Abstract
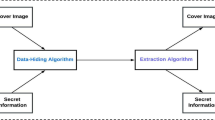
Secure transformation of data over public networks like the Internet is nothing but achieving authenticity, secrecy, and confidentiality in secure data transmission is now the primary concern. These issues may be solved by using data hiding techniques. Steganography, cryptography, and watermarking techniques are used to hide data and ensure its security during transmission. Objective of this submission is to analyze and examine several methods of deep learning in image cryptography and steganography. The hidden message is revealed via steganography, but its format is altered through cryptography. Steganography and cryptography are both essential and robust techniques. This paper’s primary goal is to explore several integrating steganography with encryption to create a hybrid system. In addition, specific differences were also given between cryptography and steganographic approaches. This paper aims to help other researchers’ summaries current trends, problems, and possible future directions in this area.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
El-kenawy E-S, Saber M, Arnous R (2019) An integrated framework to ensure information security over the internet. Int J Comput Appl 178:13–15. https://doi.org/10.5120/ijca2019919117
Alqadi Z (2020) Image blocking to hide secret message. Int J Comput Sci Mob Comput 9. https://doi.org/10.47760/ijcsmc.2020.v09i11.002
Asratian R (2019) Protected message processing in distributed systems on the basis of cryptographic message syntax. Inform Tehnol 25:435–440. https://doi.org/10.17587/it.25.435-440
Chandra P, Suhartana I (2021) Web-based image steganography application to hide secret messages. JELIKU (J Elektr Ilmu Komput Udayana) 9(375). https://doi.org/10.24843/JLK.2021.v09.i03.p08
Zaidan BB, Zaidan AA, Al-Frajat AK, Jalab HA (2010) On the differences between hiding information and cryptography techniques: an overview. J Appl Sci (Faisalabad) 10:1650–1655
Gupta Vibhor, Metha G (2018) Medical data security using cryptography, pp 866–869. https://doi.org/10.1109/CONFLUENCE.2018.8442712
Rahim R, Adyaraka D, Sallu S, Sarimanah E, Hidayat A, Sewang A, Hartinah S (2018) An application data security with lempel-ziv welch and blowfish. Int J Eng Technol (UAE) 7:71–73
Singh A, Gilhotra R (2011) Data security using private key encryption system based on arithmetic coding. Int J Netw Secur Appl (IJNSA) 3. https://doi.org/10.5121/ijnsa.2011.3305
Sheshasaayee A, Anandapriya B (2017) Digital signatures security using cryptography for industrial applications, pp 379–382. https://doi.org/10.1109/ICIMIA.2017.7975640
Lyubashevsky V, Micciancio D (2017) Asymptotically efficient lattice-based digital signatures. J Cryptol 31. https://doi.org/10.1007/s00145-017-9270-z
Khan S, Yousaf MH, Wahid M (2015) Variable least significant bits garyscale image Stegnography. Pak J Sci 67:281–287
Bajwa I, Riasat R (2011) A new perfect hashing based approach for secure stegnography. In: 2011 6th International conference on digital information management, ICDIM 2011. https://doi.org/10.1109/ICDIM.2011.6093325
Islam AU, Khalid F, Shah M, Khan Z, Mahmood T, Khan A, Ali U, Naeem M (2016) An improved image steganography technique based on MSB using bit differencing. In2016 Sixth international conference on innovative computing technology, pp 265–269. https://doi.org/10.1109/INTECH.2016.7845020
Singh A, Singh H (2015) An improved LSB based image steganography technique for RGB images, pp 1–4. https://doi.org/10.1109/ICECCT.2015.7226122
Qu Z, Cheng Z, Liu W, Wang X (2019) A novel quantum image steganography algorithm based on exploiting modification direction. Multimedia Tools Appl 78. https://doi.org/10.1007/s11042-018-6476-5
Dhamija A, Dhaka V (2015) A novel cryptographic and steganographic approach for secure cloud data migration. https://doi.org/10.1109/ICGCIoT.2015.7380486
Pv, Vijay &Vijayalakshmi, V. &Godandapani, Zayaraz (2016) An improved level of security for DNA steganography using hyperelliptic curve cryptography. Wireless Pers Commun 89. https://doi.org/10.1007/s11277-016-3313-x
Balaji P, Murugan K, Srinivasan K, Shridevi S, Shamsudheen S, Hu Y-C (2021) Improved authentication and computation of medical data transmission in the secure IoT using hyperelliptic curve cryptography. J Supercomput. https://doi.org/10.1007/s11227-021-03861-x
Qian Y, Dong J, Wang W, Tan T (2015) Deep learning for steganalysis via convolutional neural networks. In: Proceedings of SPIE—the international society for optical engineering, p 9409. https://doi.org/10.1117/12.2083479
Qian Y, Dong J, Wang W, Tan T (2016) Learning and transferring representations for image steganalysis using convolutional neural network, pp 2752–2756. https://doi.org/10.1109/ICIP.2016.7532860
Duan X, Li B, Guo D, Zhang Z, Ma Y (2020) A coverless steganography method based on generative adversarial network. EURASIP J Image Video Process. https://doi.org/10.1186/s13640-020-00506-6
Chen X, Zhang Z, Qiu A, Xia Z, Xiong N (2020) A novel coverless steganography method based on image selection and StarGAN. IEEE Trans Netw Sci Eng 1–1. https://doi.org/10.1109/TNSE.2020.3041529
Li S, Wang J, Liu P, Wei M, Yan Q (2021) Detection of multiple steganography methods in compressed speech based on code element embedding, Bi-LSTM and CNN with attention mechanisms. IEEE/ACM Trans Audio Speech Lang Process 29:1556–1569. https://doi.org/10.1109/TASLP.2021.3074752
Zhang Z, Liu J, Ke Y, Lei Y, Li J, Zhang M, Yang X (2019) Generative steganography by sampling. IEEE Access 1–1. https://doi.org/10.1109/ACCESS.2019.2920313
Ke Y, Zhang MQ, Liu J, Su TT, Yang XY (2019) Generative steganography with Kerckhoffs’ principle. Multimedia Tools Appl 78(10):13805–13818. https://doi.org/10.1007/s11042-018-6640-y
Yang Z, Xiang L, Zhang S, Sun X, Huang Y (2021) Linguistic generative steganography with enhanced cognitive-imperceptibility. IEEE Signal Process Lett 1–1. https://doi.org/10.1109/LSP.2021.3058889
Yu C, Hu D, Zheng S, Jiang W, Li M, Zhao Z-Q (2021) An improved steganography without embedding based on attention GAN. Peer-to-Peer Netw Appl 14:1–12. https://doi.org/10.1007/s12083-020-01033-x
Chen L, Wang R, Yan D, Wang J (2021) Learning to generate steganographic cover for audio steganography using gan. IEEE Access 1–1. https://doi.org/10.1109/ACCESS.2021.3090445
Chang C-C (2021) Cryptospace invertible steganography with conditional generative adversarial networks. Secur Commun Netw 2021:1–14. https://doi.org/10.1155/2021/5538720
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Sandya, K., Kompella, S. (2023). A Combined Approach of Steganography and Cryptography with Generative Adversarial Networks: Survey. In: Bhateja, V., Sunitha, K.V.N., Chen, YW., Zhang, YD. (eds) Intelligent System Design. Lecture Notes in Networks and Systems, vol 494. Springer, Singapore. https://doi.org/10.1007/978-981-19-4863-3_18
Download citation
DOI: https://doi.org/10.1007/978-981-19-4863-3_18
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-19-4862-6
Online ISBN: 978-981-19-4863-3
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)