Abstract
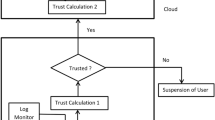
Cloud computing is a revolutionary information technology, that aims to provide reliable, customized and quality of service guaranteed environments, where virtualized and dynamic data are stored and shared among cloud users. Thanks to its significant benefits such as: on demand resources and low maintenance costs, cloud computing becomes a trend in the area of new technologies that facilitates communication and access to information. Despite the aforementioned facts, the distributed and open nature of this paradigm makes privacy and security of the stored resources a major challenge, that limits the use and agreement of cloud computing in practice. Among the strong security policies adopted to address this problem, there are Intrusion Detection and Prevention Systems (IDPS), that enable the cloud architecture to detect anomalies through monitoring the usage of stored resources, and then reacting prevent their expansion. In this paper, we propose a secure, reliable and flexible IDPS mainly based on autonomous mobile agents, that are associated with tracing and revocation protocol. While roaming among multiple cloud servers, our mobile agent is charged with executing requested tasks and collecting needed information. Thus, on each cloud server a “cryptographic trace” is produced in which all behaviors, results and data involved in the execution are recorded, which allow to identify any possible intrusions and hence predict a response to prevent them or end their processing, through using a server revocation technique based on trust threshold.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Mell, P., Grance, T.: The NIST definition of cloud computing (2011)
Galante, J., Kharif, O., Alpeyev, P.: Sony network breach shows Amazon clouds appeal for hackers (2011)
Scarfone, K., Mell, P.: Guide to Intrusion Detection and Prevention Systems (IDPS). NIST Special Publication, 800, p. 94 (2007)
Gavalas, D., Tsekouras, G.E., Anagnostopoulos, C.: A mobile agent platform for distributed network and systems management. J. Syst. Softw. 82(2), 355–371 (2009)
Gupta, S., Kumar, P., Abraham, A.: A profile based network intrusion detection and prevention system for securing cloud environment. Int. J. Distrib. Sens. Netw. 2013, 1–12 (2013)
Tupakula, U., Varadharajan, V., Akku, N.: Intrusion detection techniques for infrastructure as a service cloud. In: IEEE International Conference on Dependable, Autonomic and Secure Computing, pp. 744–751 (2011)
Jin, H., Xiang, G., Zou, D., Wu, S., Zhao, F., Li, M., Zheng, W.: A VMM-based intrusion prevention system in cloud computing environment. J. Supercomput. 66(3), 1133–1151 (2013)
Smith, D., Guan, Q., Fu, S.: An anomaly detection framework for autonomic management of compute cloud systems. In: 34th Annual Computer Software and Applications Conference Workshops (COMPSACW), Seoul, pp. 376–381 (2010)
Alsafi, H.M., Abduallah, W.M., Pathan, A.S.K.: IDPS: an integrated intrusion handling model for cloud computing environment. Int. J. Comput. Inf. Technol. (IJCIT) 4(1), 1–16 (2012)
Dastjerdi, A.V., Bakar, K.A., Tabatabaei, S.G.H.: Distributed intrusion detection in clouds using mobile agents. In: Third International Conference on Advanced Engineering Computing and Applications in Sciences, Sliema, pp. 175–180 (2010)
Mills, D., Martin, J., Burbank, J., Kasch, W.: Network time protocol version 4: protocol and algorithms specification no. RFC5905 (2010)
Vigna, G.: Cryptographic traces for mobile agents. In: Vigna, G. (ed.) Mobile Agents and Security. LNCS, vol. 1419, pp. 137–153. Springer, Heidelberg (1998). doi:10.1007/3-540-68671-1_8
Phan, R.W.: Fixing the integrated Diffie-Hellman-Dsa key exchange protocol. Commun. Lett. IEEE 9(6), 570–572 (2005)
Aumasson, J.: On the pseudo-random generator ISAAC. IACR Cryptology ePrint Archive 2006, p. 438 (2006)
Jaffar, A., Martinez, J.C.: Detail power analysis of the SHA-3Hashing algorithm candidates on Xilinx Spartan-3E. Int. J. Comput. Electr. Eng. 5(4), 410–413 (2013)
Announcing the Advanced Encryption Standard (AES). FIPS Publication 197, NIST (2001)
Gallagher, P.: Digital signature standard (DSS). Federal Information Processing Standards Publication, FIPS PUB, 186–3 (2009)
Calheiros, R.N., Ranjan, R., Beloglazov, A., DeRose, C.A.F., Buyya, R.: CloudSim: a toolkit for modeling and simulation of cloud computing environments and evaluation of resource provisioning algorithms. Softw. Pract. Experience 41(1), 23–50 (2010). Wiley publishers
Bellifemine, F., Poggi, A., Rimassa, G.: JADE: a FIPA2000-compliant agent development environment. In: The 5th International Conference on Autonomous Agents, pp. 216–217. ACM, Montreal (2001)
Braun, P., Rossak, R.: Mobile Agents: Basic Concepts, Mobility Models and the Tracy Toolkit. Elsevier, San Francisco (2005)
Maynor, D.: Metasploit Toolkit for Penetration Testing, Exploit Development, and Vulnerability Research. Elsevier, San Francisco (2011)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2017 Springer International Publishing AG
About this paper
Cite this paper
Idrissi, H., Ennahbaoui, M., El Hajji, S., Souidi, E.M. (2017). A Secure Cloud-Based IDPS Using Cryptographic Traces and Revocation Protocol. In: El Hajji, S., Nitaj, A., Souidi, E. (eds) Codes, Cryptology and Information Security. C2SI 2017. Lecture Notes in Computer Science(), vol 10194. Springer, Cham. https://doi.org/10.1007/978-3-319-55589-8_24
Download citation
DOI: https://doi.org/10.1007/978-3-319-55589-8_24
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-55588-1
Online ISBN: 978-3-319-55589-8
eBook Packages: Computer ScienceComputer Science (R0)