Abstract
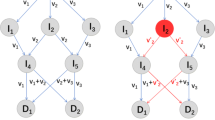
Network coding offers increased throughput and improved robustness to random faults in completely decentralized networks. In contrast to traditional routing schemes, however, network coding requires intermediate nodes to modify data packets en route; for this reason, standard signature schemes are inapplicable and it is a challenge to provide resilience to tampering by malicious nodes.
We propose two signature schemes that can be used in conjunction with network coding to prevent malicious modification of data. Our schemes can be viewed as signing linear subspaces in the sense that a signature σ on a subspace V authenticates exactly those vectors in V. Our first scheme is (suitably) homomorphic and has constant public-key size and per-packet overhead. Our second scheme does not rely on random oracles and is based on weaker assumptions.
We also prove a lower bound on the length of signatures for linear subspaces showing that our schemes are essentially optimal in this regard.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-3-642-00468-1_29
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Ahlswede, R., Cai, N., Li, S., Yeung, R.: Network information flow. IEEE Transactions on Information Theory 46(4), 1204–1216 (2000)
Bellare, M., Goldreich, O., Goldwasser, S.: Incremental cryptography: The case of hashing and signing. In: Desmedt, Y.G. (ed.) CRYPTO 1994. LNCS, vol. 839, pp. 216–233. Springer, Heidelberg (1994)
Boneh, D., Franklin, M.: An efficient public key traitor tracing scheme. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 338–353. Springer, Heidelberg (1999)
Boneh, D., Gentry, C., Lynn, B., Shacham, H.: Aggregate and verifiably encrypted signatures from bilinear maps. In: Biham, E. (ed.) EUROCRYPT 2003. LNCS, vol. 2656, pp. 416–432. Springer, Heidelberg (2003)
Brands, S.: An efficient off-line electronic cash system based on the representation problem, CWI Technical Report CS-R9323 (1993)
Byers, J.W., Luby, M., Mitzenmacher, M., Rege, A.: A digital fountain approach to reliable distribution of bulk data. In: ACM SIGCOMM (1998)
Charles, D., Jain, K., Lauter, K.: Signatures for network coding. In: 40th Annual Conference on Information Sciences and Systems, CISS 2006 (2006)
Chou, P.A., Wu, Y., Jain, K.: Practical network coding. In: 41st Allerton Conference on Communication, Control, and Computing (2003)
Duquesne, S., Frey, G.: Background on pairings. In: Handbook of Elliptic and Hyperelliptic Curve Cryptography. Chapman & Hall/CRC Press, Boca Raton (2006)
Freeman, D., Scott, M., Teske, E.: A taxonomy of pairing-friendly elliptic curves. Cryptology ePrint Archive, Report 2006/372 (2006), http://eprint.iacr.org/
Gkantsidis, C., Rodriguez, P.: Network coding for large scale content distribution. In: IEEE INFOCOM (2005)
Gkantsidis, C., Rodriguez, P.: Cooperative security for network coding file distribution. In: IEEE INFOCOM (2006)
Han, K., Ho, T., Koetter, R., Médard, M., Zhao, F.: On network coding for security. In: IEEE MILCOM (2007)
Ho, T., Koetter, R., Médard, M., Karger, D., Effros, M.: The benefits of coding over routing in a randomized setting. In: Proc. International Symposium on Information Theory (ISIT) (2003)
Ho, T., Leong, B., Koetter, R., Médard, M., Effros, M., Karger, D.: Byzantine modification detection in multicast networks using randomized network coding. In: Proc. Intl. Symposium on Information Theory (ISIT), pp. 144–152 (2004)
Ho, T., Médard, M., Koetter, R., Karger, D.R., Effros, M., Shi, J., Leong, B.: A random linear network coding approach to multicast. IEEE Trans. Inform. Theory 52(10), 4413–4430 (2006)
Jaggi, S.: Design and Analysis of Network Codes. PhD thesis, California Institute of Technology (2006)
Jaggi, S., Langberg, M., Katti, S., Ho, T., Katabi, D., Médard, M., Effros, M.: Resilient network coding in the presence of Byzantine adversaries. IEEE Trans. on Information Theory 54(6), 2596–2603 (2008)
Johnson, R., Molnar, D., Song, D., Wagner, D.: Homomorphic signature schemes. In: Preneel, B. (ed.) CT-RSA 2002. LNCS, vol. 2271, pp. 244–262. Springer, Heidelberg (2002)
Katz, J., Lindell, Y.: Introduction to Modern Cryptography. Chapman & Hall/CRC Press, Boca Raton (2007)
Kim, M., Médard, M., Barros, J.: Counteracting Byzantine adversaries with network coding: An overhead analysis (2008), http://arxiv.org/abs/0806.4451
Krohn, M., Freedman, M., Mazieres, D.: On the-fly verification of rateless erasure codes for efficient content distribution. In: Proc. of IEEE Symposium on Security and Privacy, pp. 226–240 (2004)
Li, S.-Y.R., Yeung, R.W., Cai, N.: Linear network coding. IEEE Trans. Info. Theory 49(2), 371–381 (2003)
Stanley, R.: Enumerative Combinatorics, vol. 1. Cambridge University Press, Cambridge (1997)
Zhao, F., Kalker, T., Médard, M., Han, K.: Signatures for content distribution with network coding. In: Proc. Intl. Symp. Info. Theory (ISIT) (2007)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Boneh, D., Freeman, D., Katz, J., Waters, B. (2009). Signing a Linear Subspace: Signature Schemes for Network Coding. In: Jarecki, S., Tsudik, G. (eds) Public Key Cryptography – PKC 2009. PKC 2009. Lecture Notes in Computer Science, vol 5443. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-00468-1_5
Download citation
DOI: https://doi.org/10.1007/978-3-642-00468-1_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-00467-4
Online ISBN: 978-3-642-00468-1
eBook Packages: Computer ScienceComputer Science (R0)