Abstract
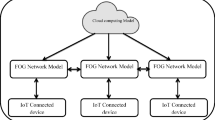
While real-time/near real-time healthcare solutions for the elderly are becoming increasingly popular in medical smart homes, the IT infrastructure and the sensitive information collected using sensor networks can be exposed to cyberattacks. The management of such systems requires 24/7/365 monitoring and partial automation. However, the wide variety of data formats used by the various vendors’ products in medical smart homes cannot be used directly by software agents for data aggregation and data fusion, let alone to support the overall cybersecurity posture. This can be enabled by capturing the semantics of the components of the sensor networks used in these settings. Network anomalies, sensor failure, and sensor data tampering can be detected automatically by performing automated reasoning. In this chapter, we present an overview of knowledge organization systems in a medical smart home environment. We discuss the cyberattack types that occurred in the medical smart home setting and the role of legislation and standards. Finally, we discuss information security countermeasures for cyber-resilience to improve overall the Medical IoT infrastructure.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
Photoplethysmogram.
- 2.
Electrocardiography.
- 3.
Magnetic Resonance Imaging.
- 4.
Computed Tomography.
- 5.
- 6.
Therapeutic Goods Administration.
- 7.
- 8.
Radio Frequency Identification.
- 9.
Wireless Sensor Networks.
References
Mansell Robin (1994) Information and communication technology policy research in the united kingdom: a perspective. Can J Commun 19(1):1–11
Akyildiz IF, Su W, Sankarasubramaniam Y, Cayirci E (2002) Wireless sensor networks: a survey. Comput Netw 38:393–422
Bennasar M, Price BA, Stuart A, Gooch D, Mccormick C, Mehta V, Clare L, Blaine A, Stuart A, Gooch D, Mccormick C, Bandara AK (2019) Knowledge-based architecture for recognising activities of older people. 23rd International Conference on Knowledge-Based and Intelligent Information & Engineering Systems, 159:590–599
Hammi B, Zeadally S, Khatoun R, Nebhen J (2022) Survey on smart homes: vulnerabilities, risks, and countermeasures. Comput Secur 117
Kamel MBM, George LE (2013) Remote patient tracking and monitoring system. Int J Comput Sci Mob Comput 2:88–94
Wazid M, Das AK, Rodrigues JJPC, Shetty S, Park Y (2019) IoMT malware detection approaches: analysis and research challenges. IEEE Access 7:182459–182476
Mitchell Lauren L, Peterson Colleen M, Rud Shaina R, Jutkowitz Eric, Sarkinen Andrielle, Trost Sierra, Porta Carolyn M, Finlay Jessica M, Gaugler Joseph E (2020) “It’s like a cyber-security blanket’’: the utility of remote activity monitoring in family dementia care. J Appl Gerontol 39(1):86–98
World Health Organization (2021) Ageing and health. pp 5–9. Online available at https://www.who.int/news-room/fact-sheets/detail/ageing-and-health
Australian government (2017) Australian law reform commission. Who are older australians? pp 1–8
Frey Bruce B (1996) Health insurance portability and accountability Act. The SAGE Encyclopedia of Educational Research, Measurement, and Evaluation 12–14:2018
Alromaihi S, Elmedany W, Balakrishna C (2018) Cyber security challenges of deploying IoT in smart cities for healthcare applications. In: Proceedings - 2018 IEEE 6th International Conference on Future Internet of Things and Cloud Workshops, W-FiCloud 2018. pp 140–145
Nasiri S, Sadoughi F, Tadayon MH, Dehnad A (2019) Security requirements of internet of things-based healthcare system: a survey study. Acta Inform Med 2(4):253–258
Sikos LF (2019) Data science in cybersecurity and cyberthreat intelligence
Yaqoob Tehreem, Abbas Haider, Atiquzzaman Mohammed (2019) Security vulnerabilities, attacks, countermeasures, and regulations of networked medical devices-a review. IEEE Commun Surv Tutor 21(4):3723–3768
