Abstract
This paper shows how the simplified event calculus (SEC) may be used to represent security models for discretionary access control when access rights may be expressed as holding for limited periods of time.
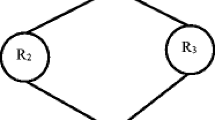
The approach involves formulating a set of axioms to represent a specific security model with time-constrained authorizations. These model-specific axioms are combined with a set of rules which represent the core axiom of the SEC and a set of ground atomic assertions which record a history of security events which affect a database. In this framework, a subject’s request to exercise an access right on a database object is allowed only if authorization can be proved from the axiomatization.
An example security model is presented to demonstrate the approach, extensions to this model are outlined and implementation issues are discussed.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-0-387-35508-5_22
Chapter PDF
Similar content being viewed by others
References
Apt, K., Blair, H., and Walker, A. (1988). Towards a theory of declarative knowledge. Foundations of Deductive Databases and Logic Programming (ed. J. Minker ), Morgan-Kaufmann.
Bertino, E., Bettini, C., Ferrari, E., and Samarati, P. (1996). A temporal access control mechanism for database systems, TKDE, 8 (1).
Clark, K. (1978). Negation as failure. Logic and Databases (eds. H.Gallaire and J. Minker ), Plenum.
Griffiths, P., and Wade, B. (1976). An authorization mechanism for relational database systems. ACM TODS, 1 (3).
Kowalski, R. (1979). Logic for Problem Solving, Elsevier.
Kowalski, R. (1992). Database updates in the event calculus. Journal of Logic Programming, 12.
Kowalski, R. and Sergot, M. (1986). A logic-based calculus of events. New Generation Computing, 4 (1).
LLoyd, J. (1987). Foundations of Logic Programming, Springer-Verlag.
Michie, D. (1968). Memo functions and machine learning. Nature, 218.
Sadri, F. and Kowalski, R. (1995). Variants of the event calculus, Proceedings of ICLP, MIT Press.
Shepherdson, J. (1984). Negation as failure. Journal of Logic Programming, 1.
Shepherdson, J. (1997). Negation as failure, completion and stratification. Handbook of Logic in AI and Logic Programming, Volume 5, Logic Programming (eds. D. Gabbay, et al,Oxford.
Stirling, L. and Shapiro, E. (1994). The Art of PROLOG,MIT Press.
Thomas, R. and Sandhu, R. (1993). Discretionary access control in objected-oriented databases: Issues and research directions. Proceedings of the Sixteenth National Computer Security Conference.
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2000 IFIP International Federation for Information Processing
About this chapter
Cite this chapter
Barker, S. (2000). Temporal Authorization in the Simplified Event Calculus. In: Atluri, V., Hale, J. (eds) Research Advances in Database and Information Systems Security. IFIP — The International Federation for Information Processing, vol 43. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35508-5_18
Download citation
DOI: https://doi.org/10.1007/978-0-387-35508-5_18
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-4757-6411-6
Online ISBN: 978-0-387-35508-5
eBook Packages: Springer Book Archive