Abstract
Cross-site scripting (XSS) vulnerabilities are among the most prevailing problems on the web. Among the practically deployed countermeasures is a“defense-in-depth” Content Security Policy (CSP) to mitigate the effects of XSS attacks. However, the adoption of CSP has been frustratingly slow. This paper focuses on a particular roadblock for wider adoption of CSP: its interplay with browser extensions.
We report on a large-scale empirical study of all free extensions from Google’s Chrome web store that uncovers three classes of vulnerabilities arising from the tension between the power of extensions and CSP intended by web pages: third party code inclusion, enabling XSS, and user profiling. We discover extensions with over a million users in each vulnerable category.
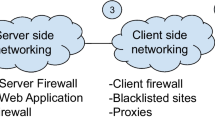
With the goal to facilitate a wider adoption of CSP, we propose an extension-aware CSP endorsement mechanism between the server and client. A case study with the Rapportive extensions for Firefox and Chrome demonstrates the practicality of the approach.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
- 2.
The actual name of the event depends on the browser implementation.
References
Van Acker, S., Nikiforakis, N., Desmet, L., Piessens, F., Joosen, W.: Monkey-in-the-browser: malware and vulnerabilities in augmented browsing script markets. In: ASIA CCS 2014 (2014)
Bandhakavi, S., Tiku, N., Pittman, W., King, S.T., Madhusudan, P., Winslett, M.: Vetting browser extensions for security vulnerabilities with VEX. Commun. ACM 54(9), 91–99 (2011). doi:10.1145/1995376.1995398
Barth, A., Porter Felt, A., Saxena, P., Boodman, A.: Protecting browsers from extension vulnerabilities. In: NDSS (2010)
Barua, A., Zulkernine, M., Weldemariam, K.: Protecting web browser extensions from javascript injection attacks. In: ICECCS (2013)
Bauer, L., Cai, S., Jia, L., Passaro, T., Tian, Y.: Analyzing the dangers posed by Chrome extensions. In: IEEE CNS (2014)
BuiltWith. Content security policy usage statistics. http://trends.builtwith.com/docinfo/Content-Security-Policy. (Accessed Februrary 2015)
Chang, W., Chen, S.: Defeat information leakage from browser extensions via data obfuscation. In: Qing, S., Zhou, J., Liu, D. (eds.) ICICS 2013. LNCS, vol. 8233, pp. 33–48. Springer, Heidelberg (2013)
Dhawan, M., Ganapathy, V.: Analyzing information flow in javascript-based browser extensions. In: ACSAC (2009)
Fazzini, M., Saxena, P., Orso, A.: AutoCSP: Automatically Retrofitting CSP to Web Applications (2015)
Google. Chrome web store. https://chrome.google.com/webstore/category/extensions. (Accessed February 2015)
Google. Chromium. http://dev.chromium.org/Home. (Accessed February 2015)
Google. Content security policy (csp) - google chrome. https://developer.chrome.com/extensions/contentSecurityPolicy. (Accessed February 2015)
Google. Gmail. https://www.gmail.com/. (Accessed February 2015)
Google. Reject the unexpected - content security policy in gmail. http://gmailblog.blogspot.se/2014/12/reject-unexpected-content-security.html. (Accessed Februrary 2015)
Heule, S., Rifkin, D., Stefan, D., Russo, A.: The most dangerous code in the browser. In: HotOS (2015)
Javed, A.: CSP AiDer: An automated recommendation of content security policy for web applications. In: Poster at IEEE Symposium on Security & Privacy (2011)
Joyent. Node.js. http://www.nodejs.org/. (Accessed February 2015)
Kapravelos, A., Grier, C., Chachra, N., Kruegel, C., Vigna, G., Paxson, V.: Hulk: Eliciting Malicious Behavior in Browser Extensions. In: USENIX Sec. (2014)
Karim, R., Dhawan, M., Ganapathy, V., Shan, C.: An analysis of the mozilla jetpack extension framework. In: Noble, J. (ed.) ECOOP 2012. LNCS, vol. 7313, pp. 333–355. Springer, Heidelberg (2012)
