Abstract
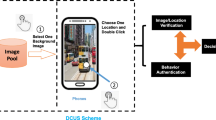
Smartphones have gained huge popularity and rapidly changed the way of people’s living habits and communication style. Despite the widespread adoption, there is a big challenge to protect data security on smartphones. This is because phone users often store their personal data (e.g., images) and proceed sensitive tasks (e.g., financial operations) on the device. To secure the device from unauthorized access, designing an appropriate unlocking mechanism is an expected solution. To complement existing schemes, we advocate that combining behavioral biometrics can enhance the security of unlocking mechanisms. In this work, we develop a double-click-based unlocking scheme (DCUS), which allows users to unlock the phone by double clicking on the pre-selected location on an image. For verification, DCUS has to check selected images, image location and behavioral features of double-click action. In the user study, we involve 40 participants and explore some common supervised algorithms. The results demonstrate that participants can achieve a good success rate (over 96%) with positive feedback.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Aviv, A.J., Gibson, K., Mossop, E., Blaze, M., Smith, J.M.: Smudge attacks on smartphone touch screens. In: Proceedings of the 4th USENIX Conference on Offensive Technologies, pp. 1–7. USENIX Association (2010)
Al-Sudani, A.R., Gao, S., Wen, S., Al-Khiza’ay, M.: Checking an authentication of person depends on RFID with thermal image. SpaCCS 2018, 371–380 (2018)
Bonneau, J.: The science of guessing: analyzing an anonymized corpus of 70 million passwords. In: Proceedings of the 2012 IEEE Symposium on Security and Privacy, pp. 538–552 (2012)
De Luca, A., Hang, A., Brudy, F., Lindner, C., Hussmann, H.: Touch me once and i know it’s you!: implicit authentication based on touch screen patterns. In: Proceedings of CHI, pp. 987–996. ACM (2012)
Deloitte’s 2019 global mobile consumer survey. https://www2.deloitte.com/content/dam/insights/us/articles/glob43115_2019-global-mobile-survey/DI_2019-global-mobile-survey.pdf
Feng, T., et al.: Continuous mobile authentication using touchscreen gestures. In: Proceedings of the 2012 IEEE Conference on Technologies for Homeland Security (HST), pp. 451–456. IEEE, USA (2012)
Findling, R.D., Mayrhofer, R.: Towards face unlock: on the difficulty of reliably detecting faces on mobile phones. In: MoMM, pp. 275–280 (2012)
Frank, M., Biedert, R., Ma, E., Martinovic, I., Song, D.: Touchalytics: on the applicability of touchscreen input as a behavioral biometric for continuous authentication. IEEE Trans. Inf. Forensics Secur. 8(1), 136–148 (2013)
Gomez-Barrero, M., Galbally, J.: Reversing the irreversible: a survey on inverse biometrics. Comput. Secur. 90, 101700 (2020)
Guo, Y., Yang, L., Ding, X., Han, J., Liu, Y.: OpenSesame: unlocking smart phone through handshaking biometrics. In: INFOCOM, pp. 365–369 (2013)
Izuta, R., Murao, K., Terada, T., Iso, T., Inamura, H., Tsukamoto, M.: Screen unlocking method using behavioral characteristics when taking mobile phone from pocket. In: MoMM, pp. 110–114 (2016)
Larrucea, X., Moffie, M., Asaf, I.S.: Santamaria: towards a GDPR compliant way to secure European cross border healthcare industry 4.0. Comput. Stand. Interfaces 69, 103408 (2020)
Li, Y., et al.: A closer look tells more: a facial distortion based liveness detection for face authentication. In: AsiaCCS, pp. 241–246 (2019)
Li, Y., Cheng, Y., Meng, W., Li, Y., Deng, R.H.: Designing leakage-resilient password entry on head-mounted smart wearable glass devices. IEEE Trans. Inf. Forensics Secur. 16, 307–321 (2021)
Li, W., Tan, J., Meng, W., Wang, Yu., Li, J.: SwipeVLock: a supervised unlocking mechanism based on swipe behavior on smartphones. In: Chen, X., Huang, X., Zhang, J. (eds.) ML4CS 2019. LNCS, vol. 11806, pp. 140–153. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-30619-9_11
Li, W., Tan, J., Meng, W., Wang, Y.: A swipe-based unlocking mechanism with supervised learning on smartphones: design and evaluation. J. Netw. Comput. Appl 165, 102687 (2020)
Meng, Y.: Designing click-draw based graphical password scheme for better authentication. In: Proceedings of the 7th IEEE International Conference on Networking, Architecture, and Storage (NAS), pp. 39–48 (2012)
Meng, Y., Li, W., Kwok, L.-F.: Enhancing click-draw based graphical passwords using multi-touch on mobile phones. In: Proceedings of the 28th IFIP TC 11 International Information Security and Privacy Conference (IFIP SEC), IFIP Advances in Information and Communication Technology, vol. 405, pp. 55–68 (2013)
Meng, W., Wong, D.S., Furnell, S., Zhou, J.: Surveying the development of biometric user authentication on mobile phones. IEEE Commun. Surv. Tutorials 17(3), 1268–1293 (2015)
Meng, W.: RouteMap: a route and map based graphical password scheme for better multiple password memory. In: Proceedings of the 9th International Conference on Network and System Security (NSS), pp. 147–161 (2015)
Meng, W.: Evaluating the effect of multi-touch behaviours on android unlock patterns. Inf. Comput. Secur. 24(3), 277–287 (2016)
