Abstract
Nowadays, protecting digital contents becomes important because it is easy to copy them and hard to distinguish the copy from the original one. As the Internet becomes wider and faster, digital contents are distributed illegally wider and faster than ever. Much research is conducted on preventing illegal distribution and on developing new protection technologies, such as digital watermarking, digital right management, etc. But these technologies are mainly used for commercial and business purposes. Moreover, these technologies are based on the assumption that digital contents will not be modified after being distributed by the contents owner.
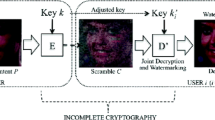
In this paper, we propose a new scheme to protect against the illegal distribution of modifiable digital contents. The proposed scheme also manages modification history and the copyright information of modified digital contents. The proposed scheme assumes that the system is composed of server, client, and application that manages modification history. The application exists in the client side and has a secret key. Any legal user receives encrypted digital contents from the server via this application, but cannot place decrypted contents into storage. If a user has distributed his digital contents and his private key to others, our scheme can determine who has distributed them. We compare our scheme with previous technologies such as simple encryption method, digital watermarking, digital right management, and secure file system, and show that the proposed scheme has better characteristics.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-0-387-35691-4_52
Chapter PDF
Similar content being viewed by others
References
M. D. Swanson, M. Kobayashi and A. H. Tewfik, “Multimedia Data-Embedding and Watermarking Technologies,” Proceedings of the IEEE, Vol. 86, No. 6, JUNE 1998.
J. Brassil, S. Low, N. Maxemchuk, L. O’Gorman, “Electronic Marking and Identification Techniques to Discourage Document Copying,” IEEE J. Select. Areas Commun., vol. 13, pp 1495–1504, Oct 1995.
Http://www.watermarkingworld.org/webring.html
Http://www.microsoft.com/windows/windowsmedia/drm.asp
Http://cryptome.org/ms-drm-os.htm
T. Sander and C. F. Tschudin, “On software protection via function hiding,” Lecture Notes in Computer Science, 1525: 1 1 1–123, 1998.
Boaz Barak, Oded Goldreich, Russell Impagliazzo, Steven Rudich, Amit Sahai, Salil Vadhan, Ke Yang, “On the (1m)possibility of Obfuscating Programs,” * Advances in Cryptology–CRYPTO ‘01, vol. 2139 of Lecture Notes in Computer Science, pp. 1–18, August 19–23, 2001.
Jurgen Reuter, Stefan U. Hngen, James J. Hunt, and Walter F. Tichy, “Distributed Revision Control Via the World Wide Web,” In Proc. Sixth Intl. Workshop on Software Configuration Management, Berlin, Germany, March, 1996.
Ethan Miller, et.al.,“Strong Security for Distributed File Systems,” the 20th International Performance, Computing, and Communications Conference (IPCCC200I).
Microsoft Digital Media Division, “Security Overview of Windows Media Rights Manager,” September 2001.
Matt Blaze, “A Cryptographic File System for Unix,” 1st ACM Conference on Communications and Computing Security, pages 9–16, November 1993.
Jude T.Regan and Christian D. Jensen, “Capability file names: Separating authorization from user management in an internet file system,” In Proceedings of the 10th USENIX Security Symposium, pages 221–233, The USENIX association, August 2001.
A. Bakker, M. van Steen, and A. Tanenbaum, “A Law-Abiding Peer-to-Peer Network for Free-Software Distribution,” In Proc. Intl Symp. Network Computing and Applications, Cambridge, MA, Feb. 2002. IEEE.
Http://www.intertrust.com/main/research/whitepapers/IDCUnderstandingDRMSystems. pdf
C.1. Podilchuk and E.J. Delp, “Digital watermarking: Algorithms and applications,” IEEE Signal Processing Magazine, vol. 18, no. 4, pp. 33–46, July 2001.
F. Hartung and F. Ramme, “Digital Rights Management and Watermarking of Multimedia Contents for M-Commerce Applications,” IEEE Communications Magazine, vol. 38, no. 11, pp. 78–84, Nov. 2000, Invited paper.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2003 IFIP International Federation for Information Processing
About this paper
Cite this paper
Park, H., Kim, J. (2003). PCMHoDC. In: Gritzalis, D., De Capitani di Vimercati, S., Samarati, P., Katsikas, S. (eds) Security and Privacy in the Age of Uncertainty. SEC 2003. IFIP — The International Federation for Information Processing, vol 122. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35691-4_8
Download citation
DOI: https://doi.org/10.1007/978-0-387-35691-4_8
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-4757-6489-5
Online ISBN: 978-0-387-35691-4
eBook Packages: Springer Book Archive