Abstract
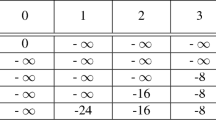
In this paper we analyse the security of the SHA-3 candidate ARIRANG. We show that bitwise complementation of whole registers turns out to be very useful for constructing high-probability differential characteristics in the function. We use this approach to find near-collisions with Hamming weight 32 for the full compression function as well as collisions for the compression function of ARIRANG reduced to 26 rounds, both with complexity close to 20 and memory requirements of only a few words. We use near collisions for the compression function to construct pseudo-collisions for the complete hash functions ARIRANG-224 and ARIRANG-384 with complexity 223 and close to 20, respectively. We implemented the attacks and provide examples of appropriate pairs of H,M values. We also provide possible configurations which may give collisions for step-reduced and full ARIRANG.
Chapter PDF
Similar content being viewed by others
References
Chang, D., Hong, S., Kang, C., Kang, J., Kim, J., Lee, C., Lee, J., Lee, J., Lee, S., Lee, Y., Lim, J., Sung, J.: ARIRANG: SHA-3 Proposal. NIST SHA-3 candidate, http://csrc.nist.gov/groups/ST/hash/sha-3/Round1/documents/ARIRANG.zip
Contini, S., Matusiewicz, K., Pieprzyk, J.: Extending FORK-256 attack to the full hash function. In: Qing, S., Imai, H., Wang, G. (eds.) ICICS 2007. LNCS, vol. 4861, pp. 296–305. Springer, Heidelberg (2007)
Hong, D., Kim, W.-H., Koo, B.: Preimage attack on arirang. Cryptology ePrint Archive, Report 2009/147 (2009), http://eprint.iacr.org/2009/147
Hong, D., Sung, J., Lee, S., Moon, D., Chee, S.: A new dedicated 256-bit hash function. In: Robshaw, M.J.B. (ed.) FSE 2006. LNCS, vol. 4047, pp. 195–209. Springer, Heidelberg (2006)
Indesteege, S., Mendel, F., Rechberger, C., Schläffer, M.: Practical Collisions for SHAMATA. In: Jacobson, M.J., Rijmen, V., Safavi-Naini, R. (eds.) SAC 2009. LNCS, vol. 5867, pp. 1–15. Springer, Heidelberg (2009)
Matusiewicz, K., Peyrin, T., Billet, O., Contini, S., Pieprzyk, J.: Cryptanalysis of FORK-256. In: Biryukov, A. (ed.) FSE 2007. LNCS, vol. 4593, pp. 19–38. Springer, Heidelberg (2007)
Mendel, F., Lano, J., Preneel, B.: Cryptanalysis of reduced variants of the FORK-256 hash function. In: Abe, M. (ed.) CT-RSA 2007. LNCS, vol. 4377, pp. 85–100. Springer, Heidelberg (2007)
Saarinen, M.-J.: A Meet-in-the-Middle collision attack against the new FORK-256. In: Srinathan, K., Rangan, C.P., Yung, M. (eds.) INDOCRYPT 2007. LNCS, vol. 4859, pp. 10–17. Springer, Heidelberg (2007)
Schneier, B., Kesley, J.: Unbalanced Feistel networks and block cipher design. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, pp. 121–144. Springer, Heidelberg (1996)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Guo, J., Matusiewicz, K., Knudsen, L.R., Ling, S., Wang, H. (2009). Practical Pseudo-collisions for Hash Functions ARIRANG-224/384. In: Jacobson, M.J., Rijmen, V., Safavi-Naini, R. (eds) Selected Areas in Cryptography. SAC 2009. Lecture Notes in Computer Science, vol 5867. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-05445-7_9
Download citation
DOI: https://doi.org/10.1007/978-3-642-05445-7_9
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-05443-3
Online ISBN: 978-3-642-05445-7
eBook Packages: Computer ScienceComputer Science (R0)