Abstract
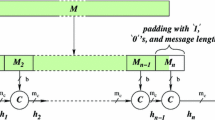
We show that for various choices of the parameters in the SL2(\( \mathbb{F}_{2^n } \)) hashing scheme, suggested by Tillich and Zémor, messages can be modified without changing the hash value. Moreover, examples of hash functions “with a trapdoor” within this family are given. Due to these weaknesses one should impose at least certain restrictions on the allowed parameter values when using the SL2(\( \mathbb{F}_{2^n } \)) hashing scheme for cryptographic purposes.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
K. S. Abdukhalikov and C. Kim, On the Security of the Hashing Scheme Based on SL2, in Fast Software Encryption-FSE’ 98, S. Vaudenay, ed., vol. 1372 of Lecture Notes in Computer Science, Springer, 1998, pp. 93–102.
M. Bellare and D. Micciancio, A New Paradigm for Collision-Free Hashing: Incrementality at Reduced Cost, in Advances in Cryptology-EUROCRYPT’ 97, W. Fumy, ed., vol. 1233 of Lecture Notes in Computer Science, Springer, 1997, pp. 163–192.
C. Charnes and J. Pieprzyk, Attacking the SL2 hashing scheme, in Advances in Cryptology-ASIACRYPT’ 94, J. Pieprzyk and R. Safavi-Naini, eds., vol. 917 of Lecture Notes in Computer Science, Springer, 1995, pp. 322–330.
I. B. Damgård, A Design Principle for Hash Functions, in Advances in Cryptology-CRYPTO’ 89, G. Brassard, ed., vol. 435 of Lecture Notes in Computer Science, Springer, 1989, pp. 416–427.
W. Geiselmann, A Note on the Hash Function of Tillich and Zemor, in Cryptography and Coding, C. Boyd, ed., vol. 1025 of Lecture Notes in Computer Science, Springer, 1995, pp. 257–263.
J. Gutiérrez, T. Recio, and C. Ruiz de Velasco, Polynomial decomposition algorithm of almost quadratic complexity, in Applied Algebra, Algebraic Algorithms and Error-Correcting Codes (AAECC-6), Rome, Italy, 1988, T. Mora, ed., vol. 357 of Lecture Notes in Computer Science, Springer, 1989, pp. 471–475.
B. Huppert, Endliche Gruppen I, vol. 134 of Grundlehren der mathematischen Wissenschaften, Springer, 1967. Zweiter Nachdruck der ersten Auflage.
D. Kozen and S. Landau, Polynomial Decomposition Algorithms, Journal of Symbolic Computation, 7 (1989), pp. 445–456.
B. Preneel, Design principles for dedicated hash functions, in Fast Software Encryption, R. Anderson, ed., vol. 809 of Lecture Notes in Computer Science, Springer, 1994, pp. 71–82.
J.-J. Quisquater and M. Joye, Authentication of sequences with the SL2 hash function: Application to video sequences., Journal of Computer Security, 5 (1997), pp. 213–223.
J.-P. Tillich and G. Zémor, Hashing with SL2, in Advances in Cryptology-CRYPTO’ 94, Y. Desmedt, ed., vol. 839 of Lecture Notes in Computer Science, Springer, 1994, pp. 40–49.
S. Vaudenay, Hidden Collisions on DSS, in Advances in Cryptology-CRYPTO’ 96, N. Koblitz, ed., vol. 1109 of Lecture Notes in Computer Science, Springer, 1996, pp. 83–88.
J. Von zur Gathen, Functional Decomposition of Polynomials: The Tame Case, Journal of Symbolic Computation, 9 (1990), pp. 281–300.
-, Functional Decomposition of Polynomials: The Wild Case, Journal of Symbolic Computation, 10 (1990), pp. 437–452.
G. Zémor, Hash Functions and Graphs With Large Girths, in Advances in Cryptology-EUROCRYPT’ 91, D. W. Davies, ed., vol. 547 of Lecture Notes in Computer Science, Springer, 1991, pp. 508–511.
-, Hash Functions and Cayley Graphs, Designs, Codes and Cryptography, 4 (1994), pp. 381–394.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2000 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Steinwandt, R., Grassl, M., Geiselmann, W., Beth, T. (2000). Weaknesses in the SL2(\( \mathbb{F}_{2^n } \)) Hashing Scheme. In: Bellare, M. (eds) Advances in Cryptology — CRYPTO 2000. CRYPTO 2000. Lecture Notes in Computer Science, vol 1880. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-44598-6_18
Download citation
DOI: https://doi.org/10.1007/3-540-44598-6_18
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-67907-3
Online ISBN: 978-3-540-44598-2
eBook Packages: Springer Book Archive