Abstract
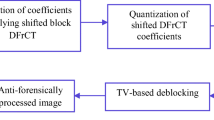
Bianchi et al. proposed a method to detect the non-aligned double JPEG (NAD-JPEG) compression using the presence of distortions in the Integer Periodicity Map (IPM) of DC coefficients of any JPEG image. However, we found that the IPM can be easily altered without affecting the visual quality of an image. In this paper, we propose a new anti-forensics scheme that alters the IPM to deceive the Bianchi et al. scheme. In our proposed method, a statistical model of the DC coefficients from singly compressed JPEG image is used to generate an estimated image which is free from quantization artifacts that are present in the IPM. The estimated image is subjected to NAD-JPEG compression. It was found that the DC values of NAD-JPEG image are no longer be the multiples of the corresponding primary quantization step size \(q_1\). As a result, the DCT coefficients do not cluster around the lattice related to the \(q_1\) and the IPM of the double JPEG compressed image seems to be the IPM of a singly compressed JPEG image. Experimental results show the effectiveness of the proposed anti-forensics scheme as the accuracy of the said forensics method get reduced to less than \(50\%\) in case of anti-forensically modified images.
This work is supported by Ministry of Electronics and Information Technology, Govt. of India; grant no “12(1)/2017-CSRD”.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Bianchi, T., Piva, A.: Detection of nonaligned double JPEG compression based on integer periodicity maps. IEEE Trans. Inf. Forensics Secur. 7(2), 842–848 (2012). https://doi.org/10.1109/TIFS.2011.2170836
Chu, X., Stamm, M.C., Chen, Y., Liu, K.J.R.: On antiforensic concealability with rate-distortion tradeoff. IEEE Trans. Image Process. 24(3), 1087–1100 (2015)
Dang-Nguyen, D.T., Pasquini, C., Conotter, V., Boato, G.: RAISE: a raw images dataset for digital image forensics. In: Proceedings of the 6th ACM Multimedia Systems Conference, MMSys 2015, pp. 219–224. ACM, New York (2015). https://doi.org/10.1145/2713168.2713194
Das, T.K.: Anti-forensics of JPEG compression detection schemes using approximation of DCT coefficients. Multimed. Tools Appl. 77(24), 31835–31854 (2018). https://doi.org/10.1007/s11042-018-6170-7
Fan, W., Wang, K., Cayre, F., Xiong, Z.: JPEG anti-forensics with improved tradeoff between forensic undetectability and image quality. IEEE Trans. Inf. Forensics Secur. 9(8), 1211–1226 (2014)
Fan, Z., de Queiroz, R.L.: Identification of bitmap compression history: JPEG detection and quantizer estimation. IEEE Trans. Image Process. 12(2), 230–235 (2003)
Farid, H.: A survey of image forgery detection. IEEE Signal Process. Mag. 2(26), 16–25 (2009)
Huang, F., Huang, J., Shi, Y.Q.: Detecting double JPEG compression with the same quantization matrix. IEEE Trans. Inf. Forensics Secur. 5(4), 848–856 (2010)
Lai, S.Y., Böhme, R.: Countering counter-forensics: the case of JPEG compression. In: Filler, T., Pevný, T., Craver, S., Ker, A. (eds.) IH 2011. LNCS, vol. 6958, pp. 285–298. Springer, Heidelberg (2011). https://doi.org/10.1007/978-3-642-24178-9_20
Li, H., Luo, W., Huang, J.: Anti-forensics of double JPEG compression with the same quantization matrix. Multimed. Tools Appl. 74(17), 6729–6744 (2015)
Lukáš, J., Fridrich, J.: Estimation of primary quantization matrix in double compressed JPEG images. In: Proceedings of DFRWS (2003)
Luo, W., Huang, J., Qui, G.: JPEG error analysis and its applications to digital image forensics. IEEE Trans. Inf. Forensics Secur. 5(3), 480–491 (2010)
Milani, S., Tagliasacchi, M., Tubaro, S.: Discriminating multiple jpeg compression using first digit features. In: 2012 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), pp. 2253–2256, March 2012
Niu, Y., Li, X., Zhao, Y., Ni, R.: An enhanced approach for detecting double JPEG compression with the same quantization matrix. Sig. Process.: Image Commun. 76, 89–96 (2019)
Pevny, T., Fridrich, J.: Detection of double-compression in JPEG images for applications in steganography. IEEE Trans. Inf. Forensics Secur. 3(2), 247–258 (2008)
Schaefer, G., Stich, M.: UCID: an uncompressed color image database. In: Yeung, M.M., Lienhart, R.W., Li, C.S. (eds.) Storage and Retrieval Methods and Applications for Multimedia 2004, vol. 5307, pp. 472–480, December 2003. https://doi.org/10.1117/12.525375
Singh, G., Singh, K.: Improved JPEG anti-forensics with better image visual quality and forensic undetectability. Forensic Sci. Int. 277 (2017). https://doi.org/10.1016/j.forsciint.2017.06.003
Stamm, M.C., Tjoa, S.K., Lin, W.S., Liu, K.J.R.: Anti-forensics of JPEG compression. In: 2010 IEEE International Conference on Acoustics, Speech and Signal Processing, pp. 1694–1697, March 2010. https://doi.org/10.1109/ICASSP.2010.5495491
Taimori, A., Razzazi, F., Behrad, A., Ahmadi, A., Babaie-Zadeh, M.: Quantization-unaware double JPEG compression detection. J. Math. Imaging Vis. 54(3), 269–286 (2016)
Uehara, T., Safavi-Naini, R., Ogunbona, P.: Recovering DC coefficients in block-based DCT. IEEE Trans. Image Process. 15(11), 3592–3596 (2006). https://doi.org/10.1109/TIP.2006.881939
Wei, H., Yao, H., Qin, C., Tang, Z.: Automatic forgery localization via artifacts analysis of JPEG and resampling. In: Yang, C.-N., Peng, S.-L., Jain, L.C. (eds.) SICBS 2018. AISC, vol. 895, pp. 221–234. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-16946-6_18
Xue, F., Lu, W., Ye, Z., Liu, H.: JPEG image tampering localization based on normalized gray level co-occurrence matrix. Multimed. Tools Appl. 78(8), 9895–9918 (2019). https://doi.org/10.1007/s11042-018-6611-3
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Switzerland AG
About this paper
Cite this paper
Bhaduri Mandal, A., Das, T.K. (2019). Anti-forensics of a NAD-JPEG Detection Scheme Using Estimation of DC Coefficients. In: Garg, D., Kumar, N., Shyamasundar, R. (eds) Information Systems Security. ICISS 2019. Lecture Notes in Computer Science(), vol 11952. Springer, Cham. https://doi.org/10.1007/978-3-030-36945-3_17
Download citation
DOI: https://doi.org/10.1007/978-3-030-36945-3_17
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-36944-6
Online ISBN: 978-3-030-36945-3
eBook Packages: Computer ScienceComputer Science (R0)