Abstract
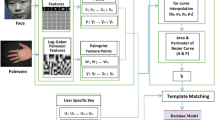
In this paper we report an approach for cryptographic key generation based on keystroke dynamics and the k-medoids algorithm. The stages that comprise the approach are training-enrollment and user verification. The proposed approach is able to verify the identity of individuals off-line avoiding the use of a centralized database. The performance of the proposed approach is assessed using 20 samples of keystroke dynamics from 20 different users. Simulation results show a false acceptance rate (FAR) of 5.26% and a false rejection rate (FRR) of 10%. The cryptographic key released by the proposed approach may be used in several encryption algorithms.
Chapter PDF
Similar content being viewed by others
References
Clancy, T.C., Kiyavash, N., Lin, D.J.: Secure smart card-based fingerprint authentication. In: Proceedings of the 2003 ACM SIGMM Workshop of Biometrics Methods and Application (2003)
Goh, A., Ngo, D.C.L.: Computation of cryptographic keys from face biometrics. In: Lioy, A., Mazzocchi, D. (eds.) CMS 2003. LNCS, vol. 2828, pp. 1–13. Springer, Heidelberg (2003)
Hao, F., Anderson, R., Daugman, J.: Combining Cryptography with Biometrics Effectively, Computer Laboratory, University of Cambridge, Technical Report Number 640 (2005)
Hao, F., Chan, C.W.: Private key generation from on-line handwritten signatures. Information Management & Computer Society 10(4) (2002)
Zhang, Q., Couloigner, I.: A New and Efficient K-Medoid Algorithm for Spatial Clustering. In: Gervasi, O., Gavrilova, M.L., Kumar, V., Laganá, A., Lee, H.P., Mun, Y., Taniar, D., Tan, C.J.K. (eds.) ICCSA 2005. LNCS, vol. 3482, pp. 181–189. Springer, Heidelberg (2005)
Barioni, M.C.N., Razente, H., Traina, A.J.M., Traina Jr., C.: Accelerating k-medoid-based algorithms through metric access methods. Journal of Systems and Software 81(3), 343–355 (2008)
Kardi, T.: Minkowski Distance of order λ (2009), http://people.revoledu.com/kardi/tutorial/Similarity/MinkowskiDistance.html
Garcia-Baleon, H.A., Alarcon-Aquino, V.: Cryptographic Key Generation from Biometric Data Using Wavelets. In: Proceedings of the IEEE Electronics, Robotics and Automotive Mechanics Conference, CERMA 2009 (September 2009)
Garcia-Baleon, H.A., Alarcon-Aquino, V., Ramirez-Cruz, J.F.: Bimodal Biometric System for Cryptographic Key Generation Using Wavelet Transforms. In: Proceedings of the IEEE Mexican International Conference on Computer Science, ENC 2009 (September 2009)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Garcia-Baleon, H.A., Alarcon-Aquino, V., Starostenko, O. (2009). K-Medoids-Based Random Biometric Pattern for Cryptographic Key Generation. In: Bayro-Corrochano, E., Eklundh, JO. (eds) Progress in Pattern Recognition, Image Analysis, Computer Vision, and Applications. CIARP 2009. Lecture Notes in Computer Science, vol 5856. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-10268-4_10
Download citation
DOI: https://doi.org/10.1007/978-3-642-10268-4_10
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-10267-7
Online ISBN: 978-3-642-10268-4
eBook Packages: Computer ScienceComputer Science (R0)