Abstract
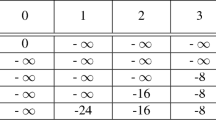
Shin et al. [4] proposed a new hash function with 160-bit output length at PKC’98. Recently, at FSE 2002, Han et al. [5] cryptanalyzed the hash function proposed at PKC’98 and suggested a method finding a collision pair with probability 2-30, supposing that boolean functions satisfy the SAC(Strict Avalanche Criterion). This paper improves their attack and shows that we can find a collision pair from the original version of the hash function with probability 2-37.13 through the improved method. Furthermore we point out a weakness of the function comes from shift values dependent on message.
This work was supported by both Ministry of Information and Communication and Korea Information Security Agency, Korea, under project 2002-130
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
F. Chabaud and A. Joux, Differential Collisions in SHA-0, Advances in CRYPTO’98, LNCS 1462, Springer-Verlag, 1998, pp. 56–71.
H. Dobbertin, Cryptanalysis of MD4, Fast Software Encryption, LNCS 1039, Springer-Verlag,1996, pp. 53–69.
H. Dobbertin, Cryptanalysis of MD5 Compress, May. 1996. http://www-cse.ucsd.edu/users/bsy/dobbertin.ps
Sanguk Shin, Kyunghyune Rhee, Daehyun Ryu, Sangjin Lee, A New Hash Function Based on MDx-family and Its Application to MAC, Public Key Cryptography’98, pp. 234–246. 1998.
Daewan Han, Sangwoo Park, Seongtaek Chee, Cryptanalysis of a Hash Function Proposed at PKC’98, Fast Software Encryption 2002, LNCS 2365, pp. 252–262.
P.R. Kasselman and W.T. Penzhorn, Cryptanalysis of reduced version of HAVAL, Electronics Letters 6th January 2000 Vol.36 No.1, pp. 30–31.
S.W. Park, S.H. Sung, S.T. Chee, J.I. Lim, On the Security of Reduced Versions of 3-Pass HAVAL, ACISP 2002, LNCS 2384, pp. 406–419.
R. Rivest, The MD4 message digest algorithm, RFC 1320, Internet Activities Board, Internet Privacy Task Force, Apr. 1992.
R. Rivest, The MD5 message digest algorithm, RFC 1321, Internet Activities Board, Internet Privacy Task Force, Apr. 1992.
Y. Zheng, J. Pieprzyk and J. Sebberry, HAVAL-A one-way hashing algorithm with variable length of output, Advances in Cryptology-Auscrypt’92, LNCS 718, Springer-Verlag, 1993, pp. 83–104.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2003 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Chang, D., Sung, J., Sung, S., Lee, S., Lim, J. (2003). Full-Round Differential Attack on the Original Version of the Hash Function Proposed at PKC’98. In: Nyberg, K., Heys, H. (eds) Selected Areas in Cryptography. SAC 2002. Lecture Notes in Computer Science, vol 2595. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-36492-7_12
Download citation
DOI: https://doi.org/10.1007/3-540-36492-7_12
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-00622-0
Online ISBN: 978-3-540-36492-4
eBook Packages: Springer Book Archive