Abstract
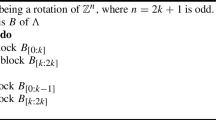
Lattice reduction is a hard problem of interest to both public-key cryptography and cryptanalysis. Despite its importance, extremely few algorithms are known. The best algorithm known in high dimension is due to Schnorr, proposed in 1987 as a block generalization of the famous LLL algorithm. This paper deals with Schnorr’s algorithm and potential improvements. We prove that Schnorr’s algorithm outputs better bases than what was previously known: namely, we decrease all former bounds on Schnorr’s approximation factors to their (ln 2)-th power. On the other hand, we also show that the output quality may have intrinsic limitations, even if an improved reduction strategy was used for each block, thereby strengthening recent results by Ajtai. This is done by making a connection between Schnorr’s algorithm and a mathematical constant introduced by Rankin more than 50 years ago as a generalization of Hermite’s constant. Rankin’s constant leads us to introduce the so-called smallest volume problem, a new lattice problem which generalizes the shortest vector problem, and which has applications to blockwise lattice reduction generalizing LLL and Schnorr’s algorithm, possibly improving their output quality. Schnorr’s algorithm is actually based on an approximation algorithm for the smallest volume problem in low dimension. We obtain a slight improvement over Schnorr’s algorithm by presenting a cheaper approximation algorithm for the smallest volume problem, which we call transference reduction.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Ajtai, M.: The worst-case behavior of Schnorr’s algorithm approximating the shortest nonzero vector in a lattice. In: Proceedings of the Thirty-Fifth Annual ACM Symposium on Theory of Computing (electronic), pp. 396–406. ACM Press, New York (2003)
Ajtai, M., Kumar, R., Sivakumar, D.: A sieve algorithm for the shortest lattice vector problem. In: Proc. 33rd STOC, pp. 601–610. ACM Press, New York (2001)
Boguslavsky, M.I.: Radon transforms and packings. Discrete Appl. Math. 111(1-2), 3–22 (2001)
Boneh, D.: Twenty years of attacks on the RSA cryptosystem. Notices of the AMS 46(2), 203–213 (1999)
Boneh, D., Durfee, G.: Cryptanalysis of RSA with private key d less than N 0.292. In: Stern, J. (ed.) EUROCRYPT 1999. LNCS, vol. 1592, pp. 1–11. Springer, Heidelberg (1999)
Cassels, J.W.S.: Rational quadratic forms. London Mathematical Society Monographs, vol. 13. Academic Press Inc. [Harcourt Brace Jovanovich Publishers], London (1978)
Cohen, H.: A Course in Computational Algebraic Number Theory, 2nd edn. Springer, Heidelberg (1995)
Conway, J., Sloane, N.: Sphere Packings, Lattices and Groups, 3rd edn. Springer, Heidelberg (1998)
Coppersmith, D.: Small solutions to polynomial equations, and low exponent RSA vulnerabilities. J. of Cryptology 10(4), 233–260 (1997)
Grötschel, M., Lovász, L., Schrijver, A.: Geometric algorithms and combinatorial optimization. In: Algorithms and Combinatorics: Study and Research Texts, vol. 2. Springer, Berlin (1988)
Hermite, C.: Extraits de lettres de M. Hermite à M. Jacobi sur différents objets de la théorie des nombres, deuxième lettre. J. Reine Angew. Math. 40, 279–290 (1850) (Also available in the first volume of Hermite’s complete works, published by Gauthier-Villars)
Howgrave-Graham, N.A., Smart, N.P.: Lattice attacks on digital signature schemes. Des. Codes Cryptogr. 23(3), 283–290 (2001)
Lagrange, J.L.: Recherches d’arithmétique, Nouveaux Mémoires de l’Académie de, Berlin, vol. 1773
Lenstra, A.K., Lenstra Jr., H.W., Lovász, L.: Factoring polynomials with rational coefficients. Mathematische Ann. 261, 513–534 (1982)
Lovász, L.: An Algorithmic Theory of Numbers, Graphs and Convexity. CBMS-NSF Regional Conference Series in Applied Mathematics, vol. 50. SIAM Publications, Philadelphia (1986)
Martinet, J.: Les réseaux parfaits des espaces euclidiens. Masson, Paris (1996)
Micciancio, D., Goldwasser, S.: Complexity of lattice problems. The Kluwer International Series in Engineering and Computer Science, vol. 671. Kluwer Academic Publishers, Boston (2002) (A cryptographic perspective)
Milnor, J., Husemoller, D.: Symmetric bilinear forms. Math. Z (1973)
Nguyen, P.Q., Shparlinski, I.E.: The insecurity of the digital signature algorithm with partially known nonces. J. Cryptology 15(3), 151–176 (2002)
Nguên, P.Q., Stehlé, D.: Floating-point LLL revisited. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 215–233. Springer, Heidelberg (2005)
Nguyên, P.Q., Stern, J.: The two faces of lattices in cryptology. In: Silverman, J.H. (ed.) CaLC 2001. LNCS, vol. 2146, p. 146. Springer, Heidelberg (2001)
Odlyzko, A.M.: The rise and fall of knapsack cryptosystems. In: Proc. of Cryptology and Computational Number Theory. Proc. of Symposia in Applied Mathematics, vol. 42, pp. 75–88. AMA (1989)
Rankin, R.A.: On positive definite quadratic forms. J. London Math. Soc. 28, 309–314 (1953)
Schnorr, C.P.: A hierarchy of polynomial lattice basis reduction algorithms. Theoretical Computer Science 53, 201–224 (1987)
Schnorr, C.P.: A more efficient algorithm for lattice basis reduction. J. of algorithms 9(1), 47–62 (1988)
Schnorr, C.P., Euchner, M.: Lattice basis reduction: improved practical algorithms and solving subset sum problems. Math. Programming 66, 181–199 (1994)
Schnorr, C.-P., Hörner, H.H.: Attacking the chor-rivest cryptosystem by improved lattice reduction. In: Guillou, L.C., Quisquater, J.-J. (eds.) EUROCRYPT 1995. LNCS, vol. 921, pp. 1–12. Springer, Heidelberg (1995)
Thunder, J.L.: Higher-dimensional analogs of Hermite’s constant. Michigan Math. J. 45(2), 301–314 (1998)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Gama, N., Howgrave-Graham, N., Koy, H., Nguyen, P.Q. (2006). Rankin’s Constant and Blockwise Lattice Reduction. In: Dwork, C. (eds) Advances in Cryptology - CRYPTO 2006. CRYPTO 2006. Lecture Notes in Computer Science, vol 4117. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11818175_7
Download citation
DOI: https://doi.org/10.1007/11818175_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-37432-9
Online ISBN: 978-3-540-37433-6
eBook Packages: Computer ScienceComputer Science (R0)