Abstract
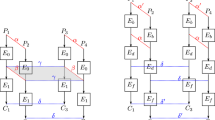
We propose a new attack on Feistel ciphers with a non-surjective round function such as the CAST cipher family and LOKI91. We extend the attack towards block ciphers that use a non-uniformly distributed round function and apply the extended attack to the CAST family. This attack demonstrates that the round function of a Feistel cipher with six to eight rounds needs to be surjective and sufficiently uniform.
Similar content being viewed by others
References
C.M. Adams and S.E. Tavares, Designing S-boxes for ciphers resistant to differential cryptanalysis, Proc. of the 3rd symposium on State and Progress of Research in Cryptography, W. Wolfowicz, Ed., Fondazione Ugo Bordoni, 1993, pp. 181–190.
C.M. Adams, Simple and effective key scheduling for symmetric ciphers, Workshop on Selected Areas in Cryptography, pp. 129–133, Queen's University, Kingston, Ontario, Canada, May 1994.
K.G. Beauchamp, Walsh Functions and Their Applications, Academic Press, New York, 1975.
E. Biham and A. Shamir, Differential Cryptanalysis of the Data Encryption Standard, Springer-Verlag, 1993.a
A. Bosselaers, propriety DES software, KULeuven.
W. Diffie and M. Hellman, Exhaustive cryptanalysis of the NBS data encryption standard, Computer, pp. 74–78, 1977.
H. Feistel, W.A. Notz, and J.L. Smith, “Some cryptographic techniques for machine-to-machine data communications,” Proc. IEEE, Vol. 63,No. 11, November 1975, pp. 1545–1554.
Data Encryption Standard, Federal Information Processing Standard (FIPS), Publication 46, National Bureau of Standards, U.S. Department of Commerce, Washington D.C., January 1977.
H.M. Heys and S.E. Tavares, On the security of the CAST encryption algorithm, Canadian Conference on Electrical and Computer Engineering, pp. 332–335, Sept. 1994, Halifax, Canada.
L.R. Knudsen, Block ciphers — analysis, design and applications, PhD. Thesis, DAIMI PB-485, Aarhus University, 1994.
L. Brown, M. Kwan, J. Pieprzyk and J. Seberry, Improving resistance against differential cryptanalysis and the redesign of LOKI, Advances in Cryptology, Proc. AsiaCrypt'91, LNCS 453, H. Imai, R. L. Rivest and T. Matsumoto, Eds., Springer-Verlag, 1993, pp. 36–50.
M. Matsui, Linear cryptanalysis method for DES cipher, Advances in Cryptology, Proc. Eurocrypt'93, LNCS 765, T. Helleseth, Ed., Springer-Verlag, 1994, pp. 386–397.
M. Matsui, The first experimental cryptanalysis of the Data Encryption Standard, Advances in Cryptology, Proc. Crypto'94, LNCS 839, Y. Desmedt, Ed., Springer-Verlag, 1994, pp. 1–11.
S. Miyaguchi, The Feal cipher family, Advances in Cryptology, Proc. Crypto'90, LNCS 537, S. Vanstone, Ed., Springer-Verlag, 1991, pp. 627–638.
B. Schneier, Description of a new variable-length key, 64-bit block cipher (Blowfish), Fast Software Encryption, LNCS 809, R. Anderson, Ed., Springer-Verlag, 1994, pp. 191–204.
T. Tokita, T. Sorimachi, and M. Matsui, “Linear cryptanalysis of LOKI and s 2DES,” Advances in Cryptology, Proc. Asiacrypt'94, LNCS, J. Pieprzyk, Ed., Springer-Verlag, to appear.293303
Wiener, M., 1993, Efficient DES key search, presentation at Rump Session of Crypto (August, 1993), Santa Barbara, CA. Available as TR-244, School of Computer Science, Carleton University, Ottawa, Canada, May 1994.
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Rijmen, V., Preneel, B. & De Win, E. On Weaknesses of Non–surjective Round Functions. Designs, Codes and Cryptography 12, 253–266 (1997). https://doi.org/10.1023/A:1008224928678
Issue Date:
DOI: https://doi.org/10.1023/A:1008224928678