Abstract
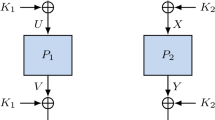
We propose a new construction for format-preserving encryption. Our design provides the flexibility for use in format-preserving encryption (FPE) and for static table-driven tokenization. Our algorithm is a substitution-permutation network based on random Sboxes. Using pseudorandom generators and pseudorandom functions, we prove a strong adaptive security based on the super-pseudorandom permutation assumption of our core design. We obtain empirical parameters to reach this assumption. We suggest parameters for quantum security.
Our design accommodates very small domains, with a radix a from 4 to the Unicode alphabet size and a block length \(\ell \) starting 2. The number of Sbox evaluations per encryption is asymptotically \(\ell ^{\frac{3}{2}}\), which is also the number of bytes we need to generate using \(\mathsf {AES}\) in \(\mathsf {CTR}\) mode for each tweak setup. For instance, we tokenize 10 decimal digits using 29 (parallel) \(\mathsf {AES}\) computations to be done only once, when the tweak changes.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
Note that we want exact format preservation hence no stretch in theciphertext. Consequently, FPE cannot authenticate at the same time and authenticationcannot be used to defeat chosen ciphertext attacks.
- 2.
There exists another FAST algorithm in the literature which is unrelated [14].
- 3.
A permutation \(\pi \) is called even if the number of (x, y) pairs such that \(x<y\) and \(\pi (x)>\pi (y)\) is even.
- 4.
We will only use \(\lambda =L_1=L_2\). So, the superscript \(\lambda \) is only an informative notation.
- 5.
Forcing the last two bytes of \(\mathsf {IV}\) to 0 avoids that some slide properties in coins such as \(\mathsf {IV}'=\mathsf {IV}+1\) and \(K'=K\) may occur (although the complexity to obtain such properties could be very high).
- 6.
Interestingly, if the algorithm generating coins is secure, there is no need to care about constant-time implementation for the Sbox generations as discussed in Sect. 5.
- 7.
We tested other Intel CPUs and obtained comparable results.
- 8.
- 9.
Our code is available on https://github.com/comForte/Format-Preserving-Encryption.
- 10.
- 11.
A “chosen S attack” leads to trivial attacks. For instance, the adversary could pick all Sboxes equal, or all Sboxes linear (over \({\mathbf{Z}}_a\)). Therefore, we do not consider chosen-S models.
References
Retail Financial Services - Requirements for Protection of Sensitive Payment Card Data - Part 1: Using Encryption Method. ANSI X9.119-1-2016. American National Standards Institute
Retail Financial Services - Requirements for Protection of Sensitive Payment Card Data - Part 2: Implementing Post Authorization Tokenization Systems. ANSI X9.119-2-2017. American National Standards Institute
Recommendation for Block Cipher Modes of Operation: Methods for Format Preserving Encryption. NIST Special Publication (SP) 800–38G. National Institute of Standards and Technology. http://dx.doi.org/10.6028/NIST.SP.800-38G
Baignères, T., Finiasz, M.: Dial C for cipher. In: Biham, E., Youssef, A.M. (eds.) SAC 2006. LNCS, vol. 4356, pp. 76–95. Springer, Heidelberg (2007). https://doi.org/10.1007/978-3-540-74462-7_7
Baignères, T., Stern, J., Vaudenay, S.: Linear cryptanalysis of non binary ciphers. In: Adams, C., Miri, A., Wiener, M. (eds.) SAC 2007. LNCS, vol. 4876, pp. 184–211. Springer, Heidelberg (2007). https://doi.org/10.1007/978-3-540-77360-3_13
Bellare, M., Hoang, V.T., Tessaro, S.: Message-recovery attacks on feistel-based format-preserving encryption. In: 23rd ACM Conference on Computer and Communications Security, Vienna, Austria, pp. 444–455. ACM Press (2016)
Bellare, M., Ristenpart, T., Rogaway, P., Stegers, T.: Format-preserving encryption. In: Jacobson, M.J., Rijmen, V., Safavi-Naini, R. (eds.) SAC 2009. LNCS, vol. 5867, pp. 295–312. Springer, Heidelberg (2009). https://doi.org/10.1007/978-3-642-05445-7_19
Bellare, M., Rogaway, P., Spies, T.: The FFX mode of operation for format-preserving encryption. http://csrc.nist.gov/groups/ST/toolkit/BCM/documents/proposedmodes/ffx/ffx-spec.pdf
Biham, E.: How to Decrypt or even Substitute DES-Encrypted Messages in \(2^{28}\) steps. Inf. Process. Lett. 84, 117–124 (2002)
Biryukov, A., Khovratovich, D.: Related-key cryptanalysis of the full AES-192 and AES-256. In: Matsui, M. (ed.) ASIACRYPT 2009. LNCS, vol. 5912, pp. 1–18. Springer, Heidelberg (2009). https://doi.org/10.1007/978-3-642-10366-7_1
Black, J., Rogaway, P.: Ciphers with arbitrary finite domains. In: Preneel, B. (ed.) CT-RSA 2002. LNCS, vol. 2271, pp. 114–130. Springer, Heidelberg (2002). https://doi.org/10.1007/3-540-45760-7_9
