Abstract
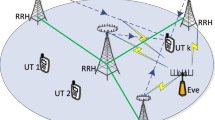
In this paper, we propose and analyze a secret key agreement (SKA) protocol designed for multiple-input multiple-output (MIMO) scenarios, in which a legitimate transmitter estimates the amount of information that can be leaked to potentially hazardous legitimate receivers in the network, generates a secret key, and transmits the generated key to a specific legitimate receiver. For the latter key transmission step, a new beamforming method is proposed that regards other legitimate receivers in the network as untrustworthy nodes and show the attack algorithm they can perform. The proposed protocol requires only one-way transmission and no mutual interaction to share the secret key. Through numerical simulations, we evaluate two scenarios for malicious users, where a part of them are other legitimate receivers. Namely, we evaluate the information leakage risk of our model under two conditions: a disadvantage for them, where the malicious user is unaware of the existence of beamforming, and an advantage, where the user can jam directly to the beamformer. Finally, to demonstrate the practicality of the protocol, we demonstrate that the beamforming advantage dramatically reduces the computational complexity requirement at the legitimate receiver.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
In our future work, we consider the case where \(N_\textrm{E}\) is large.
References
Rivest, R.L., Shamir, A., Adleman, L.: A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 21(2), 120–126 (1978)
Shor, P.: Algorithms for quantum computation: discrete logarithms and factoring. In: 35th Annual Symposium on Foundations of Computer Science, pp. 124–134, November 1994
Mucchi, L., et al.: Physical-layer security in 6G networks. IEEE Open J. Commun. Soc. 2, 1901–1914 (2021)
Khisti, A., Wornell, G., Wiesel, A., Eldar, Y.: On the gaussian MIMO wiretap channel. In: IEEE International Symposium on Information Theory, pp. 2471–2475, June 2007
Maurer, U.M.: Secret key agreement by public discussion from common information. IEEE Trans. Inf. Theory 39(3), 733–742 (1993)
Sharifian, S., Poostindouz, A., Safavi-Naini, R.: A capacity-achieving one-way key agreement with improved finite blocklength analysis. In: International Symposium on Information Theory and Its Applications, pp. 407–411, October 2020
Dean, T.R., Goldsmith, A.J.: Physical-layer cryptography through massive MIMO. IEEE Trans. Inf. Theory 63(8), 5419–5436 (2017)
Gallager, R.: Low-density parity-check codes. IRE Trans. Inf. Theory 8(1), 21–28 (1962)
Muramatsu, J., Miyake, S.: Construction of codes for the wiretap channel and the secret key agreement from correlated source outputs based on the hash property. IEEE Trans. Inf. Theory 58(2), 671–692 (2012)
Wang, L., Bashar, S., Wei, Y., Li, R.: Secrecy enhancement analysis against unknown eavesdropping in spatial modulation. IEEE Commun. Lett. 19(8), 1351–1354 (2015)
Acknowledgement
This work was partially supported by JST SICORP Grant Number JPMJSC20C1, Japan.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Otsuka, S., Iimori, H., Ando, K., de Abreu, G.T.F., Ishibashi, K., Ishikawa, N. (2023). Analysis of Secret Key Agreement Protocol for Massive MIMO Systems. In: García Bringas, P., et al. International Joint Conference 15th International Conference on Computational Intelligence in Security for Information Systems (CISIS 2022) 13th International Conference on EUropean Transnational Education (ICEUTE 2022). CISIS ICEUTE 2022 2022. Lecture Notes in Networks and Systems, vol 532. Springer, Cham. https://doi.org/10.1007/978-3-031-18409-3_9
Download citation
DOI: https://doi.org/10.1007/978-3-031-18409-3_9
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-18408-6
Online ISBN: 978-3-031-18409-3
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)