Abstract
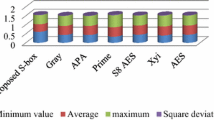
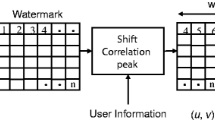
In this paper, we propose five simple algorithms to execute a collusion attack given several watermarked documents. Each document considered is a picture represented as a matrix of two dimensional Discrete Cosine Transform (DCT2) coefficients. Our algorithm is independent of media type. Bootstrap methods are used to construct confidence intervals for each DCT2 coefficient and determine its uncertainty. Using simulation studies we show that Bootstrap procedures are highly efficient with respect to the number of iterations and sample size per iteration while maintaining stellar probabilistic coverage, providing results at least as good as averaging or taking the median of signals. Most importantly, a set of simulation studies suggest that the precision of our heuristic methodology increases quickly when the number of watermarked copies are increased, but good probabilistic coverage is achieved with a low number of independently watermarked copies. We conjecture that the Bootstrap methodology will be highly effective in reconstructing the original signal for documents with high redundancy.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Cannons, J., Moulin, P.: Design and Statistical Analysis of a Hash-Aided Image Watermarking System. IEEE Transactions on Image Processing 13(10), 1393–1408 (2004)
Comesaña, P., Pérez-Freire, L., Pérez-González, F.: The Return of the Sensitivity Attack. In: Barni, M., Cox, I., Kalker, T., Kim, H.-J. (eds.) IWDW 2005. LNCS, vol. 3710, pp. 260–274. Springer, Heidelberg (2005)
Cox, I.J., Kilian, J., Leighton, F.T., Shamoon, T.: Secure spread spectrum watermarking for multimedia. IEEE Transactions on Image Processing 6(12), 1673–1687 (1997)
Delaigle, J.F., De Vleeschouwer, C., Macq, B.: Watermarking algorithm based on a human visual model. Signal Processing 66, 319–335 (1998)
Dong, P., Brankov, J.G., Galatsanos, N.P., Yang, Y., Davoine, F.: Digital Watermarks Robust to Geometric Distortions. IEEE Transactions on Image Processing 14(12), 2140–2150 (2005)
Doërr, G., Dugelay, J.: Countermeasures for Collusion Attacks Exploiting Host Signal Redundancy. In: Barni, M., Cox, I., Kalker, T., Kim, H.-J. (eds.) IWDW 2005. LNCS, vol. 3710, pp. 216–230. Springer, Heidelberg (2005)
Doërr, G., Dugelay, J.: Security Pitfalls of Frame-by-Frame Approaches to Video Watermarking. IEEE Transactions on Signals Processing 52(10), 2955–2964 (2004)
Efron, B.: The Jackknife, the Bootstrap and other Resampling Plans. Society for Industrial and Applied Mathematics, Philadelphia (1982)
Efron, B., Tibshirani, R.J.: An Introduction to the Bootstrap. Chapman & Hall, New York (1993)
Ergun, F., Kilian, J., Kumar, R.: A Note on the Limits of Collusion-Resistant Watermarks. In: Stern, J. (ed.) EUROCRYPT 1999. LNCS, vol. 1592, pp. 140–149. Springer, Heidelberg (1999)
Furon, T.: A Survey of Watermarking Security. In: Barni, M., Cox, I., Kalker, T., Kim, H.-J. (eds.) IWDW 2005. LNCS, vol. 3710, pp. 201–215. Springer, Heidelberg (2005)
Khayam, S.A.: The Discrete Cosine Transform (DCT): Theory and Application. Michigan State University (2003)
Kiyavash, N., Moulin, P.: A Framework for Optimizing Nonlinear Collusion Attacks on Fingerprinting Systems. In: 40th Annual Conference on Information Sciences and Systems, pp. 1170–1175 (2006)
Kiyavash, N., Moulin, P.: On Optimal Collusion Strategies for Fingerprinting. In: Proceedings of IEEE International Conference on Acoustics, Speech, and Signal Processing, vol. 5, p. V (2006)
Podilchuk, C.I., Delp, E.J.: Digital Watermarking: Algorithms and Applications. Signal Processing Magazine 18(4), 33–46 (2001)
Shao, J., Tu, D.: The Jackknife and Bootstrap. Springer, New York (2005)
Soriano, M., Fernandez, M., Cotrina, J.: Fingerprinting Schemes: Identifying the Guilty Sources Using Side Information. In: Barni, M., Cox, I., Kalker, T., Kim, H.-J. (eds.) IWDW 2005. LNCS, vol. 3710, pp. 231–243. Springer, Heidelberg (2005)
Vila-Forcén, J.E., Voloshynovskiy, S., Koval, O., Pérez-González, F., Pun, T.: Practical Data-Hiding: Additive Attacks Performance Analysis. In: Barni, M., Cox, I., Kalker, T., Kim, H.-J. (eds.) IWDW 2005. LNCS, vol. 3710, pp. 244–259. Springer, Heidelberg (2005)
Vinod, P., Bora, P.K.: A New Inter-Frame Collusion Attack and a Countermeasure. In: Barni, M., Cox, I., Kalker, T., Kim, H.-J. (eds.) IWDW 2005. LNCS, vol. 3710, pp. 147–157. Springer, Heidelberg (2005)
Wang, Z., Wu, M., Zhao, H., Liu, K.: Resistance of Orthogonal Gaussian Fingerprints to Collusion Attacks. In: Proceedings of International Conference on Multimedia and Expo., vol. 1, pp. 617–620 (2003)
Wolfgang, R.B., Podilchuk, C.I., Delp, E.J.: Perceptual Watermarks for Digital Images and Video. Proceedings of IEEE 87(7), 1108–1126 (1999)
Wu, M., Trappe, W., Wang, Z., Liu, K.: Collusion-resistant Fingerprinting for Multimedia. IEEE Signal Processing Magazine 21(2), 15–27 (2004)
Zhao, H., Wu, M., Wang, Z., Liu, K.: Forensic Analysis of Nonlinear Collusion Attacks for Multimedia Fingerprinting. IEEE Transactions on Image Processing 14(5), 646–661 (2005)
Zhao, H., Wu, M., Wang, Z., Liu, K.: Nonlinear Collusion Attacks on Independent Fingerprints for Multimedia. In: Proceedings of IEEE International Conference on Acoustics, Speech, and Signal Processing, vol. 5, pp. 664–667 (2003)
Zhu, W., Xiong, Z., Zhang, Y.: Multiresolution Watermarking for Images and Video. IEEE Transactions on Circuits and Systems for Video Technology 9(4), 545–550 (1999)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Behseta, S., Lam, C., Webb, R.L. (2008). A Bootstrap Attack on Digital Watermarks in the Frequency Domain. In: Chen, L., Ryan, M.D., Wang, G. (eds) Information and Communications Security. ICICS 2008. Lecture Notes in Computer Science, vol 5308. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-88625-9_24
Download citation
DOI: https://doi.org/10.1007/978-3-540-88625-9_24
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-88624-2
Online ISBN: 978-3-540-88625-9
eBook Packages: Computer ScienceComputer Science (R0)