Culmone Rosario, Giuliodori Paolo, Quadrini Michela (2015) Human activity recognition using a semantic ontology-based framework. Int J Adv Intell Syst 8(2):159–168
Sharma N, Mangla M, Mohanty SN, Gupta D, Tiwari P, Shorfuzzaman M, Rawashdeh M(2021) A smart ontology-based IoT framework for remote patient monitoring. Biomed Signal Process Control 68
Martino BD, Esposito A, Liguori S, Ospedale F, Maisto SA, Nacchia S (2018) A fuzzy prolog and ontology driven framework for medical diagnosis using IoT devices. Advances in intelligent systems and computing, 611:875–884
Guerrero E, Nieves JC, Lindgren H (2016) An activity-centric argumentation framework for assistive technology aimed at improving health. Argum Comput 7(1):5–33
Guerrero E, Lindgren H, Nieves JC (2013) ALI, an ambient assisted living system for supporting behavior change. VIII Workshop on Agents Applied in Health Care (A2HC 2013). Mci, pp 81–92
Negin Farhood, Brémond François (2019) An unsupervised framework for online spatiotemporal detection of activities of daily living by hierarchical activity models. Sensors (Switzerland) 19(19):1–34
Mahler T, Elovici Y, Shahar Y (2020) A new methodology for information security risk assessment for medical devices and its evaluation
Hassija V, Chamola V, Bajpai BC, Naren, Zeadally S (2021) Security issues in implantable medical devices: Fact or fiction? Sustain Cities Soc 66(April 2020):102552
Los Angles Times. Hollywood hospital pays \$17,000 in bitcoin to hackers; FBI investigating, pp 1–10
Farringer Deborah R (2017) Send us the bitcoin or patients will die: addressing the risks of ransomware attacks on hospitals. Seattle Univ Law Rev 40(3):16–23
Mahler T, Nissim N, Shalom E, Goldenberg I, Hassman G, Makori A, Kochav I, Elovici Y, Shahar Y (2018) Know your enemy: characteristics of cyber-attacks on medical imaging devices, pp 2–7
Australian Cyber Security Centre (2022) 2020-013 Ransomware targeting australian aged care and healthcare sectors, pp 1–6
Cheu S (2020) Cyber attack warning: Providers advised to take precautions
Boyi Xu, Da Li Xu, Cai Hongming, Xie Cheng, Jingyuan Hu, Fenglin Bu (2014) Ubiquitous data accessing method in iot-based information system for emergency medical services. IEEE Trans Ind Inform 10(2):1578–1586
Dridi A, Sassi S, Faiz S (2018) Towards a semantic medical internet of things. In: Proceedings of IEEE/ACS International Conference on Computer Systems and Applications, AICCSA, Oct-2017. pp 1421–1428
Pazienza A, Polimeno G, Vitulano F, Maruccia Y (2019) Towards a digital future: an innovative semantic iot integrated platform for industry 4.0, healthcare, and territorial control. In: Conference Proceedings - IEEE International Conference on Systems, Man and Cybernetics, Oct-2019. pp 587–592
Mavrogiorgou A, Kiourtis A, Kyriazis D (2020) Identification of IoT medical devices APIs through ontology mapping techniques. EAI/Springer Innovations in Communication and Computing, pp 39–54
Hasan MK, Ghazal TM , Saeed RA, Pandey B, Gohel H, Eshmawi AA, Abdel-Khalek S, Alkhassawneh HM (2022) A review on security threats, vulnerabilities, and counter measures of 5G enabled internet-of-medical-things. IET Commun 16(5):421–432
Ahmed G, Mehmood D, Shahzad K, Malick RAS (2021) An efficient routing protocol for internet of medical things focusing hot spot node problem. Int J Distrib Sens Netw 17(2)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this chapter
Cite this chapter
Bughio, K.S., Sikos, L.F. (2023). Knowledge Organization Systems to Support Cyber-Resilience in Medical Smart Home Environments. In: Ahmed, M., Haskell-Dowland, P. (eds) Cybersecurity for Smart Cities. Advanced Sciences and Technologies for Security Applications. Springer, Cham. https://doi.org/10.1007/978-3-031-24946-4_5
Download citation
DOI: https://doi.org/10.1007/978-3-031-24946-4_5
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-24945-7
Online ISBN: 978-3-031-24946-4
eBook Packages: Physics and AstronomyPhysics and Astronomy (R0)