Abstract
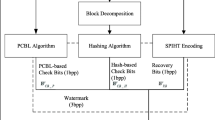
Watermarking is a means of implanting data in the form of text, symbols or any credential into the multimedia data such as image, audio or video. The conventional produces below-par accomplishment when the communication is implanted into the image LSB bits. With a view to rectify these defects and also to safeguard the confidential data and images from the bogus clients, we are introducing an innovative method. In the proposed method, we employ. Adaptive quin tree decomposition for fragmenting the original image into five blocks, and the signed communication from the ECC technique are implanted into the fifth block pixel values. Subsequently, the data revival and authentication procedure are done to check the authenticity or otherwise of the data and image revived. A group of data including images is employed to assess the efficiency of our innovative approach and amazing outcomes achieved from the novel approach that predict the robustness of the suggested decomposition method in image verification procedure. The performance outcomes also validate the proficiency of the proposed program for the confirmation of the image by means of watermarking. It has gone a long way in attaining progress in image certification, safety and security measures. Further, the efficiency of the novel system is put to test and contrasted with the outcomes of the current watermarking technique.
Similar content being viewed by others
References
M. Soliman, A. E. Hassanien, N. Ghali, and H. Onsi, “An adaptive watermarking approach for medical imaging using swarm intelligent,” Int. J. Smart Home 6 (1), 37–50 (2012).
N. Pandey, Sayani Nandy, and Shelly Sinha Choudhury, “Alternative shift algorithm for digital watermarking on text,” Int. J. Sci. Res. Publ. 2 (10), 1–5 (2012).
Sudhanshu Gonge and Jagdish Bakal, “Robust digital watermarking technique by using DCT and spread spectrum,” Int. J. Electr., Electron. Data Commun. 1 (2), 27–32 (2013).
J. Pragya and A. S. Rajawat, “Fragile watermarking for image authentication: survey,” Int. J. Electron. Comput. Sci. Eng. 1 (3), 1232–1237 (2012).
S. S. Sujatha and M. Mohamed Sathik, “A novel DWT based blind watermarking for image authentication,” Int. J. Network Security 14 (4), 223–228 (2012).
N. Yassin, N. Salem, and M. Adawy, “Block based video watermarking scheme using wavelet transform and principle component analysis,” Int. J. Comput. Sci. Issues 9 (3), 296–301 (2012).
N. Kashyap and G. R. Sinha, “Image watermarking using 3-level Discrete Wavelet Transform (DWT),” Int. J. Modern Edu. Comput. Sci. 4 (3), 50–56 (2012).
A. A. Hood and N. J. Janwe, “Robust video watermarking techniques and attacks on watermark. A review,” Int. J. Comput. Trends Technol. 4 (1), 30–34 (2013).
K. Goenka and Pallavi Patil, “Overview of audio watermarking techniques,” Int. J. Emerging Technol. Adv. Eng. 2 (2), 67–70 (2012).
Sajjad Dadkhah, Azizah Abd Manaf, and Somayeh Sadeghi, “Efficient digital image authentication and tamper localization technique using 3LSB watermarking,” Int. J. Comput. Sci. Issues 9 (2), 1–8 (2012).
Bhupendra Ram, “Digital image watermarking technique using discrete wavelet transform and discrete cosine transform,” Int. J. Adv. Res. Technol. 2 (4), 19–27 (2013).
Dayalin Leena and Selva Dhayanithy, “Robust image watermarking in frequency domain,” Int. J. Innov. Appl. Studies 2 (4), 582–587 (2013).
Nidhi Bisla and Prachi Chaudhary, “Comparative study of DWT and DWT–SVD image watermarking techniques,” Int. J. Adv. Res. Comput. Sci. Software Eng. 3 (6), 821–825 (2013).
P. M. Pithiya and H. L. Desai, “DCT based digital image watermarking, de-watermarking authentication,” Int. J. Latest Trends Eng. Technol. 2 (3), 213–219 (2013).
S. Radharani and M. L. Valarmathi, “A study on watermarking schemes for image authentication,” Int. J. Comput. Appl. 2 (4), 24–32 (2012).
