Abstract
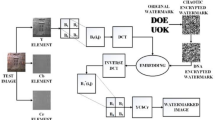
In order to accurately identify the sensitive information in the intangible cultural heritage communication network and realize the reasonable protection of intangible cultural heritage data, a method for protecting the sensitive information in the intangible cultural heritage communication network based on machine learning is proposed. With the support of machine learning algorithm, the distance measurement results are solved, and then the specific values of compressed characteristic indexes are calculated by establishing a random measurement matrix to complete the tracking and processing of the target parameters of intangible cultural heritage. On this basis, according to the encryption processing results of sensitive information, the implementation standard of OSBE protocol is established, and then with the help of the formed sensitive information processing process, the effective protection of sensitive information of intangible cultural heritage communication network is realized. The results of comparative experiments show that under the effect of machine learning algorithm, the recognition accuracy of the network host for the sensitive information of intangible cultural heritage has significantly improved, and it really has strong practical value in the reasonable protection of intangible cultural heritage data parameters.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Gleim, L., Bergs, T., Brecher, C., et al.: FactDAG: formalizing data interoperability in an internet of production. IEEE Internet Things J. 7(4), 3243–3253 (2020)
Kalyakulin, S.Y., Kuz’Min, V.V., Mitin, E.V., et al.: Automated design of information processing in preproduction. Russ. Eng. Res. 40(5), 413–415 (2020)
Wang, L., Xu, Y., Kang, Y.: Simulation of node-level data privacy protection mining method in cloud computing. Comput. Simul. 37(10), 433–436+460 (2020)
Denkena, B., Behrens, B.A., Bergmann, B., et al.: Potential of process information transfer along the process chain of hybrid components for process monitoring of the cutting process. Prod. Eng. Res. Dev. 15(2), 199–209 (2021)
Shuai, L., Shuai, W., Xinyu, L., et al.: Fuzzy detection aided real-time and robust visual tracking under complex environments. IEEE Trans. Fuzzy Syst. 29(1), 90–102 (2021)
Liu, S., et al.: Human memory update strategy: a multi-layer template update mechanism for remote visual monitoring. IEEE Trans. Multimedia 23, 2188–2198 (2021)
Yang, J., Palazzolo, A.: Tilt pad bearing distributed pad inlet temperature with machine learning—Part I: static and dynamic characteristics. J. Tribol. 144(6), 1–45 (2021)
Ostasevicius, V., Karpavicius, P., Paulauskaite-Taraseviciene, A., et al.: A machine learning approach for wear monitoring of end mill by self-powering wireless sensor nodes. Sensors 21(3137), 1–26 (2021)
Liu, S., Liu, D., Muhammad, K., Ding, W.: Effective template update mechanism in visual tracking with background clutter. Neurocomputing 458, 615–625 (2021)
Okumu, F., Ekmekiolu, A., Kara, S.S.: Modelling ships main and auxiliary engine powers with regression-based machine learning algorithms. Pol. Marit. Res. 28(1), 83–96 (2021)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Zhang, X., Jin, Y. (2023). A Method of Protecting Sensitive Information in Intangible Cultural Heritage Communication Network Based on Machine Learning. In: Xu, Y., Yan, H., Teng, H., Cai, J., Li, J. (eds) Machine Learning for Cyber Security. ML4CS 2022. Lecture Notes in Computer Science, vol 13656. Springer, Cham. https://doi.org/10.1007/978-3-031-20099-1_18
Download citation
DOI: https://doi.org/10.1007/978-3-031-20099-1_18
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-20098-4
Online ISBN: 978-3-031-20099-1
eBook Packages: Computer ScienceComputer Science (R0)