Abstract
Currently, the design of cost functions which measure the embedding distortion becomes the main task left in steganography with the emergence of Syndrome-Trellis Codes. Whether heuristically designed, e.g., Hill, WOW, or statistical model-based, e.g., HUGO, MiPOD, the embedding distortion is almost a sum of each element’s distortion. This paper proposes a new non-additive cost function designed by incorporating an eight-element neighborhood Gaussian Markov Random Field Model (8-GMRF). This proposed scheme, which could be viewed as an extension to MiPOD, derives change probabilities from minimizing the total KL divergence with a given payload and then implements adaptive steganography. Experimental results demonstrate that the proposed 8-GMRF performs superior or comparable to some of the state-of-the-art schemes in resisting steganalysis detectors.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Li, B., Wang, M., Huang, J.: A new cost function for spatial image steganography. In: Proceedings IEEE ICIP, Pairs, France, 27–30 October 2014
Filler, T., Judas, J., Fridrich, J.: Minimizing additive distortion in steganography using syndrome-trellis codes. IEEE TIFS 6(3), 920–935 (2011)
Sedighi, V., Fridrich, J., Cogranne, R.: Content-adaptive pentary steganography using the multivariate generalized Gaussian cover model. In: Proceedings of the SPIE 9409, Media Watermarking, Security, and Forensics 2015, 9409H, 4 March 2015
Sedighi, V., Cogranne, R., Fridrich, J.: Content-adaptive steganography by minimizing statistical detectability. IEEE TIFS 11(2), 221–234 (2016)
Holub, V., Fridrich, J.: Designing steganographic distortion using directional filters. In: Fourth IEEE International Workshop on Information Forensics and Security (2012)
Pevný, T., Filler, T., Bas, P.: Using high-dimensional image models to perform highly undetectable steganography. In: Böhme, R., Fong, P.W.L., Safavi-Naini, R. (eds.) IH 2010. LNCS, vol. 6387, pp. 161–177. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-16435-4_13
Pevny, T., Bas, P., Fridrich, J.: Steganalysis by subtractive pixel adjacency matrix. IEEE Trans. Inf. Forensics Secur. 5(2), 215–224 (2010)
Fridrich, J., Kodovský, J.: Rich models for steganalysis of digital images. IEEE TIFS 7, 868–882 (2011)
Chen, L., Shi, Y.Q., Sutthiwan, P., Niu, X.: Non-uniform quantization in breaking HUGO. In: Shi, Y.Q., Kim, H.-J., Pérez-González, F. (eds.) IWDW 2013. LNCS, vol. 8389, pp. 48–62. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-662-43886-2_4
Fridrich, J., Kodovský, J.: Multivariate Gaussian model for designing additive distortion for steganography. In: Proceedings of the IEEE ICASSP, 26–31 May 2013
Denemark, T., Sedighi, V., Holub, V., Cogranne, R., Fridrich, J.: Selection-channel-aware rich model for steganalysis of digital images. In: Proceedings of the IEEE WIFS, Atlanta, GA, 3–5 December 2014
Holub, V., Fridrich, J.: Digital image steganography using universal distortion. In: Proceedings of the First ACM Workshop on Information Hiding and Multimedia Security, pp. 59–68. ACM (2013)
Holub, V., Fridrich, J., Denemark, T.: Universal distortion function for steganography in an arbitrary domain. EURASIP J. Inf. Secur. 2014(1), 1–13 (2014). https://doi.org/10.1186/1687-417X-2014-1
Bas, P., Filler, T., Pevný, T.: “Break our steganographic system”: the ins and outs of organizing BOSS. In: Filler, T., Pevný, T., Craver, S., Ker, A. (eds.) IH 2011. LNCS, vol. 6958, pp. 59–70. Springer, Heidelberg (2011). https://doi.org/10.1007/978-3-642-24178-9_5
Kodovsky, J., Fridrich, J., Holub, V.: Ensemble classifiers for steganalysis of digital media. IEEE Trans. Inf. Forensics Secur. 7(2), 432–444 (2012)
Acknowledgments
This work is supported in part by National Natural Science Foundation of China under Grants 61772573 and U1736215, and in part by the Science and Technology Program of Guangzhou under Grants 201707010029 and 201804010265.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Appendix
Appendix
1.1 A. Joint probability of one 8-element neighborhood GMRF block
Recall Fig. 1, which illustrates 9 pixels of one block with index \(\mathrm{{\{0}} \sim \mathrm{{8\}}}\). Every two pixels are adjacent if connected or independent if disconnected. For those independent (e.g. pixels, i, j), we can easily obtain (14). Accordingly, we proceed with a group of pixels according to Markovianity shown in (15), which will be repeatedly used in this proof.
Firstly, it is obvious to get (16) using (15) and then take the second term of former formula repeatedly we can get (17). (18) is derived from (17).
Substitute (18) into (17), (17) into (16), \(p(0 \sim 8)\) can be formulated as:
1.2 B. \(2 \times 2\) steganographic Fisher Information matrix
Stimulated by one-dimensional steganographic Fisher Information (2) in MG, we construct \(2 \times 2\) steganographic Fisher Information matrix as following:
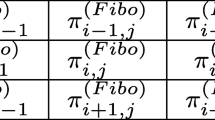
where \(I_{ij}^{(12)}(0) = I_{ij}^{(21)}(0) = {\sum _{k,l}}\frac{1}{{{p_{k,l}}}}(\frac{{\partial {q_{k,l}}({\beta _i},{\beta _j})}}{{\partial {\beta _i}}}{|_{{\beta _i},{\beta _j} = 0}}) \cdot (\frac{{\partial {q_{k,l}}({\beta _i},{\beta _j})}}{{\partial {\beta _j}}}{|_{{\beta _i},{\beta _j} = 0}})\),
Note that \({p_{k,l}}\), i.e. \( p_{k,l}^{(i,j)}\), equals \(P\{ {x_i} = k,{x_j} = l\}\), which can seemed as a point in the two-dimensional Gaussian distribution \(f({x_i},{x_j})\) (21). \({x_i},{x_j},k,l\) are used as continuous for differential and integration in this proof. Given \({p_{k,l}} = f(k,l),{p_{k \pm 1,l}} = f(k \pm 1,l),{p_{k,l \pm 1}} = f(k,l \pm 1)\), we have the Taylor approximation at points \((k \pm 1,l),(k,l \pm 1)\):
After substituting (21)–(23) and (8) into (20), we can finally derive:
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Tong, Y., Ni, J., Su, W. (2020). Image Steganography Using an Eight-Element Neighborhood Gaussian Markov Random Field Model. In: Wang, H., Zhao, X., Shi, Y., Kim, H., Piva, A. (eds) Digital Forensics and Watermarking. IWDW 2019. Lecture Notes in Computer Science(), vol 12022. Springer, Cham. https://doi.org/10.1007/978-3-030-43575-2_21
Download citation
DOI: https://doi.org/10.1007/978-3-030-43575-2_21
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-43574-5
Online ISBN: 978-3-030-43575-2
eBook Packages: Computer ScienceComputer Science (R0)