Abstract
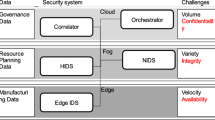
In this paper, authors describe the ain features of the Internet of Things, and potential security threats caused by these features. Authors propose an approach to the detection of incidents in the Internet of Things, based on a correlation analysis of data from the devices of the Internet of Things.
Similar content being viewed by others
References
EU FP7 Project CASAGRAS, “CASAGRAS Final Report: RFID and the Inclusive Model for the Internet of Things,” 2009, pp. 10–12.
Bryant, B., dA Method for Implementing Intention-Based Attack Ontologies with SIEM Software, 2014.
Goel, S. and Chen, V., Information security risk analysis–A matrix-based approach, Proceedings of the Information Resource Management Association (IRMA), International Conference, Information Resources Management Association, Hershey, PA, 2005.
Lee, J.-K. and Im, C.-T., Correlation Analysis of Cyber Threat Information in Heterogeneous Security Systems. Applied Security Technology Team, Korea Internet and Security Agency, 2013.
Zhaojun, G. and Yong, L., Research of security event correlation based on attribute similarity, IC3T'12, Proceedings of the 2012 International Conference on Convergence Computer Technology, 2012, pp. 110–113.
Jiang, G. and Cybenko, G., Temporal and Spatial Distributed Event Correlation for Network Security, Proceedings of the American Control Conference, 2004, vol. 2, pp. 996–1001.
Zheng, Z., Wang, J., and Zhu, Z., A general anomaly detection framework for Internet of Things, Proc. 41st IEEE/IFIP International Conference on Dependable Systems and Networks (DSN'11), Hong Kong, 2011.
Jie, X., Hongjun, B., and Yun, L., Research on security threat assessment method based on the attack tree model of the Internet of Things, JCIT, 2013, vol. 8, no. 3, pp. 653–658.
Event correlation: Move from search to operational intelligence, whitepaper.
Dong, C., Xiuquan, Q., et al., Mining data correlation from multi-faceted sensor data in the Internet of Things, China Commun., 2011, vol. 8, no. 1, pp. 132–138.
Mietz, R. and Romer, K., Exploiting Correlations for Efficient Content-based Sensor Search, IEEE Sensors, 2011, pp. 187–190.
Chatzigiannakis, I., Hasemann, H., Karnstedt, M., and Kleine, O., True self-configuration for the IoT, 3rd International Conference on the Internet of Things (IOT), 2012, pp. 135–142.
Shafagh, H. and Hithnawi, A., Poster: Come closer–proximity-based authentication for the Internet of Things, MobiCom, 2014.
Baneriee, O., Ghaoui, L.E., and D’aspremont, A., Model selection through sparse maximum likelihood estimation for multivariate Gaussian or binary data [J], J. Mach. Learn. Res., 2008, vol. 9, no. 3, pp. 485–516.
Amizadeh, S. and Hauskrecht, M., Latent variable model for learning in pairwise Markov networks [C], Proceedings of the 24th AAAI Conference on Artificial Intelligence, Atlanta, GA; Menlo Park, CA; 2010, pp. 382–387.
Friedman, J., Hastie, T., and Tibshirani, R., Sparse inverse covariance estimation with the graphical lasso, Biostatistics, 2008, vol. 9, no. 3, pp. 432–441.
Author information
Authors and Affiliations
Corresponding author
Additional information
The article is published in the original.
About this article
Cite this article
Lavrova, D., Pechenkin, A. & Gluhov, V. Applying correlation analysis methods to control flow violation detection in the internet of things. Aut. Control Comp. Sci. 49, 735–740 (2015). https://doi.org/10.3103/S0146411615080283
Received:
Published:
Issue Date:
DOI: https://doi.org/10.3103/S0146411615080283