Brier, E., Peyrin, T., Stern, J.: BPS: a format-preserving encryption proposal. http://csrc.nist.gov/groups/ST/toolkit/BCM/documents/proposedmodes/bps/bps-spec.pdf
Brightwell, M., Smith, H.: Using datatype-preserving encryption to enhance data warehouse security. In: 20th NISSC Proceedings, pp. 141–149 (1997). http://csrc.nist.gov/nissc/1997/proceedings/141.pdf
Chakraborty, D., Ghosh, S., López, C.M., Sarkar, P.: FAST: Disk Encryption and Beyond. Eprint 2017/849 https://eprint.iacr.org/2017/849
Chang, D., et al.: SPF: a new family of efficient format-preserving encryption algorithms. In: Chen, K., Lin, D., Yung, M. (eds.) Inscrypt 2016. LNCS, vol. 10143, pp. 64–83. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-54705-3_5
Chang, D., Ghosh, M., Jati, A., Kumar, A., Sanadhya, S.K.: eSPF: a family of format-preserving encryption algorithms using MDS matrices. In: Ali, S.S., Danger, J.-L., Eisenbarth, T. (eds.) SPACE 2017. LNCS, vol. 10662, pp. 133–150. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-71501-8_8
Durak, F.B., Horst, H., Horst, M., Vaudenay, S.: FAST: Secure and High Performance Format-Preserving Encryption and Tokenization. Eprint 2021/1171 https://eprint.iacr.org/2021/1171
Durak, F.B., Vaudenay, S.: Breaking the FF3 format-preserving encryption standard over small domains. In: Katz, J., Shacham, H. (eds.) CRYPTO 2017. LNCS, vol. 10402, pp. 679–707. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-63715-0_23. Eprint 2017/521 https://eprint.iacr.org/2017/521
Feistel, H.: Cryptography and computer privacy. Sci. Am. 228(5), 15–23 (1973). https://www.jstor.org/stable/10.2307/24923044
Granboulan, L., Levieil, É., Piret, G.: Pseudorandom permutation families over abelian groups. In: Robshaw, M. (ed.) FSE 2006. LNCS, vol. 4047, pp. 57–77. Springer, Heidelberg (2006). https://doi.org/10.1007/11799313_5
Grover, L.K.: A fast quantum mechanical algorithm for database search. In: Proceedings of the 28th ACM Symposium on Theory of Computing, Philadelphia, Pennsylvania, U.S.A., pp. 212–219. ACM Press (1996)
Hoang, V.T., Miller, D., Trieu, N.: Attacks only get better: how to break FF3 on large domains. In: Ishai, Y., Rijmen, V. (eds.) EUROCRYPT 2019. LNCS, vol. 11477, pp. 85–116. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-17656-3_4. Eprint 2019/244 https://eprint.iacr.org/2019/244
Hoang, V.T., Tessaro, S., Trieu, N.: The curse of small domains: new attacks on format-preserving encryption. In: Shacham, H., Boldyreva, A. (eds.) CRYPTO 2018. LNCS, vol. 10991, pp. 221–251. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-96884-1_8. Eprint 2018/556 https://eprint.iacr.org/2018/556
Knuth, D.E.: Seminumerical Algorithms – The Art of Computer Programming (3rd ed.). Addison-Wesley, Boston (1998)
Lemire, D.: Fast Random Generation in an Interval. arXiv:1805.10941v4 (2018). https://arxiv.org/pdf/1805.10941.pdf
Lumbroso, J.: Optimal Discrete Uniform Generation from Coin Flips, and Applications. arXiv:1304.1916v1 (2013). https://arxiv.org/pdf/1304.1916.pdf
Liskov, M., Rivest, R.L., Wagner, D.: Tweakable block ciphers. J. Cryptol. 24, 588–613 (2011)
Merkle, R.C.: Fast software encryption functions. In: Menezes, A.J., Vanstone, S.A. (eds.) CRYPTO 1990. LNCS, vol. 537, pp. 477–501. Springer, Heidelberg (1991). https://doi.org/10.1007/3-540-38424-3_34
Rogaway, P.: A synopsis of format preserving encryption (2010). http://web.cs.ucdavis.edu/~rogaway/papers/synopsis.pdf
Schneier, B.: Description of a new variable-length key, 64-bit block cipher (Blowfish). In: Anderson, R. (ed.) FSE 1993. LNCS, vol. 809, pp. 191–204. Springer, Heidelberg (1994). https://doi.org/10.1007/3-540-58108-1_24
Schroeppel, R.: The Hasty Pudding Cipher. AES submission (1998)
Simon, D.R.: On the power of quantum computation. SIAM J. Comput. 26(5), 1474–1483 (1997)
Spies, T.: Format Preserving Encryption. White paper (2008). https://www.voltage.com/wp-content/uploads/Voltage-Security-WhitePaper-Format-Preserving-Encryption.pdf
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 International Association for Cryptologic Research
About this paper
Cite this paper
Durak, F.B., Horst, H., Horst, M., Vaudenay, S. (2021). FAST: Secure and High Performance Format-Preserving Encryption and Tokenization. In: Tibouchi, M., Wang, H. (eds) Advances in Cryptology – ASIACRYPT 2021. ASIACRYPT 2021. Lecture Notes in Computer Science(), vol 13092. Springer, Cham. https://doi.org/10.1007/978-3-030-92078-4_16
Download citation
DOI: https://doi.org/10.1007/978-3-030-92078-4_16
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-92077-7
Online ISBN: 978-3-030-92078-4
eBook Packages: Computer ScienceComputer Science (R0)