Abstract
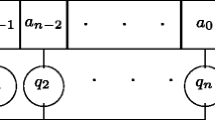
Pseudorandom sequences are used in a wide range of applications in computing and communications, including cryptography. It is common to use linear feedback shift registers (LFSRs) to generate such sequences, either directly or as components in more complex structures. Much of the analysis of such sequences is done using the algebra of polynomials and power series over finite fields. The subjects of this chapter are feedback with carry shift registers (FCSRs) and algebraic feedback shift registers (AFSRs, generalizations of both LFSRs and FCSRs), sequence generators that are analogous to LFSRs, but whose state update involves arithmetic with a carry. Their analysis is based on algebraic structures with carry, such as the integers and the N-adic numbers. After a brief review of the basics on LFSRs, FCSRs, and AFSRs, we describe several open problems. These include: given part of a sequence, how to find an optimal generator of the sequence; how to construct sequences that cannot be generated by short LFSRs, FCSRs, or AFSRs; and the analysis of various statistical properties related to these generators.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
F. Arnault, T. Berger, A. Necer, Feedback with carry shift registers synthesis with the Euclidean algorithm. IEEE Trans. Inf. Theory 50, 910–917 (2004) This paper modifies the extended Euclidean algorithm to find a minimal FCSR generating a sequence given a sufficiently long prefix of the sequence.
J. Bourgain, T. Cochrane, J. Paulhus, C. Pinner, Decimations of ℓ-sequences and permutations of even residues mod p. SIAM J. Discrete Math. 23, 842–857 (2009)
J. Bourgain, T. Cochrane, J. Paulhus, C. Pinner, On the parity of k-th powers mod p, a generalization of a problem of Lehmer. Acta Arith. 147, 173–203 (2011) These two papers show that if p is large enough and 2 is primitive modulo p, then all decimations of an ℓ-sequence with connection integer p are cyclically distinct. It is conjectured that this is true for all primes p > 13.
R. Carmichael, Sequences of integers defined by recurrence relations, Q. J. Pure Appl. Math. 48, 343–372 (1920) This is one of the first papers to study integer linear recurrences modulo an integer.
N. Courtois, Fast algebraic attacks on stream ciphers with linear feedback, in Advances in Cryptology: Crypto 2003, ed. by D. Boneh, Lecture Notes in Computer Science, vol 2729 (Springer, Berlin, 2003), pp. 177–194 Courtois’ seminal paper describes an attack on stream ciphers based on finding low degree multiples of the polynomials that express the output from a keystream generator in terms of the state bits. If such multiples can be found, then the problem of recovering the state from the output can be solved by solving a system of linear equations in the monomials of low degree.
R. Couture, P. L’Écuyer, Distribution properties of multiply-with-carry random number generators. Math. Comput. 66, 591–607 (1997) Couture and L’Écuyer invented multiply with carry sequences, generated by linear recurrences with carry. These are equivalent to FCSR sequences, which were invented independently at about the same time by Goresky and Klapper.
Z. Dai, S. Jiang, K. Imamura, G. Gong, Asymptotic behavior of normalized linear complexity of ultimately non-periodic sequences. IEEE Trans. Inf. Theory 50, 2911–2915 (2004) Let a be an infinite, binary, eventually aperiodic sequence. The authors show that the set of accumulation points of the normalized linear complexities of prefixes of a is an interval of the form [B, 1 − B].
M. Goresky, A. Klapper, Arithmetic cross-correlations of FCSR sequences. IEEE Trans. Inf. Theory 43, 1342–1346 (1997) It is shown that the arithmetic cross-correlations of cyclically distinct binary ℓ-sequences are identically zero.
M. Goresky, A. Klapper, Periodicity, correlation, and distribution properties of d–FCSR sequences. Des. Codes Cryptogr. 33, 123–148 (2004) d-FCSRs are a variant of FCSRs base on the algebra of \(\mathbb{Z}[2^{1/d}]\). In this paper various statistical properties of maximum period d-FCSR sequences are considered.
M. Goresky, A. Klapper, Algebraic Shift Register Sequences (Cambridge University Press, Cambridge, 2012), http://www.cs.uky.edu/~klapper/algebraic.html This is an extensive monograph on sequence generators based on abstract algebra. Topics studied include statistical analysis, maximum period sequences, and the register synthesis problem: the problem of finding a minimal generator of a particular type for a sequence given a short prefix.
M. Goresky, A. Klapper, R. Murty, On the distinctness of decimations of ℓ-sequences, in Sequences and Their Applications—SETA ’01, eds. by T. Helleseth, P.V. Kumar, K. Yang (Springer, Berlin, 2002), pp. 197–208
M. Goresky, A. Klapper. R. Murty, I. Shparlinski, On decimations of ℓ-sequences. SIAM J. Discrete Math. 18, 130–140 (2004) These two papers give a partial solution to the conjecture that all decimations of an ℓ-sequence are distinct if the connection integer is greater than 13. Exponential sum techniques are used.
D. Heath-Brown, Artin’s conjecture for primitive roots. Q. J. Math. Oxford Ser. 37(1), 27–38 (1986)
C. Hooley, On Artin’s conjecture. J. Reine Angew. Math. 22, 209–220, (1967) These two papers give a partial solution to Artin’s conjecture (that for any integer N there are infinitely many primes for which N is primitive), assuming a generalized Riemann hypothesis.
