Abstract
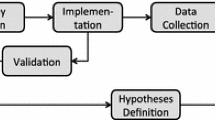
In order to improve the quality of embedded software by finding obstacles unanticipated by software specifications, this paper describes a requirement analysis method based on an Information Flow Diagram and experiments using this method, with discussion. Recently, embedded software has become more large-scale and complicated while the development cycle of the software has typically been shortened. This industry trend compromises the quality of embedded software. In order to improve the quality of the software, unexpected obstacles must be carefully analyzed in the specification and design phases. We propose a diagram-based analysis method to answer this need, and have performed an experiment using the analysis method with an actual product. The results of the experiment made it clear that 1) Novice engineers can construct an Information Flow Diagram under the lead of expert engineers; and 2) The methods by which experts lead novice engineers in the analysis of unexpected obstacles require further refinement.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Mise, T., Shinyashiki, Y., Hashimoto, M., Ubayashi, N., Nakatani, T.: A Specification Analysis Method for Unexpected Obstacles in Embedded Software (in Japanese). In: Proc. of the FOSE2005, Kindai Kagaku Sha. Japan Society for Software Science and Technology, pp. 227–235 (2005)
Sumi, T., Hirayama, M., Ubayashi, N.: Analysis of the external environment for embedded systems, IPSJ SIG Technical Reports, 2004-SE-146, pp. 33–40 (in Japanese) (2004)
Ministry of Economy, Trade and Industry, editor. Report of actual field survey of embedded software, Edition, Ministry of Economy, Trade and Industry (in Japanese) (2005)
Crook, R., Lnce, D., Lin, L., Nuseibeh, B.: Security Requirements Engineering: When Anti-Requirements Hit the Fan. In: Proc. of the 10th Anniversary Joint IEEE International Requirements Engineering Conference (RE 2002), pp. 203–205 (2002)
Hatanaka, H., Shinyashiki, Y., Mise, T., Kametani, H., Hashimoto, M., Ubayashi, N., Katamine, K., Nakatani, T.: An Analysis of Information Flow Graph based on Conceptual Model of Exceptions in Embedded Software, Technical Report of IEICE 104-431, pp. 19–24 (2004)
Shinyashiki, Y., Mise, T., Eura, Y., Hatanaka, H., Hashimoto, M., Ubayashi, N., Katamine, K., Nakatani, T.: A Conceptual Model of Exceptions in Embedded Software. In: Proceedings of Embedded Software Symposium, pp. 8–11 (in Japanese) (2004)
Mise, T., Shinyashiki, Y., Eura, Y., Hatanaka, H., Hashimoto, M., Ubayashi, N., Katamine, K., Nakatani, T.: Exception Analysis Matrix for Embedded System Software Specification. In: Proc. IPSJ/SIGSE Embedded Software Symposium (ESS 2004) (in Japanese) (2004)
Mise, T., Shinyashiki, Y., Hashimoto, M., Ubayashi, N., Katamine, K., Nakatani, T.: An Analysis Method with Failure Scenario Matrix for Specifying Unexpected Obstacles in Embedded System. In: The proceeding of the 12TH Asia-Pacific Software Engineering Conference, pp. 447–454 (2005)
Kametani, H., Shinyashiki, Y., Mise, T., Hashimoto, M., Ubayashi, N., Katamine, K., Nakatani, T.: Information Flow Diagram and Analysis Method for Unexpected Obstacle Specification of Embedded Software. In: Proc. of the Knowledge-Based Software Engineering (JCKBSE 2006), pp. 115–124 (2006)
Leveson, N.G.: Fault Tree Analysis. Safeware System Safety and Computers, 317–326 (1995)
Leveson, N.G.: Failure Modes and Effects Analysis. Safeware System Safety and Computers, 341–344 (1995)
Leveson, N.G.: HaZards and Operability Analysis. Safeware System Safety and Computers, 335–341 (1995)
Pentti, H., Atte, H.: Failure Mode and Effects Analysis of Software-based Automation Systems, STUK-YTO-TR 190, p. 35 (2002)
Dehlinger, J., Lutz, R. R. (eds.): Software Fault Tree Analysis for Product Lines. In: Proceedings of the Eighth IEEE International Symposium on High Assurance Systems Engineering, pp. 12–21 (2004)
Redmill, F., Chudleigh, M., Catmur, J.: System Safety: Hazop and Software Hazop, p. 248. John Wiley & Sons Ltd, New York (1999)
Alexander, I.: Misuse cases, use cases with hositile intent. IEEE Software 20(1), 55–66 (2003)
Lamsweerde, A.V., Letier, E.: Handling Obstacles in Goal-Oriented Requirements Engineering. IEEE Transactions on Software Engineering 26(10), 978–1005 (2000)
Bemus, P., Mertins, K., Schmidt, G. (eds.): Handbook on Architecture of Information Systems. Springer, Heidelberg (1998)
Mise, T., Hashimoto, M., Katamine, K., Shinyashiki, Y., Ubayashi, N., Nakatani, T.: A Method for Extracting Unexpected Scenarios of Embedded Systems. In: Proc. of the Knowledge-Based Software Engineering (JCKBSE 2006), pp. 41–50 (2006)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Shinyashiki, Y., Mise, T., Hashimoto, M., Katamine, K., Ubayashi, N., Nakatani, T. (2007). A Suggestion for Analysis of Unexpected Obstacles in Embedded System. In: Smith, M.J., Salvendy, G. (eds) Human Interface and the Management of Information. Methods, Techniques and Tools in Information Design. Human Interface 2007. Lecture Notes in Computer Science, vol 4557. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-73345-4_86
Download citation
DOI: https://doi.org/10.1007/978-3-540-73345-4_86
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-73344-7
Online ISBN: 978-3-540-73345-4
eBook Packages: Computer ScienceComputer Science (R0)