Navneet Singh, Sonika Matele, and Shailendra Singh, “An efficient approach for security of cloud using watermarking technique,” Int. J. Adv. Res. Comput. Commun. Eng. 2 (7), 2814–2817 (2013).
Barun Pandhwal and D. S. Chaudhari, “An overview of digital watermarking techniques,” Int. J. Soft Comput. Eng. 3 (1), 416–420 (2013).
Megha Kansal, Sukhjeet Ranade, and Amandeep Kaur, “Fragile watermarking for image authentication using a hierarchical mechanism,” Int. J. Eng. Res. Appl. 2 (4), 1759–1763 (2012).
Prabhishek Singh and R. S. Chadha, “A survey of digital watermarking techniques, applications and attacks,” Int. J. Eng. Innov. Techn. 2 (9), 165–175 (2013).
Archana Tiwari and Manisha Sharma, “Semi fragile watermarking schemes for image authentication. A survey,” Int. J. Comput. Network Inf. Security 4 (2), 43–49 (2012).
Wang Xiang-Yang, Miao E-No, “A new SVM-based image watermarking using Gaussian-Hermite moments,” Appl. Soft Comput. 12 (2), 887–903 (2012).
M. Farfoura, Shi-Jinn Horng, Jui-Lin Lai, Ray-Shine Run, Rong-Jian Chen, and M. K. Khan, “A blind reversible method for watermarking relational databases based on a time-stamping protocol,” Expert Syst. Appl. 39 (3), 3185–3196 (2012).
Sanjay Rawat and Balasubramanian Raman, “A publicly verifiable lossless watermarking scheme for copyright protection and ownership assertion,” Int. J. Electron. Commun. 66 (11), 955–962 (2012).
M. Kamran, A. Khan, and Sana Ambreen Malik, “A high capacity reversible watermarking approach for authenticating images: exploiting down-sampling, histogram processing, and block selection,” Int. J. Inf. Sci. 256, 162–183 (2013).
Guangyong Gao and Guoping Jiang, “A lossless copyright authentication scheme based on Bessel-Fourier moment and extreme learning machine in curvaturefeature domain,” J. Syst. Software 86 (1), 222–232 (2013).
Arathi Chitla and M. C. Mohan, “Authentication of images through Lossless Watermarking (LWM) technique with the aid of Elliptic Curve Cryptography (ECC),” Int. J. Comput. Appl. 57 (6), 17–25 (2012).
M. Utku Celik, G. Sharma, and M. Tekalp, “Lossless watermarking for image authentication: a new framework and an implementation,” IEEE Trans. Image Processing 15 (4), 1042–1049 (2006)
V. Padmanabha Reddy and S. Varadarajan, “Human visual system sentient imperceptible and efficient wavelet-based watermarking scheme for copyright protection of digital images,” Int. J. Comput. Sci. Network Security 9 (4), 255–264 (2009).
Author information
Authors and Affiliations
Corresponding author
Additional information
The article is published in the original.
Arathi Chitla, Associate Professor of Computer Science and Engineering in Telangana University, Nizamabad, Telangana, India, she has 14 years of teaching experience. She completed her B.E from Osmania University and M. Tech from JNTU Kakinada with distinction. She is pursuing her Ph. D from JNTU Hyderabad on Digital Watermarking Techniques. She published 10 research articles in international journals and attended national and international seminars and workshops. She organized national seminar with APSCHE.
M. Chandra Mohan, Professor of computer Science and Engineering in JNTUH, Hyderabad, Telangana, India. He is having 7 years of industrial experience and 13 years of teaching experience. He completed his B.E, M.Tech from Osmania University with distinction, Ph.D from JNTU, Hyderabad. He published 15 research articles in International Journals and presented several papers in national and international seminars and workshops. His areas of interests are software engineering and image processing.
Rights and permissions
About this article
Cite this article
Chitla, A., Mohan, M.C. An adaptive quin tree decomposition (AQTD) technique in image authentication through Lossless Watermarking (LWM). Pattern Recognit. Image Anal. 26, 69–81 (2016). https://doi.org/10.1134/S1054661815040045
Received:
Published:
Issue Date:
DOI: https://doi.org/10.1134/S1054661815040045