
I. Vajda and L. Buttyan. Lightweight authentication protocols for low-cost RFID tags. In: Proc. of UBICOMP’03, 2003.
S. Weis, S. Sarma, R. Rivest, and D. Engels. Security and privacy aspects of lowcost radio frequency identification systems. In: Proc. of 1st Int. Conf. on Security in Pervasive Computing, LNCS 2802, pp. 201–212. Springer-Verlag, 2003.
S. Weis. Security parallels between people and pervasive devices. In: Proc. of PERSEC’05, pp. 105–109. IEEE Computer Society Press, 2005.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2007 International Federation for Information Processing
About this paper
Cite this paper
Li, T., Wang, G. (2007). Security Analysis of Two Ultra-Lightweight RFID Authentication Protocols. In: Venter, H., Eloff, M., Labuschagne, L., Eloff, J., von Solms, R. (eds) New Approaches for Security, Privacy and Trust in Complex Environments. SEC 2007. IFIP International Federation for Information Processing, vol 232. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-72367-9_10
Download citation
DOI: https://doi.org/10.1007/978-0-387-72367-9_10
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-387-72366-2
Online ISBN: 978-0-387-72367-9
eBook Packages: Computer ScienceComputer Science (R0)