Abstract
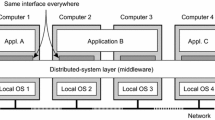
Database Security and Protection System (DSPS) is a security platform for fighting malicious DBMS. The security and performance are critical to DSPS. The authors suggested a key management scheme by combining the server group structure to improve availability and the key distribution structure needed by proactive security. This paper detailed the implementation of proactive security in DSPS. After thorough performance analysis, the authors concluded that the performance difference between the replicated mechanism and proactive mechanism becomes smaller and smaller with increasing number of concurrent connections; and that proactive security is very useful and practical for large, critical applications.
Similar content being viewed by others
References
Barak, B., Herzberg, A., Naor, D. and Shai, E., 1999. The proactivesecurity toolkit and applications. Proceedings of the ACM Conference on Computer and Communications Security, ACM, Singapore, p.18–27.
Cai, L., Yang, X. H. and Dong, J.X., 2002a. Database, securityin information warfare—special requirements and antagonism in China.Journal of Computer Research and Development,39(5): 568–573 (in Chinese).
Cai, L., Yang, X. H. and Dong, J. X., 2002b. A referencemodel for database security proxy.Journal of Zhejiang University SCIENCE,3(1): 30–36.
Canetti, R., Gennaro, R., Herzberg, A. and Naor, D., 1997. Proactivesecurity: long-term protection against break-ins.CryptoBytes: the technical newsletter of RSA Labs,3(1): 1–8.
Malkin, M., Wu, T. and Boneh, D., 1999. Experimenting withshared generation of RSA keys. Proceedings of the Internet Society's Symposium on Network and Distributed System Security. IEEE Computer Society Press, California, p.43–56.
Malkin, M., Wu, T. and Boneh, D., 2000. Building intrusion tolerant applications. Proceedings of DARPA Information Survivability Conference & Exposition (DISCEX), IEEE Computer Society Press, California, p. 74–87.
Meiter, M., Franklin, M., Lacy, J. and Wright, R., 1996. The Ω keymanagement service. Proceedings of the ACM Conference on Computer and Communications Security, ACM, New Delphi, India, p.38–47.
Author information
Authors and Affiliations
Corresponding author
Additional information
Project (No. 45.6.1-017) supported by the National Defense Pre-Research Fund of China
Rights and permissions
About this article
Cite this article
Cai, L., Yang, Xh. & Dong, Jx. Building a highly available and intrusion tolerant database security and protection system (DSPS). J. Zhejiang Univ. Sci. A 4, 287–293 (2003). https://doi.org/10.1631/jzus.2003.0287
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1631/jzus.2003.0287
Key words
- Information warfare
- Proactive security
- Intrusion tolerant
- DSPS (Database Security and Protection System)