Abstract
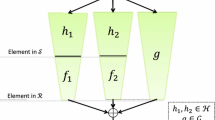
The generalized knapsack function is defined as f a (x) = ∑ i a i ·x i , where a = (a1,...,am) consists of m elements from some ring R, and x = (x1,...,xm) consists of m coefficients from a specified subset S ⊆ R. Micciancio (FOCS 2002) proposed a specific choice of the ring R and subset S for which inverting this function (for random a,x) is at least as hard as solving certain worst-case problems on cyclic lattices.
We show that for a different choice of S ⊂ R, the generalized knapsack function is in fact collision-resistant, assuming it is infeasible to approximate the shortest vector in n-dimensional cyclic lattices up to factors \(\tilde{O}(n)\). For slightly larger factors, we even get collision-resistance for anym≥ 2. This yields very efficient collision-resistant hash functions having key size and time complexity almost linear in the security parameter n. We also show that altering S is necessary, in the sense that Micciancio’s original function is not collision-resistant (nor even universal one-way).
Our results exploit an intimate connection between the linear algebra of n-dimensional cyclic lattices and the ring ℤ[α]/(α n − 1), and crucially depend on the factorization of α n-1 into irreducible cyclotomic polynomials. We also establish a new bound on the discrete Gaussian distribution over general lattices, employing techniques introduced by Micciancio and Regev (FOCS 2004) and also used by Micciancio in his study of compact knapsacks.
Part of this work done while at MIT CSAIL.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-3-540-32732-5_32
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Ajtai, M.: Generating hard instances of lattice problems (extended abstract). In: Proc. 28th Annual ACM Symposium on Theory of Computing (STOC 1996), pp. 99–108 (1996)
Ajtai, M.: The shortest vector problem in L2 is NP-hard for randomized reductions (extended abstract). In: Proc. 30th Annual ACM Symposium on Theory of Computing (STOC 1998), pp. 10–19 (1998)
Ajtai, M., Dwork, C.: A public-key cryptosystem with worst-case/average-case equivalence. In: Proc. 29th Annual ACM Symposium on Theory of Computing (STOC 1997), pp. 284–293 (1997)
Arora, S., Babai, L., Stern, J., Sweedyk, Z.: The hardness of approximate optima in lattices, codes, and systems of linear equations. J. Computer and System Sciences 54(2), 317–331 (1997)
Cai, J.-Y., Nerurkar, A.: Approximating the SVP to within a factor (1 + 1/dimε) is NP-hard under randomized reductions. Jounal of Computer and System Sciences 59(2), 221–239 (1999)
Cai, J.-Y., Nerurkar, A.P.: An improved worst-case to average-case connection for lattice problems. In: Proc. 38th Annual Symposium on Foundations of Computer Science (FOCS 1997), p. 468 (1997)
Dinur, I., Kindler, G., Safra, S.: Approximating-CVP to within almostpolynomial factors is NP-hard. In: Proc. 39th Annual Symposium on Foundations of Computer Science (FOCS 1998), pp. 99–111. IEEE Computer Society, Los Alamitos (1998)
Dummit, D.S., Foote, R.M.: Abstract Algebra, 2nd edn. Prentice Hall, Upper Saddle River (1999)
Genarro, R., Gertner, Y., Katz, J., Trevisan, L.: Bounds on the efficiency of generic cryptographic constructions. SIAM J. Computing 35(1), 217–246 (2005)
Goldreich, O., Goldwasser, S., Halevi, S.: Collision-free hashing from lattice problems. Electronic Colloquium on Computational Complexity (ECCC) Report TR96-042 (1996)
Goldreich, O., Goldwasser, S., Halevi, S.: Public-key cryptosystems from lattice reduction problems. In: Kaliski Jr., B.S. (ed.) CRYPTO 1997. LNCS, vol. 1294, pp. 112–131. Springer, Heidelberg (1997)
Khot, S.: Hardness of approximating the shortest vector problem in lattices. In: Proc. 45th Symposium on Foundations of Computer Science (FOCS 2004), pp. 126–135. IEEE Computer Society, Los Alamitos (2004)
Lyubashevsky, V., Micciancio, D.: Generalized compact knapsacks are collision resistant. Electronic Colloquium on Computational Complexity (ECCC) Report TR05-142 (2005)
Micciancio, D.: Generalized compact knapsaks, cyclic lattices, and efficient oneway functions from worst-case complexity assumptions. In: Proc. 43rd Annual Symposium on Foundations of Computer Science (FOCS (2002)
Micciancio, D.: The shortest vector problem is NP-hard to approximate to within some constant. SIAM J. Computing 30(6), 2008–2035 (March 2001)
Micciancio, D., Goldwasser, S.: Complexity of Lattice Problems: a cryptographic perspective. The Kluwer International Series in Engineering and Computer Science, vol. 671. Kluwer Academic Publishers, Boston, Massachusetts (2002)
Micciancio, D., Regev, O.: Worst-case to average-case reductions based on Gaussian measure, pp. 371–381
Regev, O.: New lattice-based cryptographic constructions. J. ACM 51(6), 899–942 (2004)
Regev, O.: On lattices, learning with errors, random linear codes, and cryptography. In: Proc. 37th Annual ACM Symposium on Theory of Computing (STOC 2005), pp. 84–93 (2005)
van Emde Boas, P.: Another NP-complete problem and the complexity of computing short vectors in a lattice. Technical Report 81-04, University of Amsterdam (1981)
Wang, X., Yin, Y.L., Yu, H.: Finding collisions in the full SHA-1. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 17–36. Springer, Heidelberg (2005)
Wang, X., Yu, H.: How to break MD5 and other hash functions. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 19–35. Springer, Heidelberg (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Peikert, C., Rosen, A. (2006). Efficient Collision-Resistant Hashing from Worst-Case Assumptions on Cyclic Lattices. In: Halevi, S., Rabin, T. (eds) Theory of Cryptography. TCC 2006. Lecture Notes in Computer Science, vol 3876. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11681878_8
Download citation
DOI: https://doi.org/10.1007/11681878_8
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-32731-8
Online ISBN: 978-3-540-32732-5
eBook Packages: Computer ScienceComputer Science (R0)