Abstract
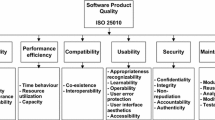
Earlier software architecture design is essential particularly when it comes to security concerns, since security risks, requirements and architectures are all closely interrelated and interacting. We have proposed the security driven twin peaks method with a mutual refinement of the requirements, and architectures. However, there are multiple alternatives to an architecture design for initial requirements, and their choices depend on non-functional requirements (NFRs), such as security, performance, and costs which have a big impact on the quality of the software. We propose a new method called TPM-SA2 to avoid any back-track in refinement. Each architectural alternative in TPM-SA2 is refined so that it aligns with the requirements. For each refinement, the requirements can be updated vice versa. TPM-SA2 enables us to predict the impacts on the NFRs by each candidate for the architecture, and choose the most appropriate one with respect to the impact. As a result, we can define the requirements and architectures, and estimated the development costs earlier than ever.
Chapter PDF
Similar content being viewed by others
Keywords
- Analytic Hierarchy Process
- Functional Requirement
- Security Requirement
- Security Analysis
- Architectural Design
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Bass, L., Clements, P., Kazman, R.: Software Architecture in Practice, 2nd edn. Addison-Wesley (2003)
Fernandez, E.B.: Security patterns and secure systems design. In: Bondavalli, A., Brasileiro, F., Rajsbaum, S. (eds.) LADC 2007. LNCS, vol. 4746, pp. 233–234. Springer, Heidelberg (2007)
Ferraz, F.S., Assad, R.E., de Lemos Meira, S.R.: Relating security requirements and design patterns: Reducing security requirements implementation impacts with design patterns. In: ICSEA, pp. 9–14 (2009)
Guo, Z., Zeckzer, D., Liggesmeyer, P., Mackel, O.: Identification of security-safety requirements for the outdoor robot ravon using safety analysis techniques. In: International Conference on Software Engineering Advances, pp. 508–513 (2010)
Heyman, T., Yskout, K., Scandariato, R., Schmidt, H., Yu, Y.: The security twin peaks. In: Erlingsson, Ú., Wieringa, R., Zannone, N. (eds.) ESSoS 2011. LNCS, vol. 6542, pp. 167–180. Springer, Heidelberg (2011)
Houmb, S.H., Islam, S., Knauss, E., Jürjens, J., Schneider, K.: Eliciting security requirements and tracing them to design: An integration of common criteria, heuristics, and umlsec. Requir. Eng. 15(1), 63–93 (2010)
Kazman, R., Klein, M.H., Barbacci, M., Longstaff, T.A., Lipson, H.F., Carrière, S.J.: The architecture tradeoff analysis method. In: ICECCS, pp. 68–78 (1998)
van Lamsweerde, A.: Elaborating security requirements by construction of intentional anti-models. In: ICSE, pp. 148–157 (2004)
Liu, L., Yu, E.S.K., Mylopoulos, J.: Secure-i*: Engineering secure software systems through social analysis. Int. J. Software and Informatics 3(1), 89–120 (2009)
Mead, N.R., Hough, E., Stehney, T.: Security quality requirements engineering (square) methodology. Tech. Rep. CMU/SEI-2005-TR-009, Software Engineering Institute, Carnegie Mellon University (2005)
Mouratidis, H., Giorgini, P.: Secure tropos: A security-oriented extension of the tropos methodology. International Journal of Software Engineering and Knowledge Engineering 17(2), 285–309 (2007)
Nuseibeh, B.: Weaving together requirements and architectures. IEEE Computer 34(3), 115–117 (2001)
Okubo, T., Kaiya, H., Yoshioka, N.: Analyzing impacts on software enhancement caused by security design alternatives with patterns. IJSSE 3(1), 37–61 (2012)
Okubo, T., Kaiya, H., Yoshioka, N.: Mutual refinement of security requirements and architecture using twin peaks model. In: COMPSAC Workshops, pp. 367–372 (2012)
Okubo, T., Yoshioka, N., Kaiya, H.: Security driven requirements refinement and exploration of architecture with multiple nfr points of view. In: IEEE International Symposium on High Assurance on Software Engineering (HASE) (to be appeared, 2014)
Saaty, T.L.: The analytic hierarchy process: planning, priority setting, resource allocation, 2nd edn. RWS, Pittsburgh (1990)
Saeki, M., Kaiya, H.: Security requirements elicitation using method weaving and common criteria. In: MoDELS Workshops, pp. 185–196 (2008)
Tanabe, D., Uno, K., Akemine, K., Yoshikawa, T., Kaiya, H., Saeki, M.: Supporting requirements change management in goal oriented analysis. In: RE, pp. 3–12 (2008)
Weinreich, R., Buchgeher, G.: Integrating requirements and design decisions in architecture representation. In: Babar, M.A., Gorton, I. (eds.) ECSA 2010. LNCS, vol. 6285, pp. 86–101. Springer, Heidelberg (2010)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Okubo, T., Yoshioka, N., Kaiya, H. (2014). Requirements Refinement and Exploration of Architecture for Security and Other NFRs. In: Iliadis, L., Papazoglou, M., Pohl, K. (eds) Advanced Information Systems Engineering Workshops. CAiSE 2014. Lecture Notes in Business Information Processing, vol 178. Springer, Cham. https://doi.org/10.1007/978-3-319-07869-4_27
Download citation
DOI: https://doi.org/10.1007/978-3-319-07869-4_27
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-07868-7
Online ISBN: 978-3-319-07869-4
eBook Packages: Computer ScienceComputer Science (R0)