Meng, W., Li, W., Wong, D.S., Zhou, J.: TMGuard: a touch movement-based security mechanism for screen unlock patterns on smartphones. In: Proceedings of the 14th International Conference on Applied Cryptography and Network Security (ACNS), pp. 629–647 (2016)
Meng, W., Lee, W.H., Liu, Z., Su, C., Li, Y.: Evaluating the impact of juice filming charging attack in practical environments. In: Kim, H., Kim, D.-C. (eds.) ICISC 2017. LNCS, vol. 10779, pp. 327–338. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-78556-1_18
Meng, W., Fei, F., Li, W., Au, M.H.: Harvesting smartphone privacy through enhanced juice filming charging attacks. In: Proceedings of ISC, pp. 291–308 (2017)
Meng, W., Li, W., Kwok, L.-F., Choo, K.-K.R.: Towards enhancing click-draw based graphical passwords using multi-touch behaviours on smartphones. Comput. Secur. 65, 213–229 (2017)
Meng, W., Li, W., Lee, W., Jiang, L., Zhou, J.: A Pilot Study of Multiple Password Interference between Text and Map-based Passwords. In: Proceedings of the 15th International Conference on Applied Cryptography and Network Security (ACNS), pp. 145–162 (2017)
Meng, W., Lee, W.H., Au, M.H., Liu, Z.: Exploring effect of location number on map-based graphical password authentication. In: Pieprzyk, J., Suriadi, S. (eds.) ACISP 2017. LNCS, vol. 10343, pp. 301–313. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-59870-3_17
Nyang, D., Kim, H., Lee, W., Kang, S., Cho, G., Lee, M.K., Mohaisen, A.: Two-thumbs-up: physical protection for PIN entry secure against recording attacks. Comput. Secur. 78, 1–15 (2018)
Shepard, R.N.: Recognition memory for words, sentences, and pictures. J. Verbal Learn. Verbal Behav. 6(1), 156–163 (1967)
Smith-Creasey, M., Rajarajan, M.: A continuous user authentication scheme for mobile devices. In: Proceedings of the 14th Annual Conference on Privacy, Security and Trust (PST), pp. 104–113 (2016)
Spitzer, J., Singh, C., Schweitzer, D.: A security class project in graphical passwords. J. Comput. Sci. Coll. 26(2), 7–13 (2010)
Shahzad, M., Liu, A.X., Samuel, A.: Behavior based human authentication on touch screen devices using gestures and signatures. IEEE Trans. Mob. Comput. 16(10), 2726–2741 (2017)
Sharma, V., Enbody, R.: User authentication and identification from user interface interactions on touch-enabled devices. In: Proceedings of the 10th ACM Conference on Security and Privacy in Wireless and Mobile Networks (WiSec), pp. 1–11 (2017)
Suo, X., Zhu, Y., Owen, G.S.: Graphical passwords: a survey. In: Proceedings of the 21st Annual Computer Security Applications Conference (ACSAC), pp. 463–472. IEEE Computer Society, USA (2005)
Sun, H., Chen, Y., Fang, C., Chang, S.: PassMap: a map based graphical-password authentication system. In: Proceedings of AsiaCCS, pp. 99–100 (2012)
Tao, H., Adams, C.: Pass-Go: a proposal to improve the usability of graphical passwords. Int. J. Netw. Secur. 2(7), 273–292 (2008)
Thorpe, J., MacRae, B., Salehi-Abari, A.: Usability and security evaluation of geopass: a geographic location-password scheme. In: Proceedings of the 9th Symposium on Usable Privacy and Security (SOUPS), pp. 1–14 (2013)
Wang, L., et al.: Unlock with your heart: heartbeat-based authentication on commercial mobile phones. In: Proceedings of ACM Interactive, Mobile, Wearable Ubiquitous Technologies, vol. 2, no. 3, pp. 140:1–140:22 (2018)
Weka: Machine Learning Software in Java. https://www.cs.waikato.ac.nz/ml/weka/
Wiedenbeck, S., Waters, J., Birget, J.-C., Brodskiy, A., Memon, N.: Passpoints: design and longitudinal evaluation of a graphical password system. Int. J. Hum.-Comput. Stud. 63(1–2), 102–127 (2005)
Weir, M., Aggarwal, S., Collins, M., Stern, H.: Testing metrics for password creation policies by attacking large sets of revealed passwords. In: Proceedings of CCS, pp. 162–175 (2010)
Yi, S., Qin, Z., Carter, N., Li, Q.: WearLock: unlocking your phone via acoustics using smartwatch. In: ICDCS, pp. 469–479 (2017)
Zheng, N., Bai, K., Huang, H., Wang, H.: You are how you touch: user verification on smartphones via tapping behaviors. In: Proceedings of the 2014 International Conference on Network Protocols (ICNP), pp. 221–232 (2014)
Acknowledgments
We would like to thank the participants for their hard work in the user study. This work was partially supported by National Natural Science Foundation of China (No. 61802080 and 61802077).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 Springer Nature Switzerland AG
About this paper
Cite this paper
Li, W., Tan, J., Zhu, N., Wang, Y. (2021). Designing Double-Click-Based Unlocking Mechanism on Smartphones. In: Wang, G., Chen, B., Li, W., Di Pietro, R., Yan, X., Han, H. (eds) Security, Privacy, and Anonymity in Computation, Communication, and Storage. SpaCCS 2020. Lecture Notes in Computer Science(), vol 12383. Springer, Cham. https://doi.org/10.1007/978-3-030-68884-4_47
Download citation
DOI: https://doi.org/10.1007/978-3-030-68884-4_47
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-68883-7
Online ISBN: 978-3-030-68884-4
eBook Packages: Computer ScienceComputer Science (R0)