E. Key, An Analysis of the structure and complexity of nonlinear binary sequence generators. IEEE Trans. Inf. Theory 22(1), 732–736 (1976) Key analyzed the linear complexities of sequences generated by nonlinear combiners and LFSRs with nonlinear output functions.
A. Klapper, Distributional properties of d–FCSR sequences. J. Complexity 20, 305–317 (2004) Let a be a maximum period sequence generated by a length m p-ary d-FCSR (an AFSR based on a ring \(\mathbb{Z}[p^{1/d}]\)). We study the variation in the number of occurrences of blocks of length s ≤ m. If d = 2, we see that the variation is bounded by a constant times the square root of the average number of occurrences of blocks of length s.
A. Klapper, The asymptotic behavior of 2-adic complexity. Adv. Math. Commun. 1, 307–319 (2007) Let a be an infinite, binary, eventually aperiodic sequence. We show that the set of accumulation points of the normalized 2-adic complexities of prefixes of a is an interval of the form [B, 1 − B].
A. Klapper, The asymptotic behavior of π-adic complexity with \(\pi ^{2} = -2\), in Sequences, Subsequences, and Consequences, eds. by S. Golomb, G. Gong, T. Helleseth, H.-Y. Song, Lecture Notes in Computer Science, vol 4893 (Springer, Berlin, 2007), pp. 134–147 Let a be an infinite, binary, eventually aperiodic sequence. We show that the set of accumulation points of the normalized π-adic complexities of prefixes of a is an interval of the form [B, 1 − B] in some cases.
A. Klapper, Expected π-adic complexity of sequences. IEEE Trans. Inf. Theory 56, 2486–2501 (2010) This paper computes the average π-adic complexity of sequences of fixed period.
A. Klapper, M. Goresky, Feedback shift registers, 2-adic span, and combiners with memory. J. Cryptol. 10, 111–147 (1997) In this paper FCSRs were introduced and many basic properties were worked out. Parts of this analysis were based on the algebra of 2-adic numbers.
J. Xu, A. Klapper, Feedback with carry shift registers over \(\mathbb{Z}/(n)\), in Proceedings of International Conference on Sequences and their Application (SETA), Singapore, December 1998, eds. by C. Ding, T. Helleseth, H. Niederreiter (Springer, Berlin, 1999), pp. 379–392 This paper generalizes Xu and Klapper’s algorithm [28] to AFSRs over certain number fields (including d-FCSRs).
J.L. Massey, Shift register synthesis and BCH decoding. IEEE Trans. Inf. Theory 15(1), 122–127 (1969) Jim Massey showed here how Berlekamp’s decoding algorithm could be used as an efficient solution to the LFSR synthesis problem. The idea is to process one symbol at a time. When the rational approximation needs updating (i.e., a discrepancy occurs), a new approximation that is correct for the new symbol is found as a linear combination of two earlier approximation.
W. Meier, O. Staffelbach, Correlation properties of combiners with memory in stream ciphers. J. Cryptol. 5, 67–86 (1992) This paper describes an effective attack on stream ciphers that combine several m-sequences with a nonlinear combiner, endowed with a small amount of extra memory. The basis is the analysis of the combining function to find a correlation between state bits and output bits.
H. Niederreiter, The probabilistic theory of linear complexity, in Advances in Cryptology—Eurocrypt 88, ed. by C. Günther, Lecture Notes in Computer Science, vol 330 (Springer, Berlin, 1988), pp. 191–209 Niederreiter showed that with probability 1 the limit of the normalized linear complexity of a sequence exists and equals 1∕2. The proof of this fact uses a relationship between continued fractions and linear complexity and uses the theory of dynamical systems.
NIST, Statistical test suite for random and pseudorandom number generators for cryptographic applications, http://csrc.nist.gov/groups/ST/toolkit/rng/index.html This is a resource with useful tools for measuring statistical randomness of sequences.
R. Rueppel, Analysis and Design of Stream Ciphers (Springer, Berlin, 1986) This book studies several aspects of stream ciphers and statistical properties of sequences, including nonlinear combiners with memory such as the summation combiner. It was largely based on Ruepppel’s Ph.D. dissertation.
L.R. Welch, Lower bounds on the maximum correlation of signals. IEEE Trans. Inf. Theory 20(1), 397–399 (1974) Here Welch derived a fundamental constraint on the size of sequence families with low pairwise correlations.
A. Klapper, J. Xu, Register synthesis for algebraic feedback shift registers based on non-primes. Des. Codes Cryptogr. 31, 227–250 (2004) This paper presents a solution to the FCSR synthesis problem for n-ary FCSRs with n arbitrary. This algorithm modifies the Berlekamp–Massey algorithm—when a discrepancy is found, the rational approximation is amended to account for several new sequence symbols instead of just one.
Acknowledgements
This material is based upon work supported by the National Science Foundation under Grant No. CCF-0514660. Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author and do not necessarily reflect the views of the National Science Foundation.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this chapter
Cite this chapter
Klapper, A. (2014). Open Problems on With-Carry Sequence Generators. In: Koç, Ç. (eds) Open Problems in Mathematics and Computational Science. Springer, Cham. https://doi.org/10.1007/978-3-319-10683-0_9
Download citation
DOI: https://doi.org/10.1007/978-3-319-10683-0_9
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-10682-3
Online ISBN: 978-3-319-10683-0
eBook Packages: Computer ScienceComputer Science (R0)