LinkedIn. Rapportive. http://rapportive.com/. (Accessed February 2015)
Maggi, F., Frossi, A., Zanero, S., Stringhini, G., Stone-Gross, B., Kruegel, C., Vigna, G.: Two years of short urls internet measurement: security threats and countermeasures. In: WWW (2013)
mitmproxy. https://mitmproxy.org/. (Accessed February 2015)
Mozilla. Firefox nightly. https://nightly.mozilla.org/. (Accessed February 2015)
Nikiforakis, N., Invernizzi, L., Kapravelos, A., Van Acker, S., Joosen, W., Kruegel, C., Piessens, Vigna, G.: You are what you include: Large-scale evaluation of remote javascript inclusions. In: CCS (2012)
OWASP. Clickjacking. https://www.owasp.org/index.php/Clickjacking. (Accessed February 2015)
OWASP. Content security policy. https://www.owasp.org/index.php/Content_Security_Policy. (Accessed February 2015)
OWASP. Cross-site scripting (Accessed February 2015)
OWASP. Top 10 2013. https://www.owasp.org/index.php/Top_10_2013. (Accessed February 2015)
Patil, K., Vyas, T., Braun, F., Goodwin, M., Liang, Z.: Poster: UserCSP - User Specified Content Security Policies. In: SOUPS (2013)
Rapportive : Reviews : Add-ons for firefox. https://addons.mozilla.org/en-US/firefox/addon/rapportive/reviews/. (Accessed February 2015)
Syrian Electronic Army uses Taboola ad to hack Reuters (again). https://nakedsecurity.sophos.com/2014/06/23/syrian-electronic-army-uses-taboola-ad-to-hack-reuters-again/
Shahriar, H., Weldemariam, K., Zulkernine, M., Lutellier, T.: Effective detection of vulnerable and malicious browser extensions. Comput. Secur. 47, 66–84 (2014). doi:10.1016/j.cose.2014.06.005
Sterne, B.: Content security policy recommendation bookmarklet. http://brandon.sternefamily.net/2010/10/content-security-policy-recommendation-bookmarklet/. (Accessed February 2015)
Taboola. Taboola | drive traffic and monetize your site. http://www.taboola.com/. (Accessed February 2015)
Can I Use. Content security policy 1.0. (Accessed February 2015)
W3C. Csp 1.0. http://www.w3.org/TR/CSP/. (Accessed February 2015)
W3C. Csp 2.0. http://www.w3.org/TR/CSP2/. (Accessed February 2015)
W3C. World wide web consortium. http://www.w3.org/. (Accessed February 2015)
Weissbacher, M., Lauinger, T., Robertson, W.: Why Is CSP failing? trends and challenges in CSP adoption. In: Stavrou, A., Bos, H., Portokalidis, G. (eds.) RAID 2014. LNCS, vol. 8688, pp. 212–233. Springer, Heidelberg (2014)
WhiteHat. Content security policy - whitehat security blog. https://blog.whitehatsec.com/content-security-policy/. (Accessed February 2015)
Acknowledgments
Thanks are due to Federico Maggi, Adrienne Porter Felt, and the anonymous reviewers for the helpful comments and feedback. This work was funded by the European Community under the ProSecuToR and WebSand projects and the Swedish research agencies SSF and VR.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
A Gmail CSP policy (12. January 2015)
A Gmail CSP policy (12. January 2015)

Rights and permissions
Copyright information
© 2015 Springer International Publishing Switzerland
About this paper
Cite this paper
Hausknecht, D., Magazinius, J., Sabelfeld, A. (2015). May I? - Content Security Policy Endorsement for Browser Extensions. In: Almgren, M., Gulisano, V., Maggi, F. (eds) Detection of Intrusions and Malware, and Vulnerability Assessment. DIMVA 2015. Lecture Notes in Computer Science(), vol 9148. Springer, Cham. https://doi.org/10.1007/978-3-319-20550-2_14
Download citation
DOI: https://doi.org/10.1007/978-3-319-20550-2_14
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-20549-6
Online ISBN: 978-3-319-20550-2
eBook Packages: Computer ScienceComputer Science (R0)