Abstract
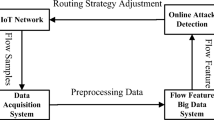
With the advent of fifth-generation network, mobile internet security suffer plenty of DDoS attacks. The number and frequency of occurrence of DDoS attacks are predicted to soar as time goes by, hence there is a need for a sophisticated DDoS detection framework to 5G network without worrying about the security issues and threats. Normally, the neural networks are widely used to detect complex and diversified DDoS attacks. However, feature vectors with high dimensions have a negative effect on detection performance. At present, there is little work on DDoS security dataset dimensionality reduction and verification. This paper proposes a DDoS detection method based on dimensionality reduction security dataset. First, XGBoost and mutual information algorithms are used to reduce the dimensionality of the KDDCup99 and CICDDoS2019 dataset respectively. Futhermore, we collect dataset in the experimental environment. Then, the CNN+LSTM and MLP neural network detectors are used to detect the dataset before and after the XGBoost dimensionality reduction. The experimental results show that using the XGBoost dimensionality reduction dataset, the neural network detector can detect multiclassify DDoS attack types with high accuracy and recall rate.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Mantas, G., Komninos, N., Rodriuez, J., Logota, E., Marques, H.: Security for 5G Communications. Fundamentals of 5G Mobile Networks (2015)
Cheskidov, P., Nikolskaia, K., Minbaleev, A.: Choosing the reinforcement learning method for modeling DdoS attacks. In: Proceedings of the International Multi -Conference on Industrial Engineering and Modern Technologies, pp. 1–4. IEEE (2019)
NSFOCUS. Vulnerability development trend (2020). http://blog.nsfocus.net
Komisarek, M., Pawlicki, M., Kozik, R., Choraś, M.: Machine learning based approach to anomaly and cyberattack detection in streamed network traffic data. J. Wirel. Mob. Netw. Ubiquit. Comput. Dependable Appl. 12(1), 3–19 (2021)
Zhe, T., Zhou, H., Li, K., Li, G.: DCTG: degree constrained topology generation algorithm for software-defined satellite network. J. Internet Serv. Inf. Secur. 9(4), 49–58 (2019)
Liu, H., Yu, L.: Toward integrating feature selection algorithms for classification and clustering. IEEE Trans. Knowl. Data Eng. 17(4), 491–502 (2005)
Cai, J., Luo, J., Wang, S., Yang, S.: Feature selection in machine learning: a new perspective. Neurocomputing 300, 70–79 (2018)
Lopez, A.D., Mohan, A.P., Nair, S.: Combining feature selectors for text classification. In: Proceedings of the 15th ACM International Conference on Information and Knowledge Management, pp. 798–799 (2006)
Firuz, K., Sherif, M., Rita, Z., Omar, M.: Feature selection for intrusion detection systems. In: Proceedings of the13th International Symposium on Computational Intelligence and Design, pp. 265–269 (2020)
Salo, F., Nassif, A.B., Essex, A.: Dimensionality reduction with IG-PCA and ensemble classifier for network intrusion detection. Comput. Netw. 148, 164–175 (2019)
Li, X., Yi, P., Wei, W., Jiang, Y., Tian, L.: LNNLS-KH: a feature selection method for network intrusion detection. Secur. Commun. Netw. 1–22, 2021 (2021)
Wang, C., Yao, H., Liu, Z.: An efficient DDoS detection based on SU-genetic feature selection. Clust. Comput. 22, 2505–2515 (2019). https://doi.org/10.1007/s10586-018-2275-z
Sanchez, O.R., Repetto, M., Carrega, A., Bolla, R., Pajo, J.F.: Feature selection evaluation towards a lightweight deep learning DDoS detector. In: IEEE International Conference on Communications, pp. 1–6 (2021)
Morris, B.: Explainable anomaly and intrusion detection intelligence for platform information technology using dimensionality reduction and ensemble learning. In: 2019 IEEE Autotestcon, pp. 1–5 (2019)
Vikram, M., Pavan, R., Dineshbhai, N.D., Mohan, B.: Performance evaluation of dimensionality reduction techniques on high dimensional data. In: Proceedings of the 3rd International Conference on Trends in Electronics and Informatics (ICOEI), pp. 1169–1174 (2019)
Amiri, F., Yousefi, M.R., Lucas, C., Shakery, A., Yazdani, N.: Mutual information-based feature selection for intrusion detection systems. J. Netw. Comput. Appl. 34(4), 1184–1199 (2011)
Yamanishi, K., Takeuchi, J., Williams, G.: On-line unsupervised outlier detection using finite mixtures with discounting learning algorithms. Data Min. Knowl. Disc. 8, 275–300 (2004). https://doi.org/10.1023/B:DAMI.0000023676.72185.7c
Sharafaldin, I., Lashkari, A.H., Hakak, S., Ghorbani, A.A.: Developing realistic distributed denial of service (DDoS) attack dataset and taxonomy. In: Proceedings of the International Carnahan Conference on Security Technology, pp. 1–8 (2019)
Chen, F., Ye, Z., Wang, C., Yan, L., Wang, R.: A feature selection approach for network intrusion detection based on tree-seed algorithm and k-nearest neighbor. In: Proceedings of the 4th International Symposium on Wireless Systems within the International Conferences on Intelligent Data Acquisition and Advanced Computing Systems, pp. 68–72 (2018)
Battiti, R.: Using mutual information for selecting features in supervised neural net learning. IEEE Trans. Neural Netw. 5(4), 537–550 (1994)
Chen, T., Guestrin, C.: Xgboost a scalable tree boosting system. In: Proceedings of the 22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, pp. 785–794. ACM (2016)
Jithu, P., Shareena, J., Ramdas, A., Haripriya, A.: Intrusion detection system for IoT botnet attacks using deep learning. SN Comput. Sci 2, 1–8 (2021). https://doi.org/10.1007/s42979-021-00516-9
Acknowledgments
This paper is supported by National Key R&D Program of China under Grant No. 2018YFA0701604.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Li, M., Qin, Y., Zhou, H. (2022). A DDoS Detection Method with Feature Set Dimension Reduction. In: You, I., Kim, H., Youn, TY., Palmieri, F., Kotenko, I. (eds) Mobile Internet Security. MobiSec 2021. Communications in Computer and Information Science, vol 1544. Springer, Singapore. https://doi.org/10.1007/978-981-16-9576-6_25
Download citation
DOI: https://doi.org/10.1007/978-981-16-9576-6_25
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-16-9575-9
Online ISBN: 978-981-16-9576-6
eBook Packages: Computer ScienceComputer Science (R0)