Abstract
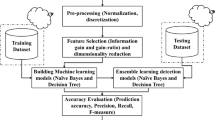
Cloud services in fog network is a platform that inherits software services to a network to handle cloud-specific problems. A significant component of the security paradigm that supports service quality is represented by intrusion detection systems (IDSs). This work develops an optimization environment to mitigate intrusion using RSLO classifier on a cloud-based fog networks. Here, a three-layer approach namely the cloud, end point, and fog layers is used as a trio to carry out all of the processing. In the cloud layer, three layers of processing are required for handling the dataset metrics which are data transformation metrics, feature selection metrics, and classification processes. With log transformation, data is transformed using KS correlation-based filter which is used to choose a feature. The classification using an ensemble methodology of RideNN classifiers which is a Rider Sea Lion Optimization (RSLO), a created classifier, is used to tune the ensemble classifier. Physical work is carried out at another layer called an end point layer. A trained ensemble classifier is used for intrusion detection in the fog layer. A greater precision, recall, and F-measure were obtained with an accuracy approximately 95%, with all benefits of the suggested RSLO-based ensemble strategy.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
An X, Zhou X, Lü X, Lin F, Yang L (2018) Sample selected extreme learning machine based intrusion detection in fog computing and MEC. Wirel Comm Mob Comp
Sadaf K, Sultana J (2020) Intrusion detection based on autoencoder and isolation forest in fog computing. IEEE Access 8:167059–167068
Thorat VA (2021) Cloud intrusion detection using modified crow search optimized based neural network. J Netw Commun Syst 4(2):9–15
Ram Kumar MP, Daniya T, Mano Paul P, Raja Kumar S (2022) Intrusion detection using optimized ensemble classification in fog computing paradigm. Knowl-Based Syst. Elsevier, ISSN: 0950-7051
Selvaraj JD, Jingle ID, Paul PM (2019) EShield: an effective detection and mitigation of flooding in DDoS attacks over large scale networks. IJEAT 8(5). ISSN: 2249-8958
An X, Su J, Lü X, Lin F (2018) Lin, Hypergraph clustering model-based association analysis of DDOS attacks in fog computing intrusion detection system. EURASIP J WCN
Chang V, Golightly L, Modesti P, Xu QA, Doan LM, Hall K, Boddu S, Kobusińska A (2022) A survey on intrusion detection systems for fog and cloud computing. Future Internet 14(3):1–27
Paul PM, Ravi R (2018) A collaborative reputation-based vector space model for email spam filtering. J Comput Theoret Nanosci 15(2):474–479. American Scientific Publishers
An X, Lin F, Xu S, Miao L, Gong C (2018) A novel differential game modelbased intrusion response strategy in fog computing, Secur Commun Netw
Chen Y, Lin Q, Wei W, Ji J, Wong KC, Coello CA (2022) Intrusion detection using multi-objective evolutionary convolutional neural network for Internet of Things in Fog computing. Knowl-Based Syst 244:108505
Paul PM, Ravi R (2018) Cooperative vector based reactive system for protecting email against spammers in wireless networks. J Electr Eng 18. ISSN: 1582–4594. University politechnica
Stojmenovic I, Wen S (2014) The fog computing paradigm: Scenarios and security issues. In: Federated conference on computer science and information systems, pp 1–8
Li S, Cheng X, Huang X, Otaibi SA, Wang H (2022) Cooperative conflict detection and resolution and safety assessment for 6G enabled unmanned aerial vehicles. IEEE Trans Intell Transp Syst, pp 1–6
Fan S, Fu S, Xu H, Cheng X (2021) Al-SPSD: Anti-leakage smart Ponzi schemes detection in blockchain. Inform Process Manage 58(4):102587
Paul PM, Jingle ID (2019) A novel optimal email feature selection protocol (OEFS) for detecting spam emails. Int J Comput Sci Eng 7(16):34–39
Paul PM, Jingle ID. A privatised approach in enhanced spam filtering techniques using TSAS over cloud networks. Int J Intell Enterpr 9(3):332–343. Inderscience Publishers
Jingle ID, Rajsingh EB, Paul PM (2012) Distributed detection of DoS using clock values in wireless broadband networks. Int J Eng Adv Technol 1(5). ISSN: 2249–8958
Jingle ID, Paul PM (2021) A collaborative defense protocol against collaborative attacks in wireless mesh networks. Int J ENM 12(3):199–220. Inderscience Publishers
Diana Jeba Jingle I, Mano Paul P (2021) A fog-based retrieval of real-time data for health applications. In: Recent trends in signal and image processing, Springer Publications, vol 1, pp 155–160
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Paul, P.M., Shekhar, R., Jingle, I.D.J., Jingle, I.B.J. (2024). Prevention and Mitigation of Intrusion Using an Efficient Ensemble Classification in Fog Computing. In: Devi, B.R., Kumar, K., Raju, M., Raju, K.S., Sellathurai, M. (eds) Proceedings of Fifth International Conference on Computer and Communication Technologies. IC3T 2023. Lecture Notes in Networks and Systems, vol 898. Springer, Singapore. https://doi.org/10.1007/978-981-99-9707-7_16
Download citation
DOI: https://doi.org/10.1007/978-981-99-9707-7_16
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-9706-0
Online ISBN: 978-981-99-9707-7
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)