Summary
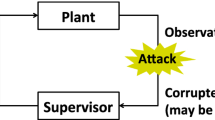
This chapter models the execution of a software process as a discrete event system that can be represented by a Deterministic Finite State Automaton (DFSA) in the discrete event setting. Supervisory Control Theory (SCT) is applied for on-line detection of malicious executables and prevention of their spreading. The language measure theory, described in Chapter 1, is adapted for performance evaluation and comparison of the unsupervised process automaton and five different supervised process automata. Simulation experiments under different scenarios show the rate of correct detection of malicious executables to be 88.75%.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
S. T. Eckmann, G. Vigna, and R.A. Kemmerer, Statl: An attack language for state-based intrusion detection, Proceedings of the ACM workshop on Intrusion Detection (Athens, Greece), November 2000.
E. Eskin and W. Lee, Modeling system calls for intrusion detection with dynamic window sizes, Proceedings of DISCEX II, 2001.
S. Forrest, S. A. Hofmeyr, and A. Somayaji, Intrusion detection using system calls, Journal of computer society 6 (1998), no. 3, 151–180.
S. Forrest, S. A. Hofmeyr, A. Somayaji, and T. A. Longstaff, A sense of self for unix processes, Proceedings of the 1996 IEEE Symposium on Security and Privacy, 1996, pp. 120–128.
S. Forrest, A.S. Perlelson, L. Allen, and R. Cherukuri, Self-noneself discrimination in a computer, Proceedings of IEEE Symposium on research in Security and Privacy, 1994.
S. Forrest, C. Warrender, and B. Pearlmutter, Detecting intrusion using system calls: Alternative data models, Proceedings of the 1999 IEEE Symposium on Security and Privacy, 1999, pp. 133–145.
A.K. Ghosh, A. Schwartzbard, and M. Schatz, Learning program behavior profiles for intrusion detection, Proceedings of the 1st USENIX Workshop on Intrusion Detection and Networking Monitoring, 1999.
K. Goseva-Popstojanova, F. Wang, R. Wang, F. Gong, K. Vaidyanathan, K. Trivedi, and B. Muthusamy, Characterizing intrusion tolerant systems using a state transition model, Proceedings of DARPA Information Survivability Conference and Exposition II (DISCEX’01), 2001.
K. Ilgun, Ustat: A real time intrusion detection system for unix, Proceedings of the 1993 IEEE Symposium on Research in Security and Privacy, 1993.
K. Ilgun, R. A. Kemmerer, and P. A. Porras, State transition analysis: a rule-based intrusion detection approach, IEEE Transactions on software engineering 21 (1995), no. 3.
G. Karsai and A. Ledeczi, An approach to self adaptive software based on supervisory control, IWSAS 2001 (Balatonfured, Hungary), 2001.
J.O. Kephart and S.R. White, How prevalent are computer viruses, High Integrity Computing Laboratory, http://www.research.ibm.com/antivirus/SciPapers/Kephart/DPMA92/dpma92.html.
R. Kumar and M. Fabian, Supervisory control of partial specification arising in protocol conversion, 35th Allerton Conference on Communication, Control and computing (Urbana-Champaign, Illinois), 1997, pp. 543–552.
S. Kumar and E. H. Spafford, A generic virus scanner in C++, Proceedings of the 8th Computer Security Applications Conference, IEEE press, 1992.
B. LeCharlier and M. Swimmer, Dynamic detection and classification of computer viruses using general behavior patterns, Proceedings of Fifth International Virus Bulletin Conference, September 20–22 1995, p. 75.
W. Lee and S.J. Stolfo, Data mining approaches for intrusion detection, Proceedings of the Seventh USENIX Security Symposium (SECURITY’ 98) (San Antonio, TX), January 1998.
R.B. Levin, The computer virus handbook, Osbrne McGraw-Hill, 1990, ISBN 0-07-881047-5.
C.C. Michael and A. Ghosh, Using finite automata to mine execution data for intrusion detection: a preliminary report, Proc. RAID 2000, 2000, pp. 133–145.
N. Nuansri, S. Singh, and T.S. Dillon, A process state-transition analysis and its application to intrusion detection, AC-SAC 1999, 1999, pp. 378–388.
Y. Okazaki, I. Sato, and S. Goto, A new intrusion detection method based on process profiling, Proceedings of the 2002 Symposium on Applications and the Internet (SAINT) (Nara City, Nara, Japan), Jan 28–Feb 01 2002.
V. Phoha, X. Xu, A. Ray, and S. Phoha, Supervisory control automata paradigm to make malicious executables ineffectual, Proceedings of the 5th IFAC Symposium on Fault Detection, Supervision and Safety (Washington, D.C), June 2003.
P.J. Ramadge and W.M. Wonham, Supervisory control of a class of discrete event processes, SIAM J. Control and Optimization 25 (1987), no. 1, 206–230.
M. G. Schultz, E. Eskin, E. Zadok, and S.J. Stolfo, Data mining methods for detection of new malicious executables, Proceedings of IEEE Symposium on Security and Privacy (Oakland, CA), May 2001.
A. Solomon and T. Kay, Dr. Solomon’s pc anti-virus book, Newtech, 1994, ISBN 0750616148.
E.H. Spafford, Computer viruses as artificial life, Journal of Artificial life 1 (1994), no. 3, 249–265.
D. Spinellis, Trace: A tool for logging operating system call transactions, Operating Systems Review 28 (1994), no. 4, 56–63.
A. Surana and A. Ray, Signed real measure of regular languages, Demonstratio Mathematica 37 (2004), no. 2, 485–503.
C. Wallace, P. Jensen, and N. Soparkar, Supervisory control of workflow scheduling, Proceedings of International Workshop on Advanced Transaction Models and Architectures (Goa), August–September 1996.
X. Wang and A. Ray, A language measure for performance evaluation of discrete-event supervisory control systems, Applied Mathematical Modelling 28 (2004), no. 9, 817–833.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer Science+Business Media, Inc.
About this chapter
Cite this chapter
Xu, X., Phoha, V.V., Ray, A., Phoha, S. (2005). Supervisory Control of Malicious Executables in Software Processes. In: Ray, A., Phoha, V.V., Phoha, S.P. (eds) Quantitative Measure for Discrete Event Supervisory Control. Springer, New York, NY. https://doi.org/10.1007/0-387-23903-0_9
Download citation
DOI: https://doi.org/10.1007/0-387-23903-0_9
Publisher Name: Springer, New York, NY
Print ISBN: 978-0-387-02108-9
Online ISBN: 978-0-387-23903-3
eBook Packages: Computer ScienceComputer Science (R0)