Summary
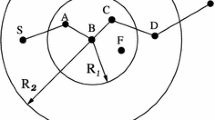
We propose in this paper a protocol, called QITAR, which will secure the ad-hoc routing process while guaranteeing end-to-end QoS requirements in terms of delay or bandwidth constraints. Our approach provides an intrusion tolerant environment and uses and enhances the concept of Trusted Timely Computing Base in order to deduce consistent delay information and verify the bandwidth value pretended by untrusted nodes. QITAR also proposes a rescue procedure that saves the resources and accelerates the route maintenance in case of node mobility.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
C. Perkins, E. M. Royer and S. R. Das, “Ad hoc On-demand Distance Vector routing”, In IETF Internet Draft, draft-ietf-manet-AODV-12.txt, November 2002.
D.B Johnson, D.A Maltz and J. Broch, “DSR: The dynamic Source Routing Protocol for Multi-hop wireless Ad Hoc Networks”, in Ad Hoc Networking, ch. 5, pp. 139–172, Addison-Wesley, 2001.
C.E. Perkins and P. Bhagwat, “Highly Dynamic Destination-Sequenced Distance Vector Routing (DSDV) for Mobile Computers”, in ACM SIGCOMM—94, October 1994.
N. Ferreira and P. Verrissimo, “Complete Specification of APIs and Protocols for the MAFTIA Middleware”, MAFTIA deliverable D9, 2002.
S. Bouam and J. Ben Othman, “Securing Data Transmission and Retransmissions Management in Ad Hoc Networks”, Proceedings of the International Conference on Wireless Networks, ICWN —04, June 2004.
M. G. Zapata and N. Asokan, “Securing Ad Hoc Routing Protocols”, in WiSe—02, September 2002.
P. Papadimitratos and Z. J. Haas, “Secure Routing for Mobile Ad Hoc Networks”, In proceedings of the CNDS conference, San Antonio, TX, 2002.
B. Awerbuch, R. Curtmola, D. Holmer, C. Nita-Rotaru and H. Rubens, “ODSBR: An On-Demand Secure Byzantine Routing Protocol”, Technical report, October 2003.
C. E. Perkins, E. M. Royer and S. R. Das, “Quality of Service for Ad hoc On-demand Distance Vector Routing”, IETF Internet Draft, work in progress, July 2000.
G.S. Ahn, A.T. Campbell, A. Veres and L.H. Sun, “SWAN: Service Differentiation in Stateless Wireless Ad Hoc Networks”, Proceedings of IEEE INFOCOM 2002, June 2002.
D. Powell and R. Stroud, “Conceptual Model and Architecture of MAFTIA”, MAFTIA deliverable D21, 2003.
K. Xu, K. Tang, R. Bagrodia, M. Gerla, M. Bereschinsky, “Adaptive Bandwidth Management and QoS Provisioning in Large Scale Ad Hoc Networks”, IEEE MILCOM—03, Boston, Massachusetts, October 2003
S. Lohier, S. M. Senouci, Y. M. Ghamri. Doudane and G. Pujolle, “A reactive QoS Routing Protocol for Ad Hoc Networks”, European Symposium on Ambient Intelligence (EUSAI2003), Eindhoven, Netherlands, November 2003, Lecture Notes in Computer Science, Springer Verlag.
D. Powell and R. Stroud, “Conceptual Model and Architecture of MAFTIA”, MAFTIA deliverable D21, 2003.
Y. C. Hu, A. Perrig and D. B. Johnson, “Packet Leashes: A Defense against Wormhole Attacks in Wireless Ad Hoc Networks”, Technical report TR01-384, Revised September 2002.
M. Kazantzidis and M. Gerla, “End-to-end versus Explicit Feedback Measurement in 802.11 Networks”, In Seventh IEEE Symposium on Computers and Communications, 2002.
H. Badis, A. Munaretto, K. Al Agha and G. Pujolle, “QoS for Ad hoc Networking Based on Multiple Metrics: Bandwidth and Delay”, IFIP/IEEE MWCN 2003, Singapore, October 27–29, 2003.
W. Yu, Y. Sun and K. J. R. Liu, “HADOF: Defense Against Routing Disruptions in Mobile Ad Hoc Networks”, in Proc. IEEE INFOCOM—04, Hong Kong 2004.
B. Awerbuch, D. Holmer and H. Rubens, “Provably Secure Competitive Routing against Proactive Byzantine Adversaries via Reinforcement Learning”, John Hopkings Univ, Tech. Rep, May 2003.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 International Federation for Information Processing
About this paper
Cite this paper
Krichene, N., Boudriga, N. (2006). On a QoS Intrusion Tolerant Routing protocol in Ad-hoc Networks. In: Al Agha, K. (eds) Ad-Hoc Networking. IFIP International Federation for Information Processing, vol 212. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-34738-7_3
Download citation
DOI: https://doi.org/10.1007/978-0-387-34738-7_3
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-387-34635-9
Online ISBN: 978-0-387-34738-7
eBook Packages: Computer ScienceComputer Science (R0)