Abstract
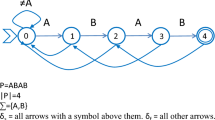
Recursive constructions for covering arrays employ small ingredient covering arrays to build large ones. At present the most effective methods are ‘cut-and-paste’ (or Roux-type) and column replacement techniques. Both can introduce substantial duplication of coverage; if unnecessary duplication can be avoided, then the recursion can yield a smaller array. Two extensions of covering arrays are introduced here for that purpose. The first examines arrays that cover only certain of the t-way interactions; we call these quilting arrays. We develop constructions of such arrays, and generalize column replacement techniques to use them in the construction of covering arrays. The second examines some consequences of nesting covering arrays of smaller strength in those of larger strength; the intersections among the covering arrays so nested lead to improvements in Roux-type constructions. For both directions, we examine consequences for the existence of covering arrays.
Similar content being viewed by others
References
Alon, N. 1986. Explicit construction of exponential sized families of k-independent sets. Discrete Math., 58, 191–193.
Barwick, S. G., and W. A. Jackson. 2007. A sequence approach to linear perfect hash families. Des. Codes Cryptogr., 45, 95–121.
Barwick, S. G., and W. A. Jackson. 2008. Geometric constructions of optimal linear perfect hash families. Finite Fields Appl., 14, 1–13.
Barwick, S. G., W. A. Jackson, and C. T. Quinn. 2004. Optimal linear perfect hash families with small parameters. J. Combin. Des., 12, 311–324.
Blackburn, S. R. 2000. Perfect hash families: probabilistic methods and explicit constructions. J. Combin. Theory (A), 92, 54–60.
Blackburn, S. R., and P. R. Wild. 1998. Optimal linear perfect hash families. J. Combin. Theory (A), 83, 233–250.
Bryce R.C., Colbourn C.J., 2009. A density-based greedy algorithm for higher strength covering arrays. Software Testing, Verification, and Reliability, 19, 37–53.
Chateauneuf, M. A., and D. L. Kreher. 2002. On the state of strength-three covering arrays. J. Combin. Des., 10, 217–238.
Cohen, D. M., S. R. Dalal, M. L. Fredman, and G. C. Patton. 1997. The AETG system: An approach to testing based on combinatorial design. IEEE Trans. Software Eng., 23, 437–44.
Cohen, M. B., C. J. Colbourn, and A. C. H. Ling. 2008. Constructing strength three covering arrays with augmented annealing. Discrete Math., 308, 2709–2722.
Colbourn, C. J. 2004. Combinatorial aspects of covering arrays. Le Matematiche (Catania), 58, 121–167.
Colbourn, C. J. 2009a. Covering array tables. http://www.public.asu.edu/~ccolbou/src/tabby.
Colbourn, C. J. 2009b. Distributing hash families and covering arrays. J. Combin. Inform. Syst. Sci., 34, 113–126.
Colbourn, C. J., G. Kéri, P. P. Rivas Soriano, and J. C. Schlage-Puchta. 2010. Covering and radiuscovering arrays: Constructions and classification. Discrete Appl. Math., 158, 1158–1190.
Colbourn, C. J., and A. C. H. Ling. 2009a. Linear hash families and forbidden configurations. Des. Codes Cryptogr., 59, 25–55.
Colbourn, C. J., and A. C. H. Ling. 2009b. A recursive construction for perfect hash families. J. Math. Crypt., 3, 291–306.
Colbourn, C. J., S. S. Martirosyan, G. L. Mullen, D. E. Shasha, G. B. Sherwood, and J. L. Yucas. 2006a. Products of mixed covering arrays of strength two. J. Combin. Des., 14, 124–138.
Colbourn, C. J., S. S. Martirosyan, Tran Van Trung, and R. A. Walker, II. 2006b. Roux-type constructions for covering arrays of strengths three and four. Des. Codes Cryptogr., 41, 33–57.
Colbourn, C. J., and J. Torres-Jiménez. 2010. Heterogeneous hash families and covering arrays. Contemp. Math., 523, 3–15.
Dinitz, J. H., A. C. H. Ling, and D. R. Stinson. 2007. Perfect hash families from transversal designs. Austr. J. Combin., 37, 233–242.
Hartman A. 2005. Software and hardware testing using combinatorial covering suites. In Interdisciplinary applications of graph theory, combinatorics, and algorithms, ed. M. C. Golumbic and I. B. A. Hartman, 237–266. Norwell, MA, Springer.
Hartman, A., and L. Raskin. 2004. Problems and algorithms for covering arrays. Discrete Math., 284, 149–156.
Martirosyan, S. S., and C. J. Colbourn. 2005. Recursive constructions for covering arrays. Bayreuther Math. Schriften, 74, 266–275.
Martirosyan, S. S., and Tran Van Trung. 2004. On t-covering arrays. Des. Codes Cryptogr., 32, 323–339.
Martirosyan, S. S., and Tran Van Trung. 2008. Explicit constructions for perfect hash families. Des. Codes Cryptogr., 46, 97–112.
Nayeri, P., C. J. Colbourn, and G. Konjevod. 2009. Randomized postoptimization of covering arrays. Lecture Notes Comput. Sci., 5874, 408–419.
Roux, G. 1987. k-Propriétés dans les tableaux de n colonnes: cas particulier de la k-surjectivité et de la k-permutivité. Ph.D. thesis; Université de Paris, Paris, France.
Tang, D. T., and C. L. Chen. 1984. Iterative exhaustive pattern generation for logic testing. IBM J. Res. Dev., 28(2), 212–219.
Torres-Jimenez, J. 2009. Covering array tables. http://www.tamps.cinvestav.mx/~jtj/.
Turán, P. 1941. Eine Extremalaufgabe aus der Graphentheorie. Mat. Fiz. Lapok, 48, 436–452.
Walker, R. A., II, and C. J. Colbourn. 2007. Perfect hash families: Constructions and existence. J. Math. Crypt., 1, 125–150.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Colbourn, C.J., Zhou, J. Improving Two Recursive Constructions for Covering Arrays. J Stat Theory Pract 6, 30–47 (2012). https://doi.org/10.1080/15598608.2012.647489
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1080/15598608.2012.647489